Critical WordPress Plugin Flaw Grants Admin Access Bypass
A critical vulnerability in a widely deployed WordPress plugin jeopardizes thousands of websites globally. This serious flaw permits attackers to bypass authentication and gain unauthorized...
A critical vulnerability in a widely deployed WordPress plugin jeopardizes thousands of websites globally. This serious flaw permits attackers to bypass authentication and gain unauthorized administrative access, posing a significant threat to affected installations. Comprehensive details of the exploit are available in a recently published
Published on March 3, 2026, the vulnerability holds a CVSS v4.0 score of 9.8, placing it in the Critical severity category. It affects all versions of the User Registration & Membership plugin up to and including version 5.1.2.
The root cause is improper validation of user-controlled input combined with weak authorization checks inside the plugin’s backend processing logic.
The attack requires no special privileges, no user interaction, and can be carried out remotely over the internet.
CYFIRMA researchers identified and analyzed CVE-2026-1492, noting that the flaw centers on how the plugin handles trust between its public-facing frontend and internal backend.
Besides this, the CVE-2026-1492 has been marked as “Critical” severity and received CVSS score of 9.8.
The plugin relies on security tokens known as nonces, alongside AJAX-based workflows, to process membership-related requests.
These tokens are embedded in client-side JavaScript on publicly visible pages, making them accessible to anyone — even users who are not logged in.
By extracting these values, an attacker can craft a malicious request that triggers privileged backend actions and completely bypasses authentication.
The consequences of a successful attack are severe. Once the flaw is exploited, the attacker immediately gains full administrative control over the targeted WordPress site.
They can install or modify plugins, access and steal stored user data, alter website content, create hidden admin accounts, and plant backdoors for persistent future access.
A compromised site can also be turned into a platform for redirecting visitors to phishing pages or malware delivery sites, putting the site’s own users at direct risk.
Activity on underground forums shows that threat actors are already discussing and sharing techniques to exploit this vulnerability.
Initial Access Brokers may use it to gain admin access and resell entry points for downstream criminal activities such as ransomware deployment, credential theft, and SEO spam operations.
This level of active interest confirms that the threat is real and immediate attention from site administrators is critical.
Inside the Exploitation Workflow
The attack begins in a controlled environment where the vulnerable plugin is confirmed to be installed and running.
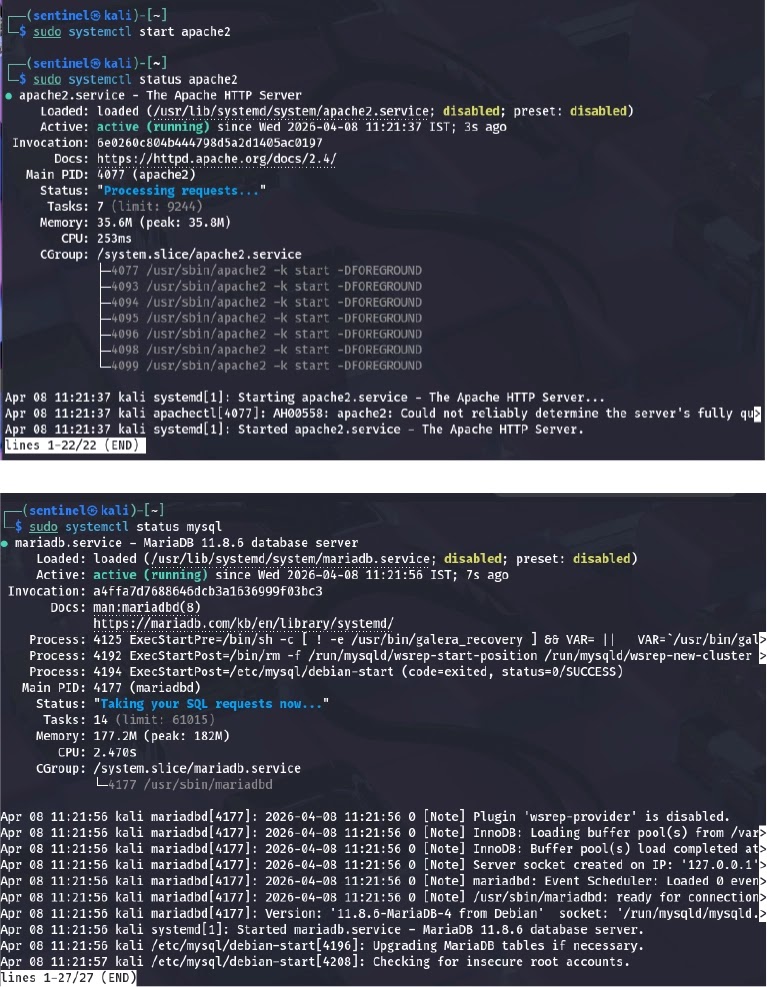
The attacker prepares the test setup before approaching the target. The publicly accessible membership pricing page is then identified as the main entry point into the site’s backend systems.
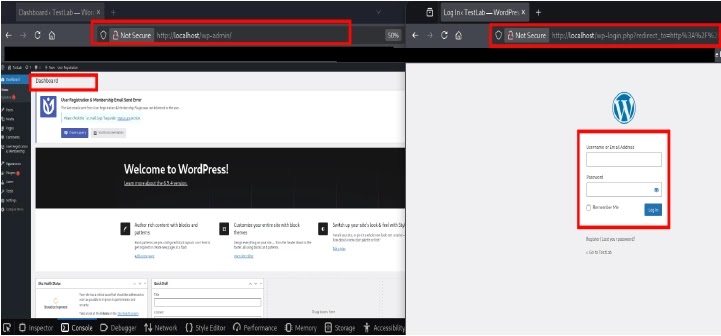
Using the browser’s developer tools, the attacker inspects the JavaScript on the membership page. This reveals nonce values and AJAX endpoint details that should never have been publicly accessible.
With these values in hand, a crafted payload is sent to the /wp-admin/admin-ajax.php endpoint. The backend processes the request without checking whether the sender is authorized.
The server then logs the attacker in and redirects the session to the WordPress admin dashboard, without a single valid credential used.
The most important action is to immediately update the User Registration & Membership plugin to version 5.1.3, where the vulnerability has been fixed.
After patching, all administrator accounts should be reviewed, and any accounts created without proper authorization must be removed. Sessions tied to suspicious accounts should be invalidated, and unknown credentials reset right away.
Organizations should also enforce strict server-side validation for all user-supplied input, especially values tied to role assignment. Access to sensitive endpoints like /wp-admin/admin-ajax.php must be tightly controlled, and internal security tokens should never be exposed in publicly accessible pages.
The principle of least privilege should be applied across all user roles, and continuous monitoring for abnormal AJAX requests or unexpected privilege escalations must remain active at all times.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.