Adblock Filters Expose User Location Even With VPN Protection
For many internet users, a Virtual Private Network (VPN) represents the pinnacle of online anonymity. While VPNs effectively obscure IP addresses and encrypt traffic, new research highlights a...
For many internet users, a Virtual Private Network (VPN) represents the pinnacle of online anonymity. While VPNs effectively obscure IP addresses and encrypt traffic, new research highlights a critical limitation: they don’t safeguard against every tracking method. A novel fingerprinting technique specifically exposes this vulnerability.
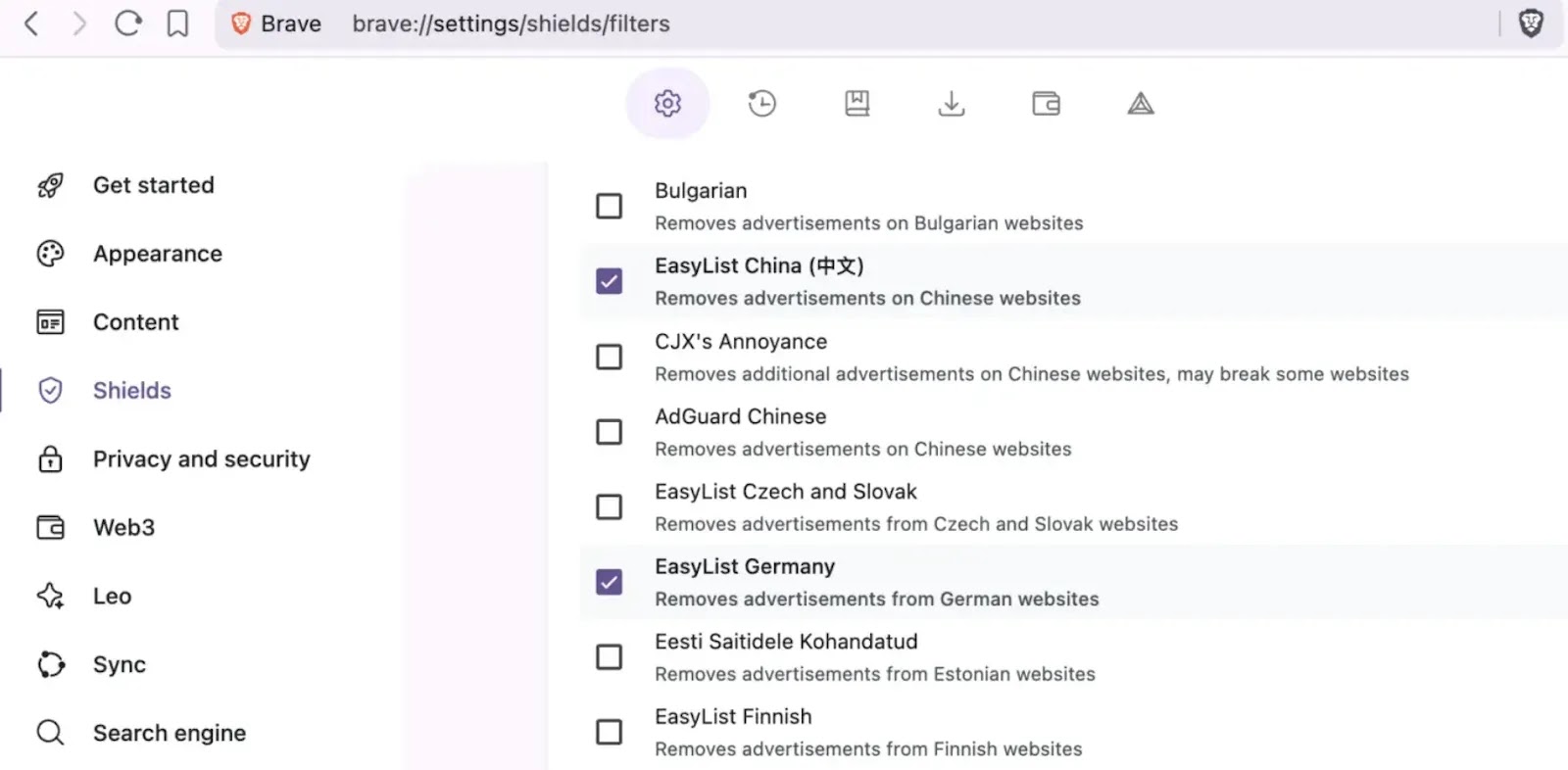
Country-specific AdBlock filter lists installed in browsers can expose your location, even when using a VPN. Most ad blockers, such as uBlock Origin, Brave, and AdBlock Plus, use filter lists to block ads.
The standard EasyList covers English-language ads, but users typically enable country-specific lists for better protection. Germans use EasyList Germany, French users enable Liste FR, and similar lists exist for Italy, Spain, Brazil, and other countries.
These lists block local ad networks not covered by the base list. These country-specific lists create a unique fingerprint.
A new proof-of-concept tool demonstrates how websites can detect which filter lists you have enabled, revealing your country or language preference regardless of your VPN location.
The technique uses simple JavaScript timing measurements. When a browser tries to load a tiny image from a domain blocked by an ad blocker, the request typically fails almost instantly, under 5 milliseconds.
