Chollima APT Uses LNK File to Deploy Sophisticated
Since March 2025, the Ricochet Chollima advanced persistent threat group has launched a targeted campaign against activists and organizations focused on North Korea. The operation, named “Operation:...
Since March 2025, the Ricochet Chollima advanced persistent threat group has launched a targeted campaign against activists and organizations focused on North Korea.
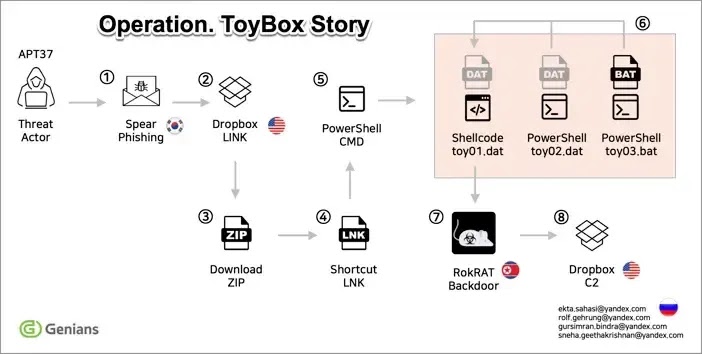
The operation, named “Operation: ToyBox Story” by Genians Security Center, relies on a clever combination of social engineering and malware delivery tactics.
Attackers send spear-phishing emails that appear to come from credible sources, specifically impersonating North Korea-focused security experts.
These emails contain Dropbox links that lead to compressed archives holding malicious Windows shortcut files. The victims unknowingly download files that trigger hidden code execution when opened.
The attack demonstrates significant sophistication in disguising malicious content. Threat actors crafted emails with subject lines referencing North Korean troops deployed to Russia, using culturally relevant content to increase the likelihood of user engagement.
The email attachments mimic Hangul document icons—commonly associated with legitimate Korean word processors—to deceive recipients into thinking they are opening standard documents rather than executable files.
This social engineering approach proves effective because users trust familiar file icons and organizations they believe are sending the messages.
An Offensive Security Engineer, S3N4T0R, noted the malware after analyzing the campaign’s technical characteristics and infection chain.
S3N4T0R identified how the attack progresses through multiple stages, each designed to evade security tools and maintain persistence on compromised systems.
The analysis revealed that attackers deliberately structured the malware to stay hidden in system memory rather than writing files to disk.
Fileless Execution Through Memory Injection
The most dangerous aspect of this malware involves its ability to execute code without leaving traces on the hard drive.
When victims extract the ZIP archive and open the seemingly innocent document file, a hidden PowerShell command embedded within the shortcut executes silently.
This command launches a batch file named “toy03.bat,” which then loads a file called “toy02.dat” from the temporary folder.
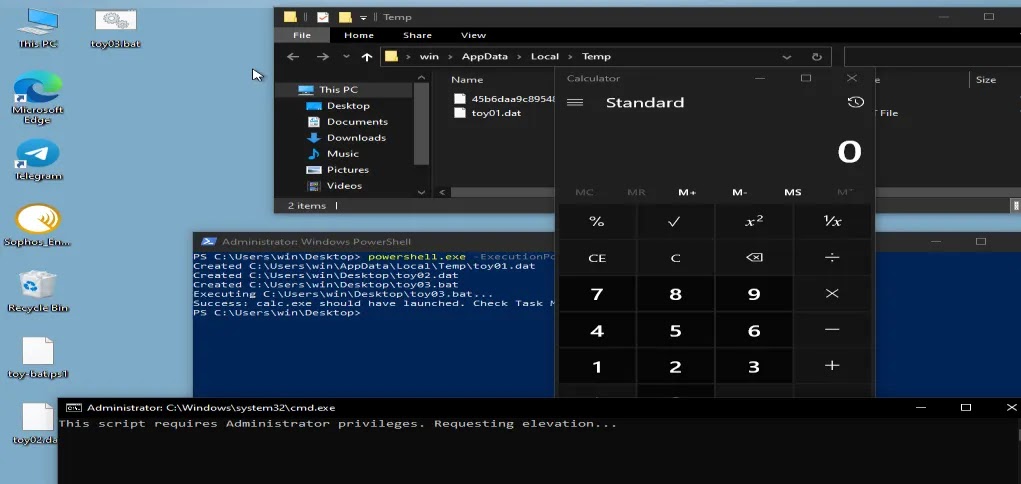
The loader decodes XOR-transformed data and injects shellcode directly into memory, bypassing traditional file-based detection methods.
Once loaded into memory, the malware creates a new executable thread to run the injected code.
This technique, known as fileless malware execution, presents serious challenges for security teams because the malicious program leaves minimal evidence on disk.
The malware then establishes communication through Dropbox API channels, allowing attackers to send commands and receive stolen data while hiding their activities within legitimate cloud service traffic.
This approach represents a significant evolution in APT tactics, leveraging trusted services to conceal malicious operations and making detection substantially more difficult for defenders.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.