Apple Expands iOS 18.7.7 Update to More Devices to Shield Users
Apple significantly expanded the availability of iOS 18.7.7 and iPadOS 18.7.7 on April 1, 2026. This unusual move pushes critical backported security patches to a broader set of devices, targeting...
Apple significantly expanded the availability of iOS 18.7.7 and iPadOS 18.7.7 on April 1, 2026. This unusual move pushes critical backported security patches to a broader set of devices, targeting millions of users still running iOS 18 who remain exposed to DarkSword. The sophisticated, web-delivered exploit chain is capable of silently stealing vast amounts of sensitive user data
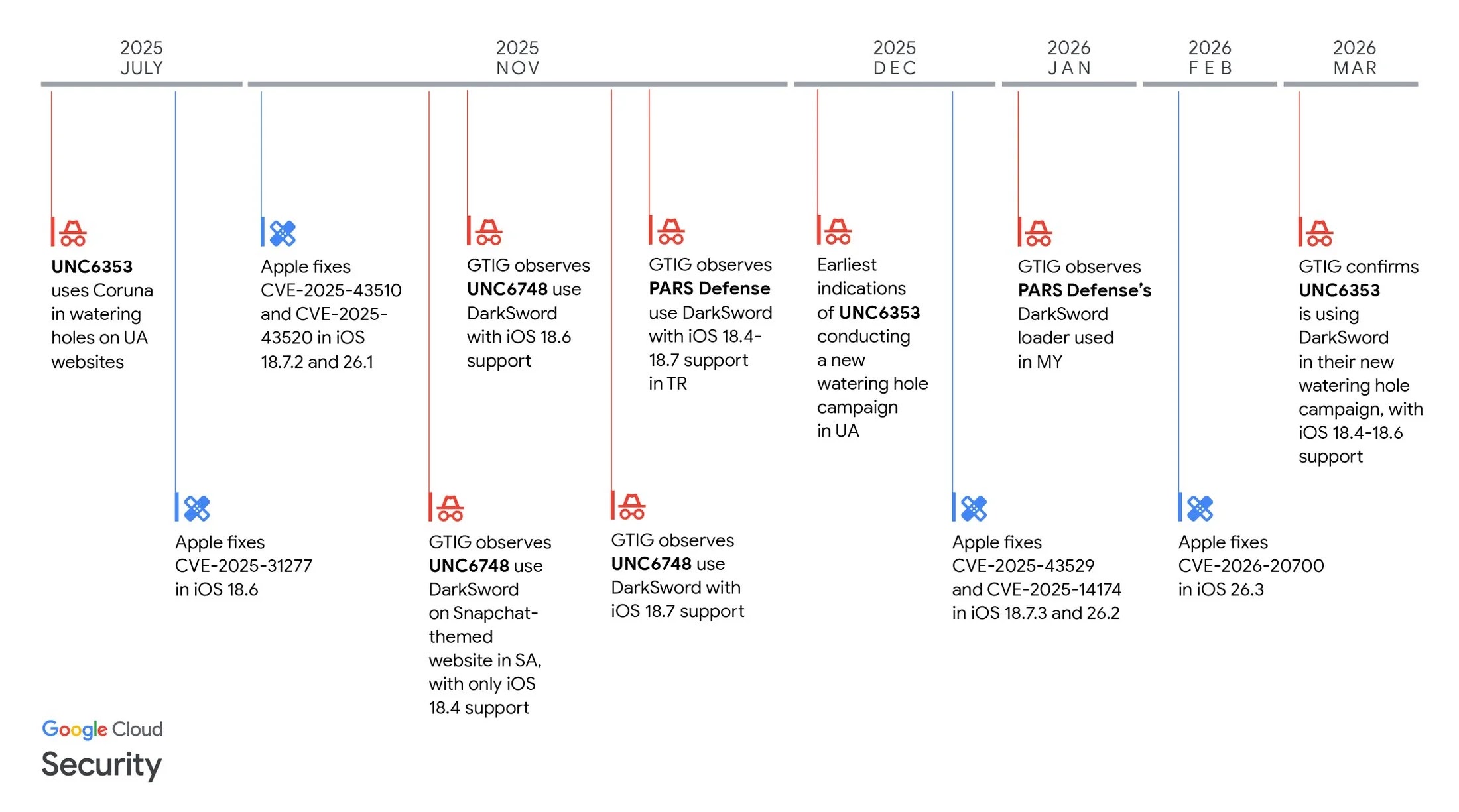
DarkSword is a fully weaponized iOS exploit kit, first identified in active campaigns as far back as November 2025 by Google’s Threat Intelligence Group (GTIG), iVerify, and Lookout.
