Advanced iOS Exploit: iPhone Hacking Ste With Tools
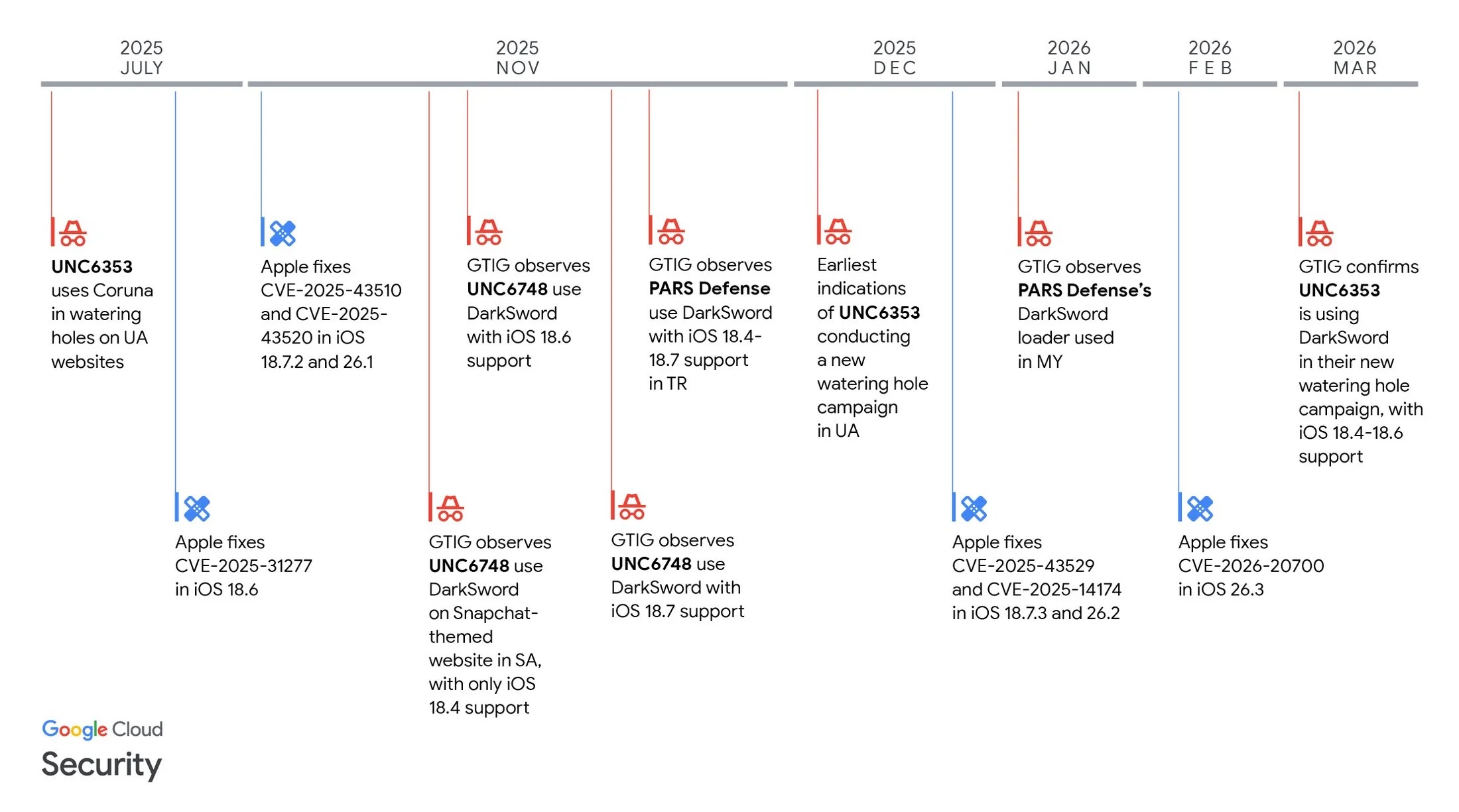
A sophisticated full-chain iOS exploit kit, dubbed DarkSword, has been actively deployed by multiple commercial surveillance vendors and state-sponsored threat actors since at least November 2025....
A sophisticated full-chain iOS exploit kit, dubbed DarkSword, has been actively deployed by multiple commercial surveillance vendors and state-sponsored threat actors since at least November 2025. Its purpose is to steal sensitive personal data from iPhone users across four countries.
