Exposed Server Exposes TheGentlemen Ransomware Reveals Toolkit
A misconfigured server, operating from a Russian bulletproof hosting provider, has exposed the full operational toolkit of a TheGentlemen ransomware affiliate. This exposure includes harvested victim...
A misconfigured server, operating from a Russian bulletproof hosting provider, has exposed the full operational toolkit of a TheGentlemen ransomware affiliate. This exposure includes harvested victim credentials and plaintext authentication tokens used to establish hidden remote access tunnels.
TheGentlemen ransomware group operates as a Ransomware-as-a-Service, or RaaS, operation where affiliates carry out attacks using shared tools and infrastructure.
The group has been documented targeting organizations across the Americas, Europe, and the Middle East, with capabilities spanning Windows, Linux, and ESXi environments.
Their attack playbook moves quickly, compressing the time between initial access and full encryption into hours. What makes this particular exposure significant is that the server did not just hold tools waiting to be used. It held evidence that those tools had already been deployed against real victims.
The server in question was found at IP address 176.120.22[.]127, operating over port 80 on Proton66 OOO infrastructure, an autonomous system with a history tied to SuperBlack ransomware, WeaXor, and XWorm campaigns.
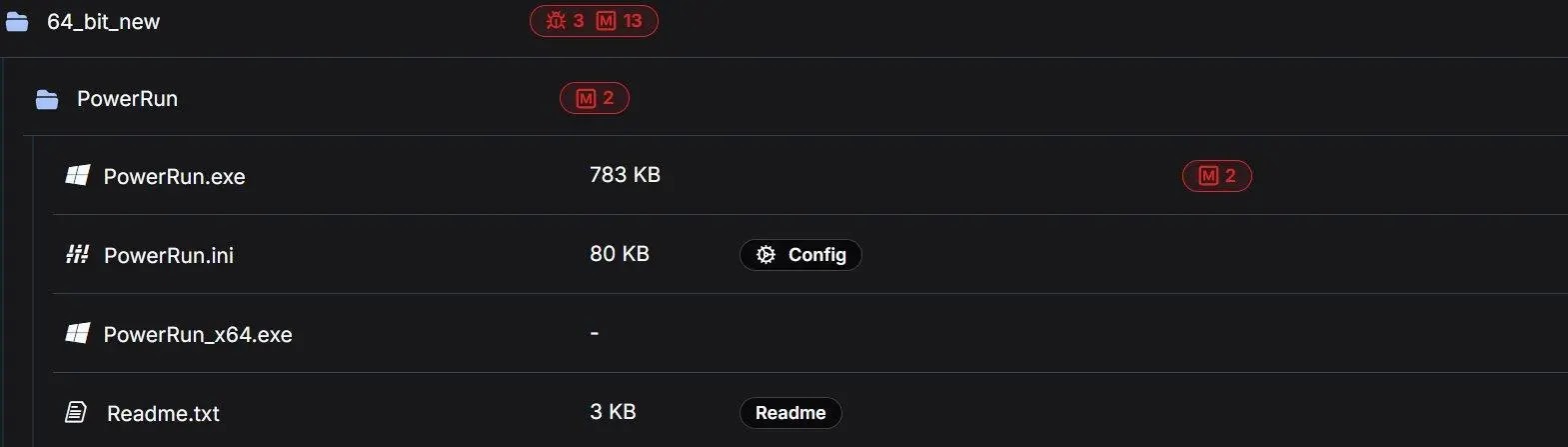
The directory contained 126 files across 18 subdirectories, totaling approximately 140 megabytes of operational material.
Hunt.io analysts identified the exposed open directory on March 12, 2026, while pivoting on indicators of compromise published in CyberXTron’s earlier report on TheGentlemen ransomware group.
Using the AttackCapture IOC search capability, the query returned a single result pointing directly to the unauthenticated server, which had been active for at least 24 days before the analysis.
Every analyzed script on the server was automatically classified as malicious, falling into two categories: Exploit, covering scripts that alter security settings and escalate privileges, and Config, covering scripts containing sensitive authentication tokens.
The AI-driven text file analysis flagged credential dumping routines, Defender disabling sequences, event log clearing, ngrok tunnel setup, and persistence mechanisms across multiple files.
Inside the Pre-Ransomware Deployment Script: z1.bat
The single most operationally revealing file in the entire directory is z1.bat, a 35-kilobyte batch script carrying the highest malware indicator count of any file on the server.
It consolidates nearly every pre-encryption preparation step into one execution, designed to run immediately before ransomware deployment when speed matters more than staying quiet.
The script opens by systematically deleting and disabling services tied to over a dozen security vendors, including Sophos, Kaspersky, Trend Micro, McAfee, ESET, Webroot, AVG, Malwarebytes, Panda, and Quick Heal.
It then extends that same stop-and-disable logic to enterprise applications including 30 or more Microsoft Exchange services, Oracle databases, MySQL, multiple Tomcat versions, Veeam backup infrastructure, and Hyper-V, all of which lock files that ransomware needs to reach.
Stopping these services ensures maximum encryption coverage across Exchange databases, SQL Server files, and backup vaults.
Beyond service termination, z1.bat performs a registry-wide purge targeting security product entries from nearly 20 vendors, spanning Kaspersky versions across nearly a decade of releases, the full McAfee product suite, and additional products including Bitdefender, COMODO, ESET, Avira, Norton, and Qihoo 360.