The toolkit specifically targets devices running iOS 18.4 through 18.7, leveraging a chain of six distinct vulnerabilities including bugs in JavaScriptCore, dyld, and the iOS sandbox to achieve full kernel-level code execution without any user interaction beyond a single website visit.
Once deployed, DarkSword exfiltrates passwords, messages, browser history, location data, cryptocurrency wallet contents, and even Apple Health data within seconds before wiping its own traces.
In March 2026, the DarkSword toolkit was publicly leaked on GitHub, dramatically lowering the barrier for less sophisticated threat actors to weaponize it. Multiple commercial surveillance vendors and suspected state-sponsored actors had already deployed it against targets in Saudi Arabia, Turkey, Malaysia, and Ukraine.
Apple’s Update for DarkSword Exploit
iOS 18.7.7 was initially released on March 24, 2026, but Apple extended its availability to a wider device pool on April 1, 2026, specifically citing the DarkSword threat.
This is an unusual policy shift; Apple has historically required users to upgrade to the latest major iOS release to receive security fixes. The company confirmed that the underlying DarkSword patches originally shipped in 2025 but are now being backported to protect the approximately 20% of users still on iOS 18.
The update patches 20+ vulnerabilities spanning critical system components:
- 802.1X (CVE-2026-28865) — An authentication flaw enabling privileged network attackers to intercept traffic, fixed via improved state management; discovered by Héloïse Gollier and Mathy Vanhoef of KU Leuven
- Kernel (CVE-2026-20687) — A use-after-free bug allowing apps to cause unexpected system termination or write to kernel memory, reported by Johnny Franks (@zeroxjf)
- Kernel (CVE-2026-28867 / CVE-2026-28868) — Two separate flaws leaking sensitive kernel state and kernel memory, discovered by Jian Lee (@speedyfriend433) and Lee Dong Ha of BoB 0xB6
- Security Framework (CVE-2026-28864) — A permissions flaw granting local attackers access to Keychain items, reported by Alex Radocea
- WebKit (CVE-2026-28861, CVE-2026-20643, CVE-2026-20665, CVE-2026-28871) — Multiple browser-engine bugs enabling cross-site scripting, Same Origin Policy bypass, Content Security Policy evasion, and cross-origin script handler access via maliciously crafted web content
- AppleKeyStore (CVE-2026-20637) — A use-after-free flaw enabling unexpected system termination
- CoreMedia (CVE-2026-20690) — An out-of-bounds access bug triggered by malicious audio streams in media files, found by Hossein Lotfi of Trend Micro Zero Day Initiative
- iTunes Store (CVE-2025-43534) — A path handling flaw allowing physical-access bypass of Activation Lock
- curl (CVE-2025-14524) — An open-source vulnerability causing unintended transmission of sensitive data over incorrect connections
The update applies to a broad range of devices, including iPhone XR through iPhone 16e, and a wide range of iPad models from the 5th-generation iPad mini to iPad Pro M4. Users with Automatic Updates enabled will receive iOS 18.7.7 automatically.
Apple has additionally confirmed that its Lockdown Mode feature provides protection against DarkSword for high-risk users who need enhanced hardening.
For comprehensive long-term protection, Apple continues to recommend upgrading to iOS 26.3 or later, where all DarkSword-related vulnerabilities have been fully addressed.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.