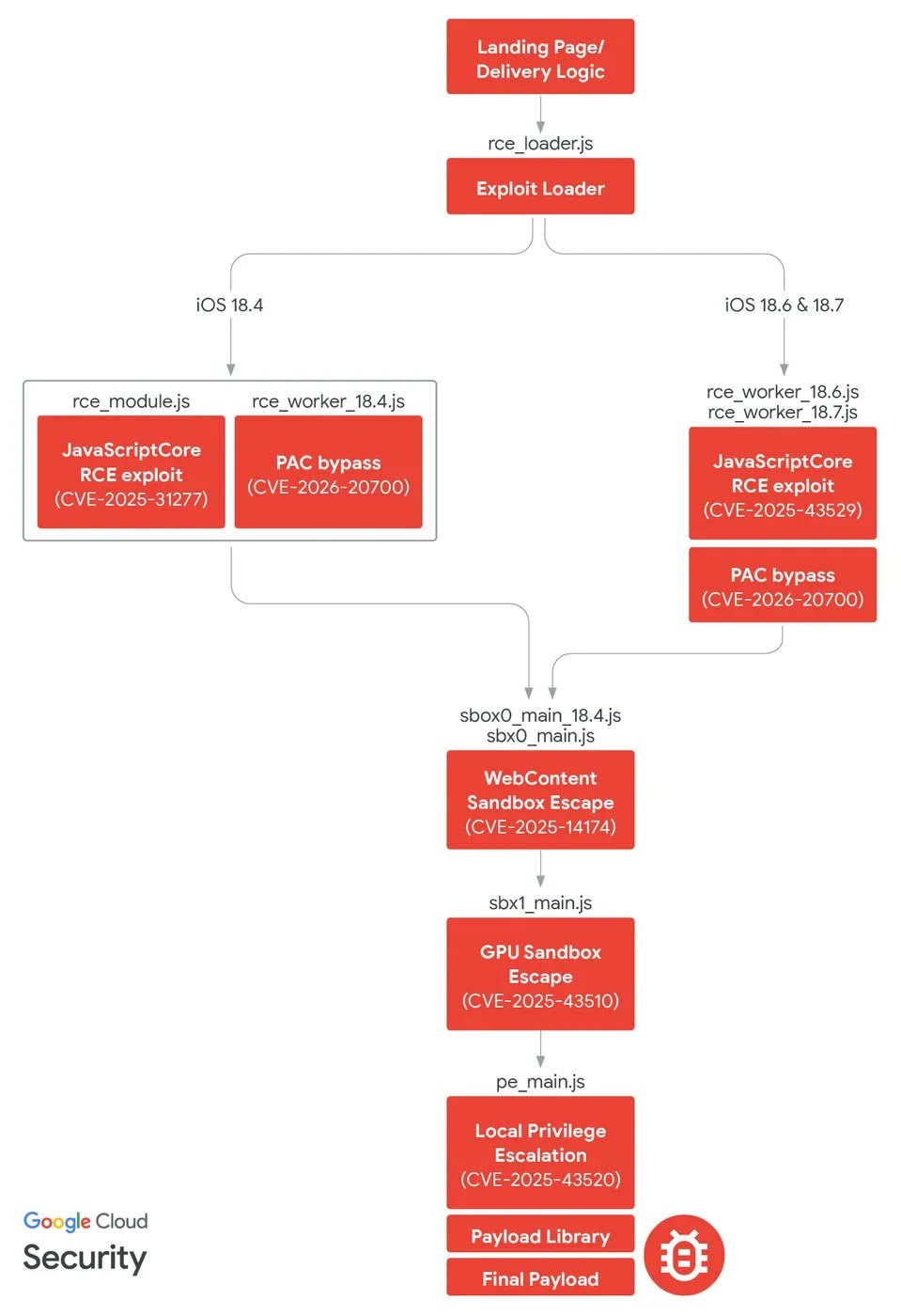
DarkSword is a full-chain iOS exploit that chains six distinct vulnerabilities, four of which were leveraged as zero-days, to achieve complete device compromise on iPhones running iOS versions 18.4 through 18.7.
The exploit chain operates entirely in JavaScript, allowing attackers to bypass Apple’s Page Protection Layer (PPL) and Secure Page Table Monitor (SPTM) mitigations that would otherwise block unsigned native binary code from executing.
GTIG, iVerify, and Lookout analyzed the exploit chain’s name based on toolmarks embedded in recovered payloads and have confirmed its use in targeted campaigns against victims in Saudi Arabia, Turkey, Malaysia, and Ukraine.
