Interlock Ransomware Actors New Tool Exploiting Gaming Anti-Cheat
The Interlock ransomware group poses a distinct threat, primarily focused on the education sector within the United States and United Kingdom. Unlike many contemporary ransomware operations that...
The Interlock ransomware group poses a distinct threat, primarily focused on the education sector within the United States and United Kingdom.
Unlike many contemporary ransomware operations that function under a Ransomware-as-a-Service (RaaS) model, Interlock operates as a smaller, dedicated team.
These operators develop and manage their own proprietary malware to control most of their attack chain, demonstrating a high level of sophistication and adaptability.
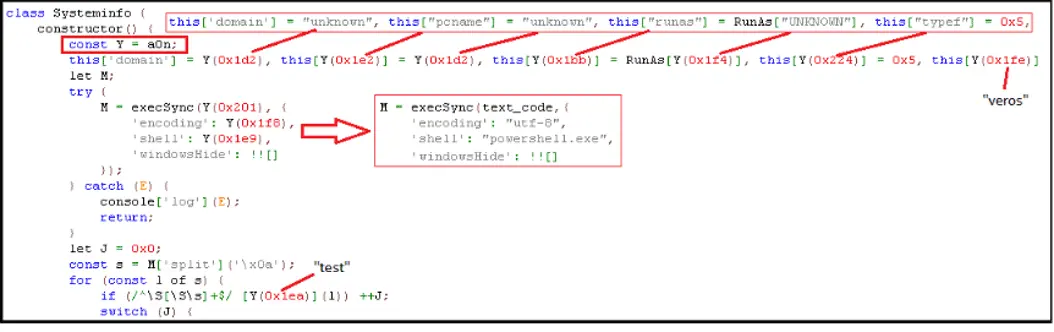
Their attacks often begin with a MintLoader infection, likely initiated through “ClickFix” social engineering tactics.
Once initial access is gained, often through a JavaScript implant known as NodeSnakeRAT, the attackers move laterally across the network.
They employ valid accounts and living-off-the-land binaries to establish persistence and conduct extensive system discovery. The impact of an Interlock intrusion is severe, involving both data theft and encryption.
The group has been observed using tools like AZcopy to exfiltrate significant amounts of data to cloud storage before deploying their ransomware.
This double-extortion tactic ensures they have leverage over their victims even if backups are available.
Fortinet analysts identified that the group deploys a unique set of tools to disable security defenses after establishing a foothold.
This allows them to execute their ransomware payloads on both Windows endpoints and Nutanix hypervisor environments without interference.
The group’s ability to pivot their techniques and exploit new vulnerabilities makes them a persistent danger to organizations globally, requiring heightened vigilance and robust defense strategies.
The “Hotta Killer” Evasion Tool
A key component of Interlock’s arsenal is a custom evasion tool dubbed “Hotta Killer,” designed to neutralize Endpoint Detection and Response (EDR) and antivirus (AV) software.
This tool employs a sophisticated “Bring Your Own Vulnerable Driver” (BYOVD) technique. It leverages a zero-day vulnerability in a legitimate gaming anti-cheat driver, originally named GameDriverx64.sys (CVE-2025-61155).
By dropping a renamed version of this vulnerable driver, UpdateCheckerX64.sys, the malware can execute privileged commands in the kernel space.
