React2Shell Exploit Compromises 7 Hackers Compromised
Cisco Talos cybersecurity researchers have uncovered a massive automated credential theft campaign actively targeting web applications worldwide. This operation, attributed to the hacker group...
Cisco Talos cybersecurity researchers have uncovered a massive automated credential theft campaign actively targeting web applications worldwide. This operation, attributed to the hacker group UAT-10608, has already compromised over 700 servers.
The attackers are exploiting a critical security flaw known as React2Shell to gain access and steal highly sensitive data. The hackers are specifically targeting Next.js applications vulnerable to CVE-2025-55182, widely known as React2Shell.
This is a severe remote code execution flaw in React Server Components. It allows attackers to send a specially crafted web request to a vulnerable server.
Because the server does not properly check the incoming data, it executes the attacker’s hidden commands. Worst of all, this attack requires no passwords or user interaction.
700+ Next.js Hosts Exploited
The UAT-10608 group uses automated tools to scan the internet for vulnerable Next.js servers. Once they find a target, they launch the React2Shell exploit to gain initial access. The exploit then downloads a malicious script onto the server.
This script runs quietly in the background, acting like a digital vacuum cleaner. It searches the server’s files, cloud settings, and system memory to harvest valuable credentials.
The script works in multiple phases, extracting everything from cloud tokens to database passwords, and then sends the stolen data back to the hackers’ command-and-control server.
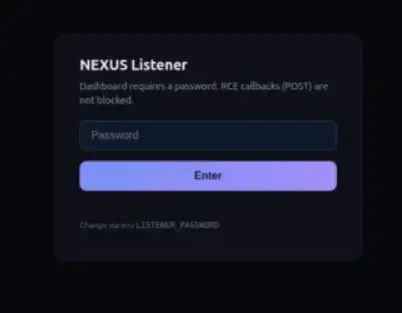
To manage the massive amount of stolen information, the attackers use a custom web dashboard called the “NEXUS Listener”. Cisco Talos researchers discovered that in just 24 hours, the dashboard recorded 766 compromised hosts.
The dashboard revealed the shocking scale of the theft:
- Over 90% of the hosts had their database credentials stolen.
- Nearly 80% lost their private SSH keys, which are used to access servers securely.
- Hackers also stole AWS cloud credentials, live Stripe payment keys, and GitHub access tokens.
The consequences of this attack are devastating. With the stolen database passwords, hackers can access private user information and financial records.

The exposed SSH keys allow them to move freely across different servers within a company’s network.
Furthermore, stolen cloud credentials give attackers the power to take over entire cloud environments, while compromised GitHub tokens could be used to insert malicious code into legitimate software updates.
Companies using Next.js must take immediate action to protect themselves. Organizations should urgently update their web applications to patch the React2Shell vulnerability.
Additionally, any company that might have been targeted should immediately change all its passwords, API keys, and security tokens.
Experts also recommend restricting access to cloud metadata services and carefully monitoring servers for any unusual background processes.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.