Six-Vulnerability iOS Exploit Chain
The six-vulnerability chain begins with a remote code execution (RCE) exploit targeting JavaScriptCore, Apple’s JavaScript engine used in Safari and WebKit, and progresses through two sandbox escape stages, a local privilege escalation, and a final payload deployment that grants attackers full kernel-level privileges.
CVE-2026-20700, a Pointer Authentication Code (PAC) bypass in Apple’s dyld dynamic linker, was chained directly with both RCE exploits and patched only with iOS 26.3 after GTIG reported it to Apple
| CVE | Exploit Module | Vulnerability Type | Affected Component | Zero-Day | Patched In |
|---|---|---|---|---|---|
| CVE-2025-31277 | rce_module.js |
JIT optimization / type confusion | JavaScriptCore (WebKit) | No | iOS 18.6 |
| CVE-2025-43529 | rce_worker_18.6.js, rce_worker_18.7.js |
Use-after-free / garbage collection bug in DFG JIT layer | JavaScriptCore (WebKit) | Yes | iOS 18.7.3, 26.2 |
| CVE-2026-20700 | rce_worker_18.4.js, rce_worker_18.6.js, rce_worker_18.7.js |
Memory corruption / user-mode PAC bypass | dyld (Dynamic Linker) |
Yes | iOS 26.3 |
| CVE-2025-14174 | sbox0_main_18.4.js, sbx0_main.js |
Out-of-bounds memory access in WebGL operation | ANGLE (GPU process / WebKit) | Yes | iOS 18.7.3, 26.2 |
| CVE-2025-43510 | sbx1_main.js |
Memory management / copy-on-write bug | XNU Kernel | No | iOS 18.7.2, 26.1 |
| CVE-2025-43520 | pe_main.js |
Kernel-mode race condition in VFS implementation | XNU Kernel (Virtual Filesystem) | No | iOS 18.7.2, 26.1 |
GTIG identified three distinct post-exploitation malware families deployed after a successful DarkSword compromise, each tailored to specific threat actor needs.
GHOSTKNIFE, deployed by threat cluster UNC6748 via a Snapchat-themed phishing site (snapshare[.]chat), is a JavaScript backdoor capable of exfiltrating signed-in accounts, messages, browser data, location history, and audio recordings from the device’s microphone.
It communicates with its command-and-control (C2) server over a custom binary protocol encrypted with ECDH and AES, and actively deletes crash logs from the device to evade forensic detection.
GHOSTSABER, deployed by Turkish commercial surveillance vendor PARS Defense in campaigns targeting Turkey and Malaysia, supports over 15 distinct C2 commands, including device enumeration, file exfiltration, arbitrary SQLite query execution, and photo thumbnail uploads.
Several GHOSTSABER commands, including audio recording and real-time geolocation, are not yet fully implemented in the JavaScript implant itself, suggesting follow-on binary modules are downloaded at runtime from the C2 server.
GHOSTBLADE, attributed to suspected Russian espionage actor UNC6353, functions as a comprehensive data miner exfiltrating iMessages, Telegram, and WhatsApp data, cryptocurrency wallet data, Safari history and cookies, Health databases, device keychains, location history, and saved Wi-Fi passwords.
Unlike the other two families, GHOSTBLADE does not operate persistently or support interactive backdoor commands, but its breadth of data collection makes it highly valuable for intelligence-gathering operations. Notably, GHOSTBLADE’s library code contains a reference to a function named startSandworm() that remains unimplemented — possibly a codename for a separate, forthcoming exploit.
UNC6748 delivered DarkSword through a fraudulent Snapchat lookalike site, using obfuscated JavaScript loaders with anti-debugging protections and session storage fingerprinting to avoid re-infecting the same victims.
PARS Defense upgraded its delivery mechanism to encrypt exploit stages using ECDH key exchange between the attacker infrastructure and the victim device, demonstrating heightened operational security awareness.
UNC6353 — a suspected Russian espionage group previously linked to the Coruna iOS exploit kit, embedded malicious <script> tags into compromised Ukrainian websites, loading DarkSword silently via hidden iFrames.
Tellingly, a comment in UNC6353’s source code was written in Russian, and GTIG has been working with CERT-UA to mitigate this ongoing campaign active through March 2026.
GTIG reported all DarkSword vulnerabilities to Apple in late 2025, and all six CVEs have since been patched the majority prior to, and the remainder with the release of iOS 26.3.
Google has also added all identified DarkSword delivery domains to Safe Browsing. Users are strongly urged to update to the latest version of iOS immediately; if updates are not available, enabling Lockdown Mode is recommended as an additional safeguard against this class of exploit.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.