Microsoft Warns Storm-1175 Exploits Web-Facing Assets 0-Day Flaws
Organizations face a critical new threat from a high-tempo ransomware campaign, according to a recent warning from Storm-1175 has built its operations around one approach — striking during the short...
Organizations face a critical new threat from a high-tempo ransomware campaign, according to a recent warning from
Storm-1175 has built its operations around one approach — striking during the short gap between when a software flaw is publicly disclosed and when IT teams patch it.
Security professionals call these “N-day” vulnerabilities: flaws that have been announced but remain unpatched across many systems.
The group scans for internet-exposed applications, including file transfer tools and mail servers, still running vulnerable versions. Even a few days of exposure is enough for attackers to gain entry.
Microsoft Threat Intelligence analysts identified Storm-1175 as responsible for these campaigns, tracking the group since 2023. Researchers noted the group exploiting over 16 known vulnerabilities across enterprise platforms.
Beyond N-day exploitation, analysts confirmed Storm-1175 also developed the ability to use zero-day flaws — ones not yet publicly known.
In one case, the group exploited CVE-2026-23760, a SmarterMail flaw, a full week before public disclosure. Similarly, CVE-2025-10035 in Fortra’s GoAnywhere Managed File Transfer was exploited one week before official announcement.
Medusa ransomware operates as a Ransomware-as-a-Service platform — its developers rent tools and infrastructure to affiliates like Storm-1175.
Medusa uses a double extortion model: attackers encrypt victim data while stealing it, then threaten to release the files publicly if a ransom goes unpaid.
This puts organizations under enormous pressure, combining operational disruption with the long-term risk of data exposure. Industries that rely on internet-facing platforms face the highest risk from Storm-1175’s campaigns.
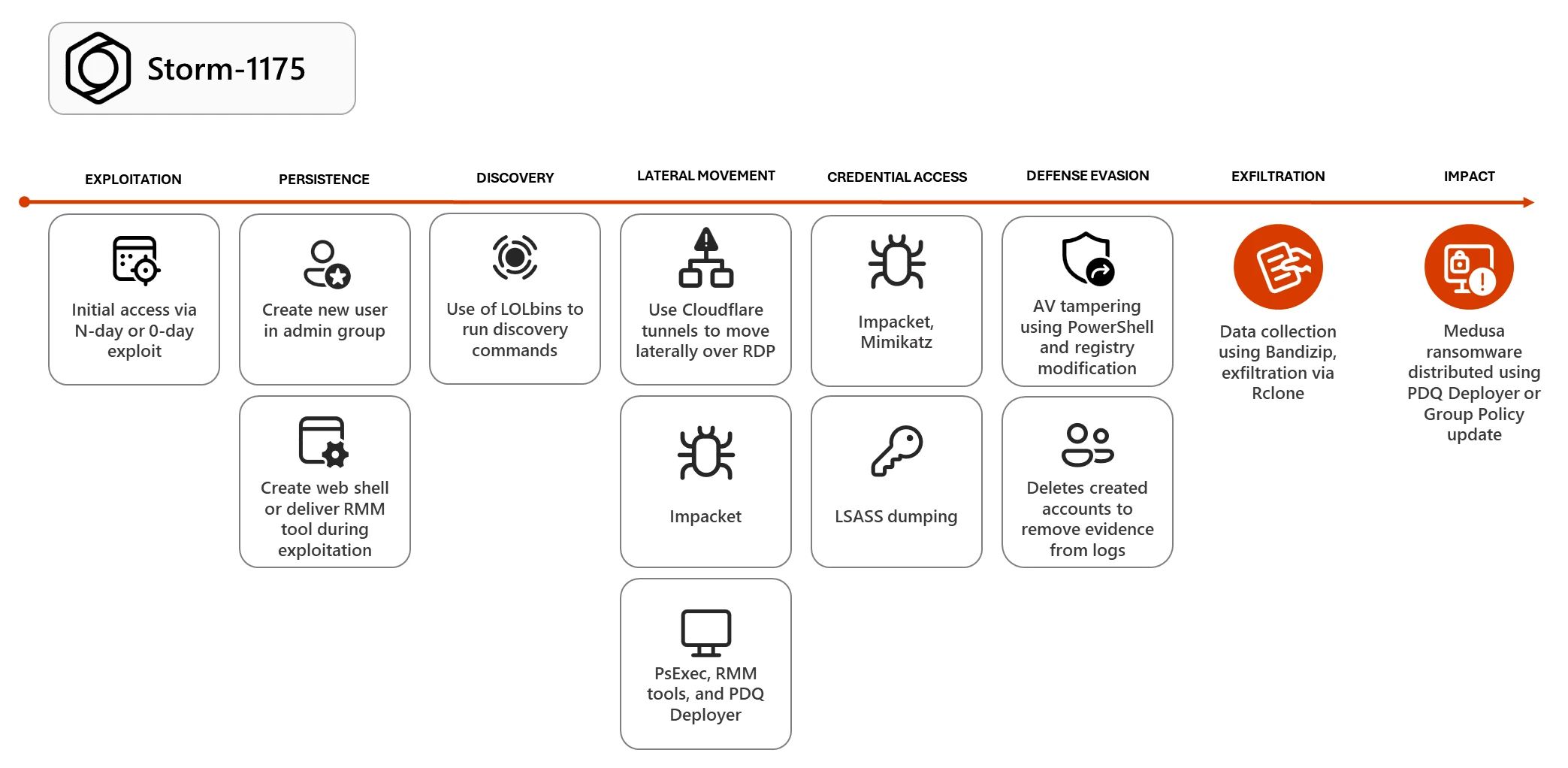
Inside Storm-1175’s Post-Compromise Playbook
Once Storm-1175 gets inside a target environment, the attack follows a rehearsed sequence of steps. The group first plants a web shell or drops a remote access payload — a small piece of code that allows reconnection to the compromised system at any time, even after the original flaw is patched.
New user accounts are also created early on to maintain a backup access path into the network.
From there, Storm-1175 deploys legitimate remote monitoring and management tools, blending activity into the normal traffic IT teams generate.
These tools allow attackers to move across internal systems without triggering security alerts. To disable defenses, the group tampers with Microsoft Defender Antivirus settings stored in the Windows registry — a step that requires highly privileged account access.
Attackers also use encoded PowerShell commands to add entire drives to antivirus exclusion lists, stopping security software from scanning for malicious files. Meanwhile, credential theft targets high-privilege accounts needed to push ransomware across the entire network.
When ready to finish the operation, Storm-1175 uses Bandizip to package collected files and Rclone to transfer that data to remote, attacker-controlled cloud storage.
PDQ Deployer is then used to execute a script called RunFileCopy.cmd, pushing Medusa ransomware payloads to every reachable machine.
In some cases, the group uses elevated privileges to trigger a Group Policy update, deploying ransomware simultaneously across every system in the domain.
Microsoft and security researchers advise organizations to patch internet-facing systems without delay — particularly within 72 hours for any vulnerability listed in the CISA Known Exploited Vulnerabilities catalog.
Security teams should monitor alerts tied to credential theft, unauthorized registry changes, and new user account creation, as these are reliable early warning signs of an active attacker.
Restricting RMM tools to approved applications and enforcing multi-factor authentication on all privileged accounts are also critical steps. Teams should regularly audit antivirus exclusion paths to detect unauthorized modifications before attackers can exploit the gap.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.