Android Banking Malware Hijacks Accounts via Fake KYC
A new Android banking malware, designated KYCShadow, is actively targeting Indian bank customers by exploiting a meticulously crafted fake Know Your Customer (KYC) verification workflow. Details of...
A new Android banking malware, designated KYCShadow, is actively targeting Indian bank customers by exploiting a meticulously crafted fake Know Your Customer (KYC) verification workflow. Details of this threat were recently published in a
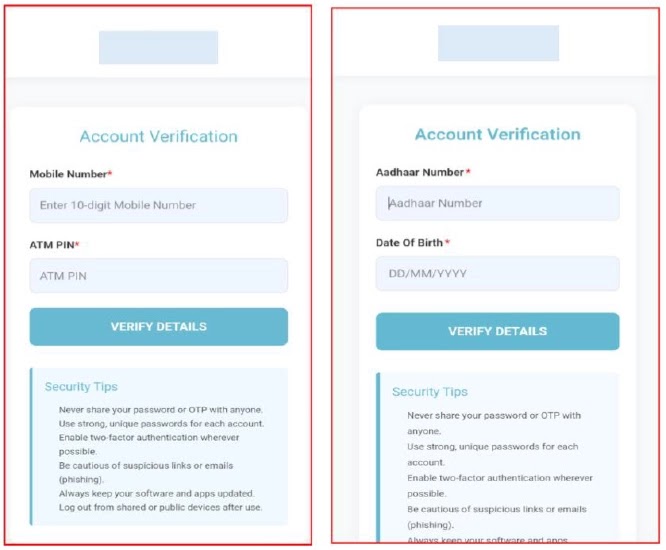
The application presents itself as a trusted banking KYC service, exploiting a routine process that millions of Indian bank users are already familiar with.
Once installed, it guides users through convincing verification screens that collect mobile numbers, ATM PINs, Aadhaar numbers, and card details one step at a time.
After users complete the flow, a fake confirmation message claims that “verification is in progress,” while all submitted data is already being transmitted to a remote attacker-controlled server at jsonapi[.]biz.
Cyfirma researchers identified this campaign in April 2026 and noted that KYCShadow is engineered as a two-stage dropper.
The first application victims install acts as a loader that silently decrypts and deploys a secondary malicious payload in the background, keeping the most capable components hidden during the initial phase to avoid early detection.
Once the secondary payload is active, it requests permissions covering SMS access, phone call control, and battery optimization exemption.
These allow the malware to intercept OTPs in real time, send and forward SMS messages remotely, place phone calls without user input, and continue operating in the background even while the device is idle.
The payload also hides itself from the device app launcher, leaving no visible trace on the infected phone.
Adding to the risk, the malware activates a full-tunnel VPN service that routes all device traffic through an attacker-controlled layer.
This gives the threat actor the ability to monitor, filter, or block outbound connections to security services, reducing the device’s capacity to detect or report the infection.
Multi-Stage Infection Mechanism
The infection starts the moment the dropper application is launched, showing a deceptive “Update Required” screen with a single button labeled “Install Update,” crafted to resemble a standard system prompt that most users would tap without question.
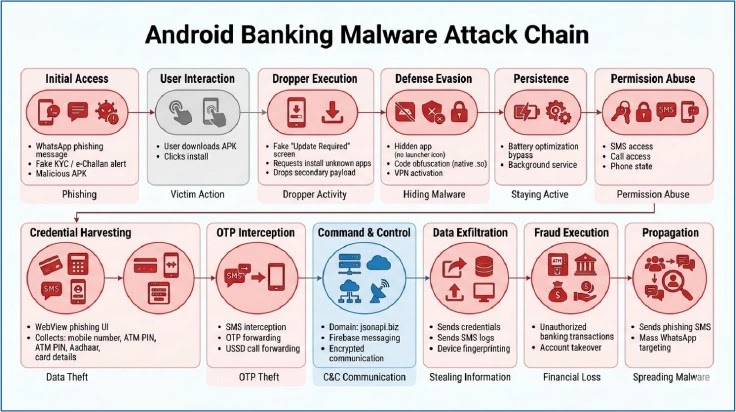
Clicking the button triggers a VPN connection request, followed by a prompt to allow installation of apps from unknown sources.
Once both approvals are given, the dropper begins decrypting an embedded payload using an XOR-based algorithm tied specifically to its own package name.
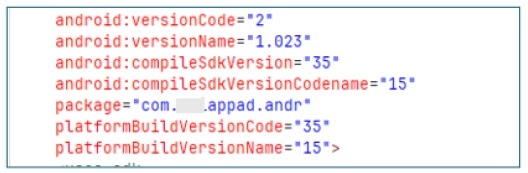
This means the payload cannot be extracted or analyzed without knowing both the exact package name and the decryption logic, making the process considerably harder for security researchers.
The decrypted file is written to temporary internal storage and installed silently through Android’s PackageInstaller API with no additional user interaction.
The secondary payload, identified as com.am5maw3.android, launches in the background and immediately suppresses its own launcher icon to remain hidden.
It registers with Firebase Cloud Messaging, establishing a persistent push-based remote command channel for the attacker.
Supported commands include real-time SMS interception, bulk inbox extraction, remote call placement, and USSD-based call forwarding, all executed without producing any visible signs on the infected device.
Users should not install applications received via WhatsApp, SMS, or messaging channels, especially those claiming to offer banking or KYC updates.
Always download banking apps from official sources, keep the “Install Unknown Apps” permission disabled, and never enter credentials or card details into unverified interfaces.
Any unexpected VPN prompts, unfamiliar permission requests, or unusual SMS activity should be reported to the concerned bank without delay.
Financial institutions and security teams should immediately block traffic to jsonapi[.]biz, jsonserv[.]biz, and jsonserv[.]xyz at the network level.
Deploying mobile threat defense solutions that detect staged dropper behavior, unauthorized permission usage, and hidden app payloads will help organizations respond more quickly to campaigns of this nature.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.