MajorDoMo RCE Vulnerability Exposes Servers Code Execution
A newly disclosed vulnerability exposes internet-facing MajorDoMo servers to unauthenticated remote code execution. The flaw stems from a broken authentication flow and unsafe dynamic PHP evaluation....
A newly disclosed vulnerability exposes internet-facing MajorDoMo servers to unauthenticated remote code execution. The flaw stems from a broken authentication flow and unsafe dynamic PHP evaluation.
The vulnerability (CVE-2026-27174) stems from the /admin.php request flow, where improper handling of unauthorized access allows execution to continue even after a redirect, effectively bypassing access controls.
That continued execution exposes an internal AJAX console handler that passes attacker-controlled input directly into PHP’s eval() function, turning a single crafted HTTP request into full server-side code execution on exposed MajorDoMo instances.
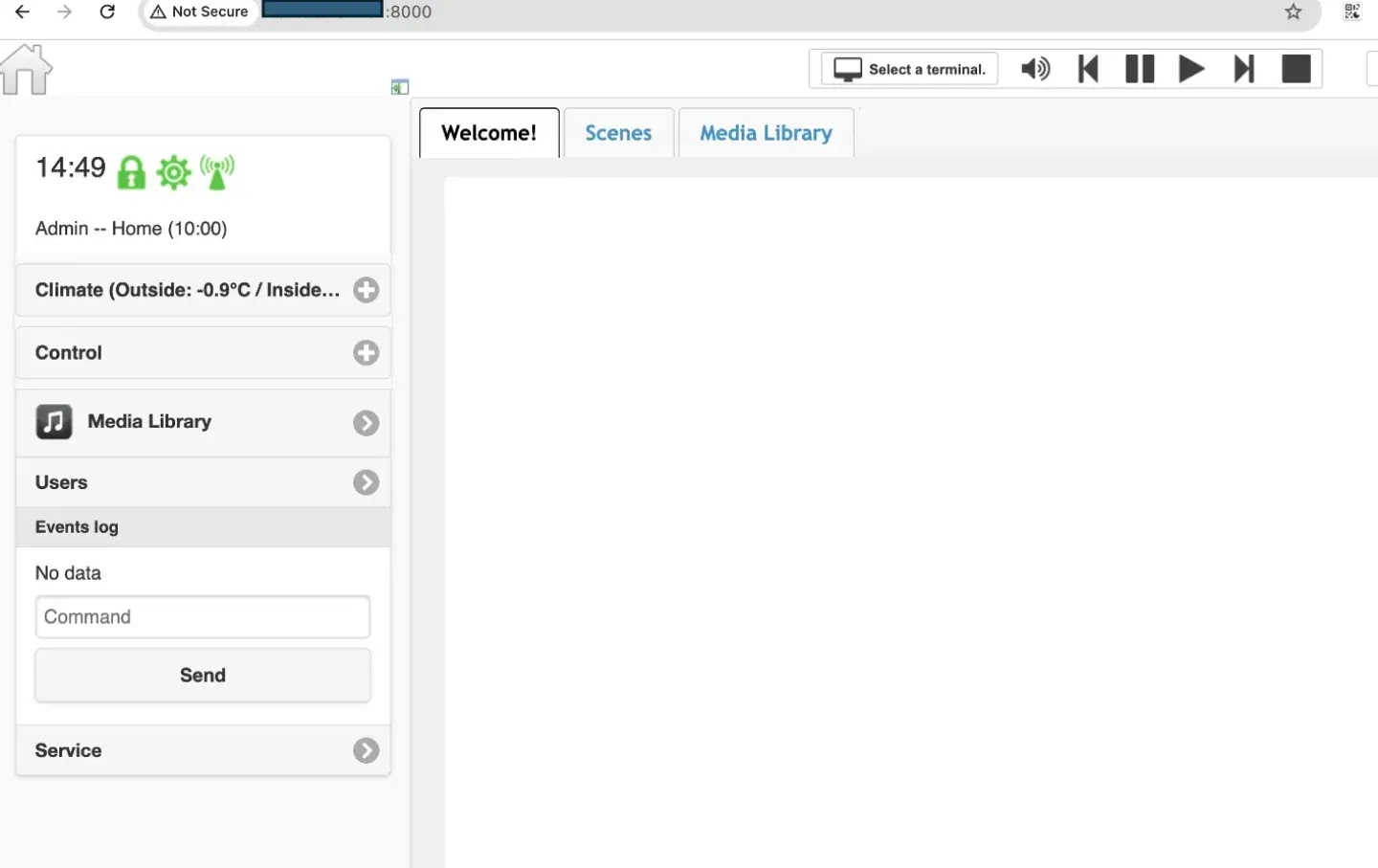
Because MajorDoMo often manages cameras, sensors, automation routines, and other internal IoT services, successful exploitation can quickly escalate from web compromise to wider smart-environment and network exposure.
Exploitation Mechanics and Attack Chain
Exploiting this architectural oversight requires only a single, specially crafted HTTP GET request directed at the exposed administrative interface.