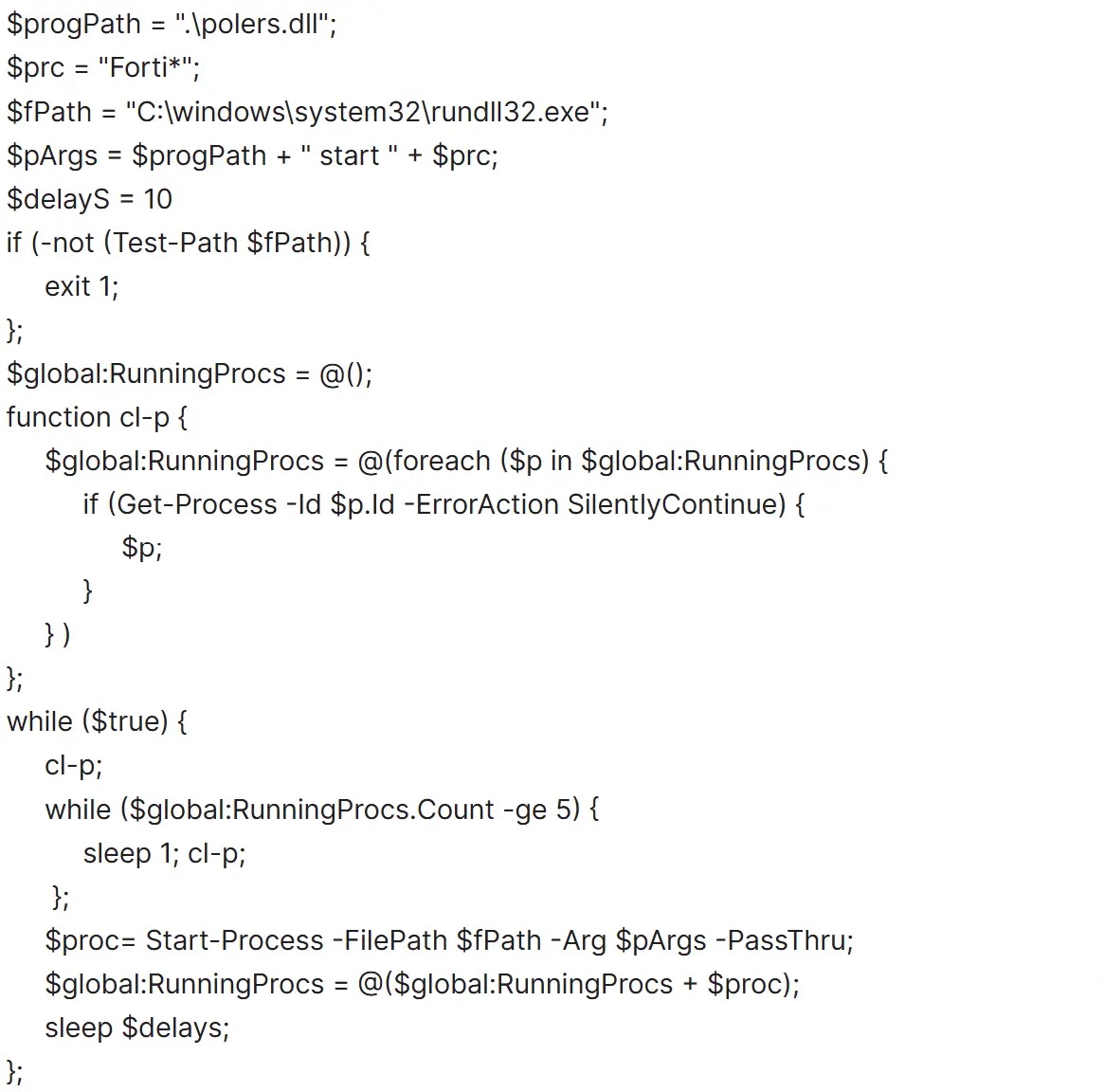
The “Hotta Killer” tool, implemented as a DLL file named polers.dll, is injected into system processes to mask its activity.
Once active, it creates a symbolic link to communicate with the malicious driver. It specifically targets processes associated with security software, such as those matching the pattern “Forti*.exe”.
By passing the Process IDs of these security tools to the driver, the malware forces the kernel to terminate them, effectively blinding the organization’s defenses before encryption begins.
To mitigate these threats, organizations should strictly block the execution of unauthorized remote access software and restrict workstation-to-workstation SMB and RDP connections.
Additionally, blocking outbound PowerShell network connections can prevent the initial download of malicious payloads.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.