Education Sector Under Attack: Espionage & Phishing
The global education sector, encompassing schools, universities, and research institutions, faces an escalating wave of cyber threats in 2026. State-backed espionage groups, sophisticated...
The global education sector, encompassing schools, universities, and research institutions, faces an escalating wave of cyber threats in 2026. State-backed espionage groups, sophisticated spear-phishing campaigns, and complex supply chain attacks are placing these vital organizations on high alert, according to a new report outlining these critical challenges.
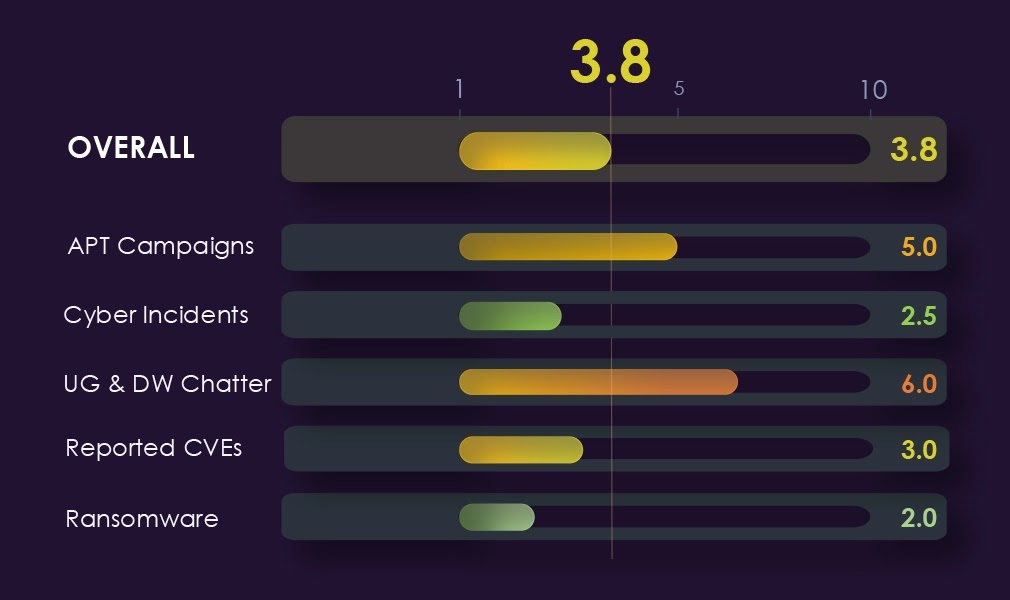
Data from Q1 2026 shows that the education sector appeared in 20% of all observed advanced persistent threat (APT) campaigns, a sharp rise from zero in the previous quarter.
The most alarming shift this period is the entry of state-sponsored threat actors into a sector that was previously absent from their target list.
All observed APT campaigns tied to education institutions carry an exclusively state-sponsored profile, with no financially motivated actors involved.
China-linked groups lead the charge, with MISSION2074 running four campaigns, followed by Stone Panda, Hafnium, and Lotus Blossom.
Iran-linked Charming Kitten is the only non-Chinese state actor observed, and its activity aligns with known Iranian interest in targeting academic and research institutions across the Middle East, including Gulf states such as Saudi Arabia, Qatar, Kuwait, Bahrain, and Oman.
Cyfirma analysts identified that victim distribution spans 27 countries, with the United States recording the highest victim count, followed by the United Kingdom, Japan, India, South Korea, and Germany.
The geographic spread is notably broader than in other sectors, with European countries featuring more prominently than in Asia-Pacific regions.
Myanmar and Hong Kong also appear in the mid-frequency tier, consistent with China-linked targeting patterns of diaspora communities and regional research institutions.
Beyond APT activity, reported cyber incidents during Q1 2026 point to supply chain attacks and spear-phishing as the primary attack techniques used against education organizations.
A total of 12 cyber incidents were tracked, representing a 1.49% share of all industry-linked incidents, placing education 10th out of 14 monitored sectors.
While this figure may appear low, researchers note that the numbers likely reflect under-reporting rather than an absence of risk, a concern reinforced by the volume of APT activity seen during the same period.
On the ransomware front, the education sector recorded 54 verified victims in Q1 2026, a 25% decline from 72 in the previous quarter. Universities and research institutes accounted for the majority of victims, followed by public schools and school districts.
Among active ransomware groups, Interlock stands out as the most focused actor, directing 27.3% of its total victims toward education organizations, a deliberate concentration that far exceeds the sector average of around 7% among gangs with more than two victims.
State Espionage and Targeted Technology Access
What separates the education sector from others this period is not just who is being attacked, but how and why.
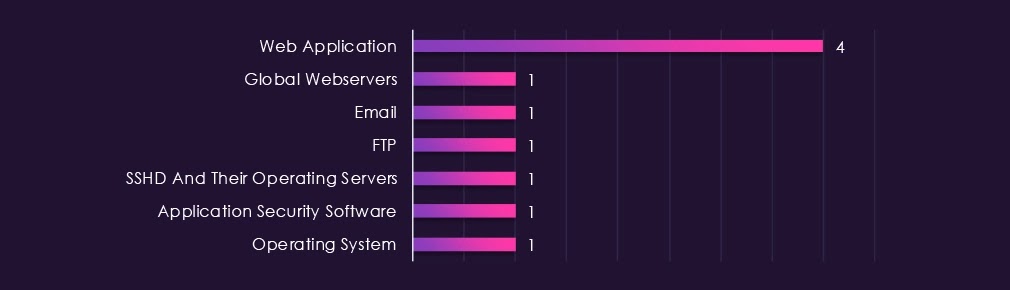
Unlike most industries where network infrastructure such as VPNs and routers are the primary targets, threat actors in the education space are going after email servers, FTP servers, and SSHD servers.
This technology profile points directly to one objective: accessing research data and institutional communications, rather than disrupting operational infrastructure.
The focus on intellectual property held by universities and research institutions makes this targeting pattern logical from a strategic espionage standpoint.
Academic institutions hold sensitive information ranging from government-funded research to defense-adjacent studies, making them high-value targets for nation-states seeking intelligence without direct confrontation.
Web applications recorded the highest number of observed attacks overall, though the margin over other categories was narrower compared to most other sectors, reinforcing that attackers are targeting communication channels as much as web-facing systems.
Dark web telemetry adds another layer of concern, with hacktivism-related mentions growing more than sevenfold, from 28 to 216, across the 90-day period.
DDoS-related chatter spiked dramatically in the final 30 days, jumping from just 9 mentions to 214, suggesting coordinated, ideologically motivated disruption campaigns running parallel to state espionage activity.
Based on findings from the Q1 2026 threat landscape, education organizations are advised to take the following steps to reduce their exposure:-
- Harden email, FTP, and SSHD server configurations and apply strict access controls, as these are the primary entry points observed in state-sponsored campaigns.
- Conduct regular security audits of third-party software and vendors to detect and respond to supply chain compromises early.
- Train staff and faculty to identify spear-phishing emails, particularly those impersonating institutional contacts or academic partnerships.
- Patch known vulnerabilities promptly, prioritizing Remote Code Execution (RCE) and injection-type CVEs, which peaked mid-quarter before declining.
- Monitor dark web channels for mentions of institutional data to detect early signs of a breach or planned attack.
- Implement multi-factor authentication (MFA) across all institutional platforms, especially research collaboration tools and administrative systems.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.