Google reCAPTCHA Update Blocks Privacy-Focused Android
Google recently deployed a significant update to its reCAPTCHA verification system. This change fundamentally alters how websites verify human traffic. Announced on April 22 at the Google Cloud Next...
Google recently deployed a significant update to its reCAPTCHA verification system. This change fundamentally alters how websites verify human traffic.
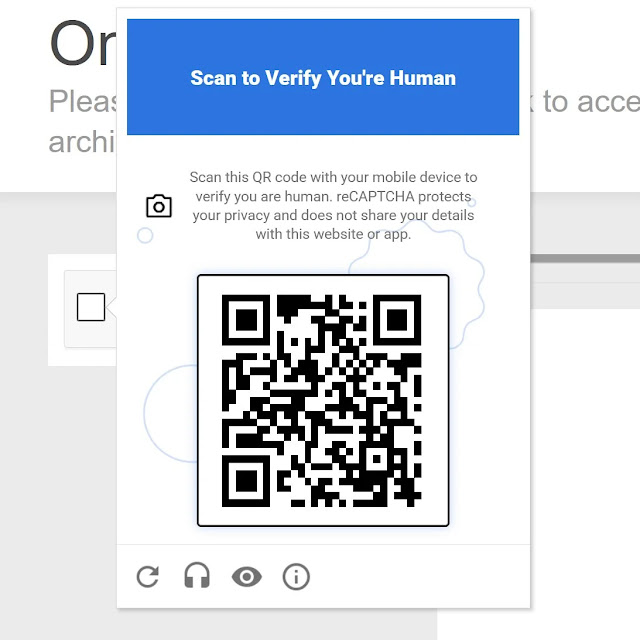
Announced on April 22 at the Google Cloud Next 2026 conference, the new mechanism operates through Google’s Cloud Fraud Defense tool and introduces a mandatory QR code challenge for suspicious traffic.
While designed to combat sophisticated AI bots, this update effectively blocks users operating privacy-focused, de-Googled Android operating systems from accessing large portions of the web.
First reported by Android Authority on May 7, the architectural shift came to light after a Reddit user discovered an updated Google support page.
Google reCAPTCHA Update
Under the new policy, Android devices must run Google Play Services version 25.41.30 or higher to successfully complete the reCAPTCHA mobile verification flow. When the Cloud Fraud Defense system detects suspicious web traffic, it now bypasses the traditional image-based puzzles that internet users have grown accustomed to solving.
Instead, the system presents a QR code that users must scan with their smartphone camera to prove human interaction.
For the vast majority of Android users utilizing factory-installed software, this verification process happens seamlessly since Google Play Services is pre-installed and auto-updating.
The reliance on this specific application suite means the verification process heavily utilizes hardware attestation, tying basic web accessibility directly to Google’s proprietary mobile ecosystem rather than simple behavioral analysis.
This mandatory integration with Google Play Services acts as a digital brick wall for the growing community of privacy advocates.
Users who intentionally flash their devices with custom, de-Googled operating systems like GrapheneOS, CalyxOS, and /e/OS are explicitly excluded from this new verification flow.
These operating systems are specifically engineered to prioritize user security and severely limit corporate data tracking by stripping out Google’s background services entirely.
According to developers at GrapheneOS, this reCAPTCHA update aggressively pushes hardware attestation, sidelining open-source alternatives. By tethering basic web navigation to a specific version of Play Services, privacy-focused users are effectively punished for securing their data.
They are rendered unable to pass standard security checks on countless websites that rely on Google’s widespread verification infrastructure, severely limiting their ability to browse the internet normally.
Google defends the architectural shift as a necessary evolution to stop advanced AI bots and widespread online fraud.
As automated threats become highly proficient at solving traditional image puzzles, the company argues that hardware-level verification is the most reliable method to confirm authentic human identity.
However, cybersecurity critics and open-source advocates argue this move exerts monopolistic control over the internet by forcing adoption of Google’s proprietary tracking software.
The security community is increasingly urging website administrators to migrate away from Google’s ecosystem and adopt alternative, less restrictive verification services like hCaptcha to ensure open web access.
For the time being, users locked out by the QR code challenge can rely on a temporary workaround by selecting the audio challenge option when presented with a reCAPTCHA prompt.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.