Without an adblocker, the request reaches the network, and DNS lookups take 50-500 milliseconds or longer.
By testing 30 domains from each country-specific list and measuring response times, the tool determines which lists are active.
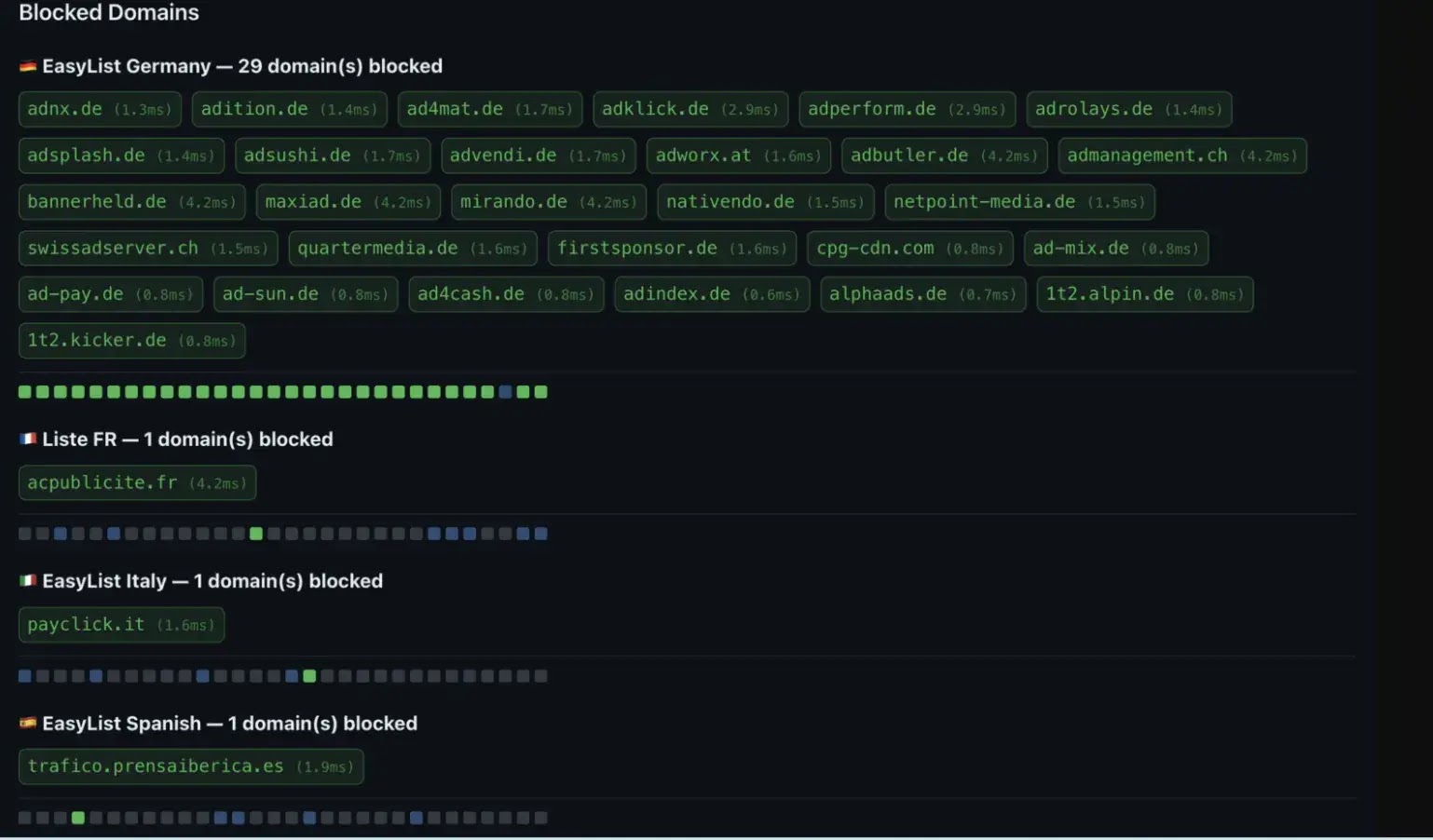
If 20 or more domains return blocked results (under 30ms), that country’s filter list is identified as enabled.
According to Adbleed, this fingerprinting vector works through VPNs, Tor Browser, and any proxy service. It requires no special permissions, cookies, or server cooperation, just client-side JavaScript.
Combined with other fingerprinting signals like timezone, keyboard layout, and screen resolution, this significantly narrows down user identity.
The detection is hard to prevent. Users can either turn off country-specific lists (allowing more local ads through), enable random country lists as camouflage, or stop using ad blockers entirely, each option having privacy trade-offs.
Adblock filter lists present a privacy paradox. They improve browsing by blocking ads and trackers, but country-specific configurations leak identifying information that VPNs cannot hide.
The fingerprinting technique is trivial to implement, difficult to detect, and challenging to mitigate without sacrificing effective ad blocking.
Users concerned about anonymity should understand that AdBlocker configuration contributes to their digital fingerprint. While VPNs remain valuable privacy tools, they are not silver bullets against all tracking methods.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.