fast16′ Malware Sabotages Ultra- Capabilities Attacking
A recently exposed Early analysis shows that fast16 relies on a multi‑stage attack chain that begins with a component named svcmgmt.exe, which works as a carrier for the main payload. This binary...
Early analysis shows that fast16 relies on a multi‑stage attack chain that begins with a component named svcmgmt.exe, which works as a carrier for the main payload.
This binary coordinates installation of an accompanying kernel‑mode driver called fast16.sys, which extends the malware’s visibility and control into the operating system core.
Once both components are active, the malware can move laterally, deploy additional worm‑like modules, and prepare destructive or disruptive actions against select hosts in the environment, especially those linked to critical infrastructure or expensive operational assets.
SentinelOne analysts were the first to document and name fast16, linking together these artifacts and showing that they are part of a unified project rather than isolated samples.
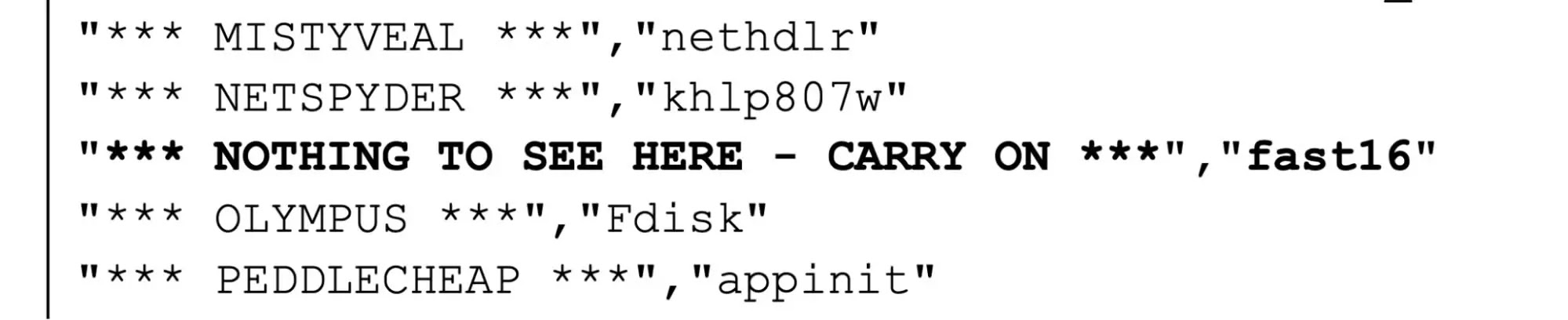
SentinelOne researchers describe fast16 as a sophisticated toolkit rather than a single binary, with its capabilities split between the driver, the management executable, and a Lua bytecode payload that is decrypted and run at runtime.
The Lua engine provides the operators with a flexible scripting layer, allowing them to script functions for propagation, sabotage, and stealth without constantly rebuilding the core binaries.
Embedded strings and configuration elements reference features like worm install routines, propagation controls, implant installation steps, and conditions under which the malware should avoid spreading too aggressively.
This careful design matches the needs of attackers who must balance persistence and control with the need to remain undetected in tightly monitored high‑value networks.
The attack vectors used by fast16 appear to center on existing access and abuse of management paths in already compromised environments, instead of simple mass‑phishing or drive‑by download campaigns.
The presence of signed or otherwise legitimate‑looking components, as well as detailed logic for installing services and drivers, suggests that the operators expect to work with elevated privileges on domain‑joined systems, possibly after using other tools and techniques to gain initial footholds.
Once running, the malware turns those footholds into a resilient presence that can patch security software, bypass local protections, and lay the groundwork for later sabotage operations against expensive infrastructure or specialized workstations.
The fast16-architecture in the original research illustrates the relationship between svcmgmt.exe, fast16.sys, and the Lua payload as part of this layered attack chain.
The operational impact of a fast16 intrusion can be severe because the malware is not only built to persist, but also to interfere with security controls and prepare for destructive actions on command.
Embedded configuration and code show that the authors anticipated encounters with various personal firewall and security products, checking for related registry keys and adapting behavior when such software is present.
On high‑value targets, this capability can translate into delayed detection of lateral movement, longer dwell times, and a higher chance that sabotage actions will succeed once finally triggered.
In environments supporting ultra‑expensive equipment or critical processes, that delay can be the difference between a contained incident and large‑scale operational downtime.
Deep dive into the fast16 infection and implant mechanism
At the core of the fast16 infection flow is the partnership between svcmgmt.exe as the user‑mode orchestrator and fast16.sys as the kernel‑mode driver that anchors the implant in the system.
The svcmgmt.exe component is responsible for tasks like copying payload files, setting up service entries, and preparing registry values that define how and when the malware should run.
SentinelOne’s analysis highlights a series of Lua function names inside the decrypted payload, including installworm, startworm, scmwormletinstall, scmwormletpropagatesystem, and oktopropagate, which together describe a staged approach to turning an initial foothold into a network‑aware implant with controlled propagation.
These functions help separate the high‑risk spread operations from core persistence so that the operators can tune how aggressively the malware moves within a network.
The implant pays particular attention to registry keys tied to personal firewalls and security products, checking paths under HKEY_LOCAL_MACHINE and HKEY_CURRENT_USER for signs of vendors such as ZoneAlarm, EZ Armor, and other firewall suites.