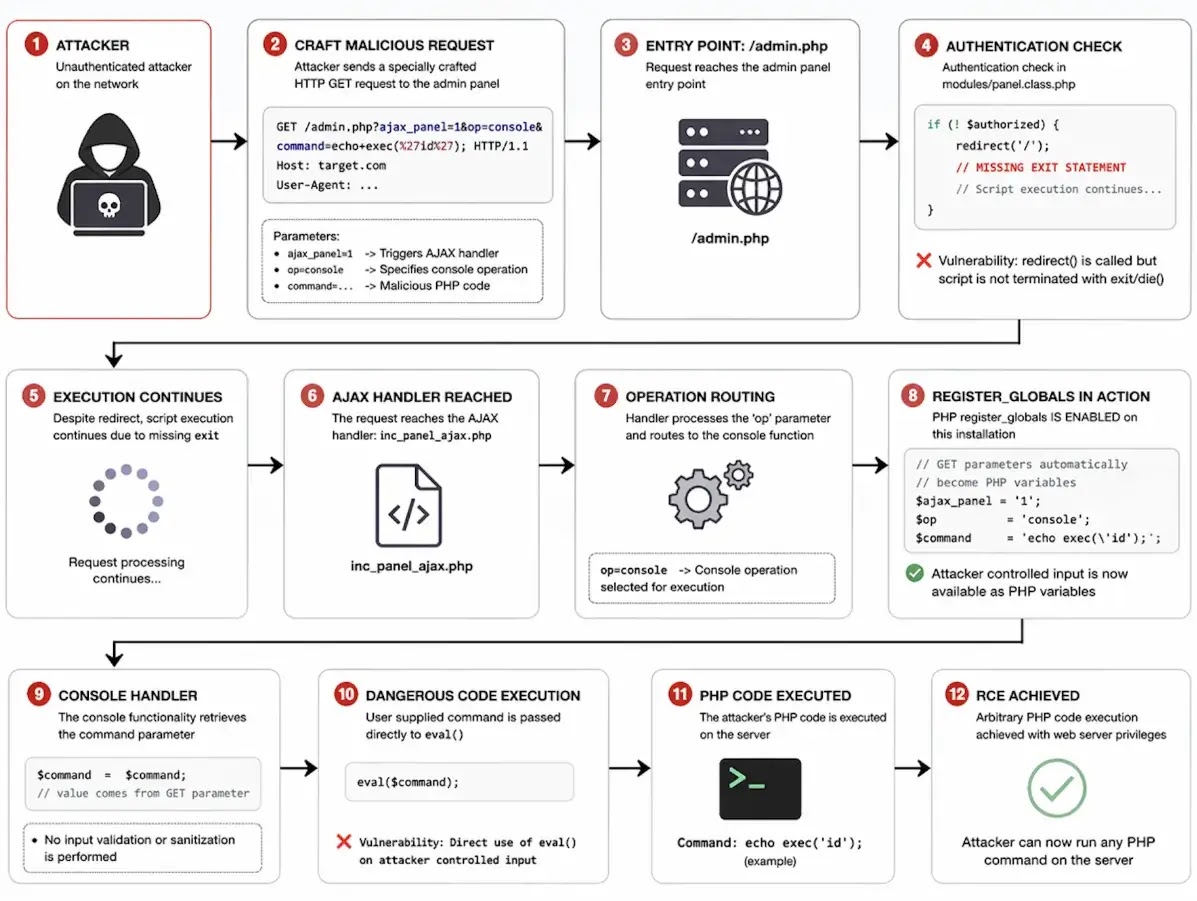
Threat actors can trigger the vulnerability by passing specific routing variables, namely selecting the internal console operation and supplying their malicious payload through the command parameter.
Even though the server returns a redirect response to the client, the backend interpreter continues to process the injected payload and executes arbitrary PHP instructions.
This grants attackers unrestricted access to the application environment, allowing them to run system-level commands, read sensitive configuration files, and establish persistent backdoor access by writing web shells to the underlying file system.
As reported by Resecurity, the vulnerability is already covered by a publicly available detection template in the ProjectDiscovery Nuclei repository, signaling a heightened risk of rapid exploitation against exposed smart-home systems.
Because MajorDoMo frequently serves as the central orchestration engine for IoT devices, cameras, and private automation networks, the impact of this remote code execution flaw extends far beyond the immediate web application.
Security researchers warn that a compromised host can be weaponized as a strategic foothold, enabling threat actors to intercept surveillance feeds, extract stored network credentials, and pivot laterally into deeper, better-protected segments of the internal network.

To mitigate this severe threat, administrators must urgently restrict administrative panel access to trusted internal IP addresses and deploy the platform behind a secure virtual private network or an advanced reverse proxy authentication gateway.
Organizations should proactively audit their system logs for unexpected console operations and apply the latest vendor patches to eliminate unsafe dynamic code-execution pathways permanently.
Indicators of Compromise (IoCs)
| Type | Indicator Details |
|---|---|
| Network | HTTP GET requests to /admin.php with parameters like ajax_panel, op, and command from external or untrusted IPs. |
| Network | Unusual outbound connections from the server hosting MajorDoMo, potentially indicating C2 or data exfiltration. |
| Host | Suspicious child processes spawned by the web server (e.g., www-data, apache), suggesting remote command execution. |
| Host | Unexpected PHP files, web shells, or backdoors in web-accessible or temporary directories, indicating compromise. |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.