It also creates open SMB shares on every drive letter from C through K, granting full access to all users, allowing ransomware running on any compromised host to reach every shared drive across the network.
The script installs Image File Execution Options debugger redirects on Windows accessibility tools including sethc.exe, utilman.exe, Magnify.exe, and HelpPane.exe, replacing them with cmd[.]exe.
This is the classic Sticky Keys backdoor, allowing a SYSTEM-level command prompt to be opened directly from the Windows login screen.
Combined with enabling RDP, disabling Network Level Authentication, and setting UAC to off, this creates persistent access that survives the removal of every other remote access tool.
The script concludes by deleting all Volume Shadow Copies, wiping all Windows event log channels, clearing the Recycle Bin, and terminating all processes with a PID above 1000, effectively clearing the execution environment for ransomware launch.
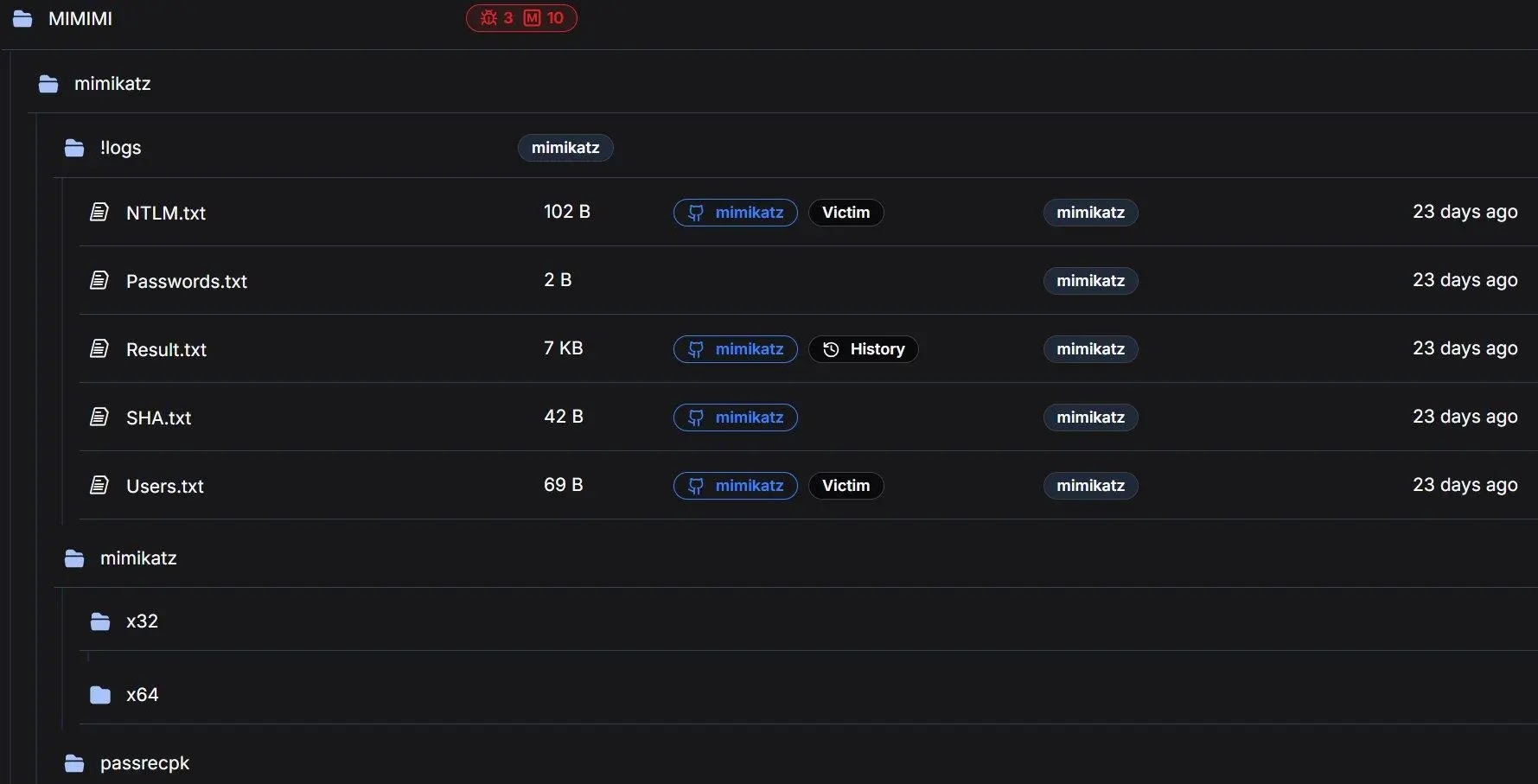
Security teams should monitor for several behaviors tied directly to this toolkit. On the endpoint side, watch for PowerRun execution, mass Windows Defender service state changes, batch-based event log clearing using wevtutil, LSASS memory access consistent with Mimikatz, IFEO debugger modifications on accessibility binaries, WDigest registry changes, and bulk network share creation.
On the network side, block connections to 176.120.22[.]127 and monitor for ngrok tunnel activity toward ngrok infrastructure.
Alert on vssadmin.exe Delete Shadows execution, mass service disabling patterns, and EnableLUA registry modifications.
For configuration hardening, enable Credential Guard, maintain offline immutable backups, enable endpoint tamper protection, audit Group Policy Objects for unauthorized Defender changes, and implement application whitelisting in user-writable directories.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.