This check allows fast16 to decide whether to perform certain network operations or to adjust its propagation logic when host‑based controls might block or flag suspicious connections.
Alongside this defensive awareness, the driver fast16.sys hooks low‑level Windows functions and registers for file system events, enabling it to watch new processes, file creations, and storage activity while keeping its own components hidden.
In some builds, the project also includes a “cleanfast16patchtarget” module that appears to patch specific software modules, likely to disable or weaken competing protections and further entrench the implant in high‑value systems.
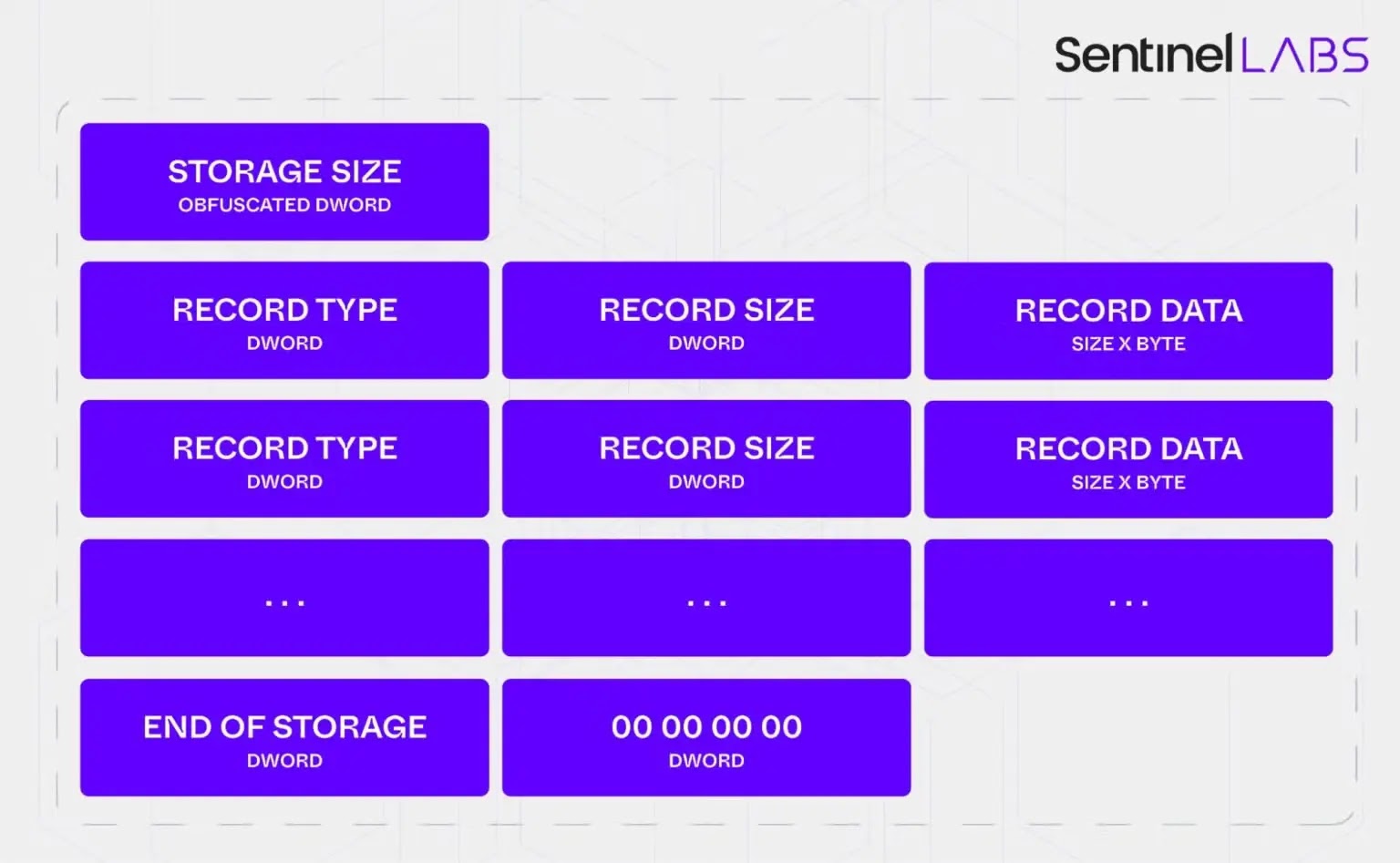
This outlines the progression from carrier execution to driver installation and Lua‑based wormlet activation across the victim environment.
Given the level of control and stealth provided by fast16, recommended defenses focus on strong driver‑loading policies, tight monitoring of service and driver creation events, and continuous scrutiny of registry changes linked to firewall and security product keys.
Network defenders should also maintain robust application control on management servers, watch for unusual instances of binaries named svcmgmt.exe, and deploy detection content aligned with the YARA rules for fast16’s Lua payload, driver, and patching code as disclosed by SentinelOne.
In high‑value environments, combining strict least‑privilege access, careful auditing of administrative actions, and regular integrity checks on security tooling will be essential to prevent fast16 from turning an initial compromise into a long‑term, sabotage‑ready presence.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.