Fake Captcha Exploits Web Infrastructure to Deliver
Recently, web-based malware campaigns have exploited fake verification pages, deceiving users into installing dangerous software. These attacks copy the look and feel of legitimate security checks...
Recently, web-based malware campaigns have exploited fake verification pages, deceiving users into installing dangerous software.
These attacks copy the look and feel of legitimate security checks that people see every day while browsing the internet.
The fake captcha ecosystem represents a fast-changing threat that uses trusted web interfaces as delivery surfaces for malicious payloads.
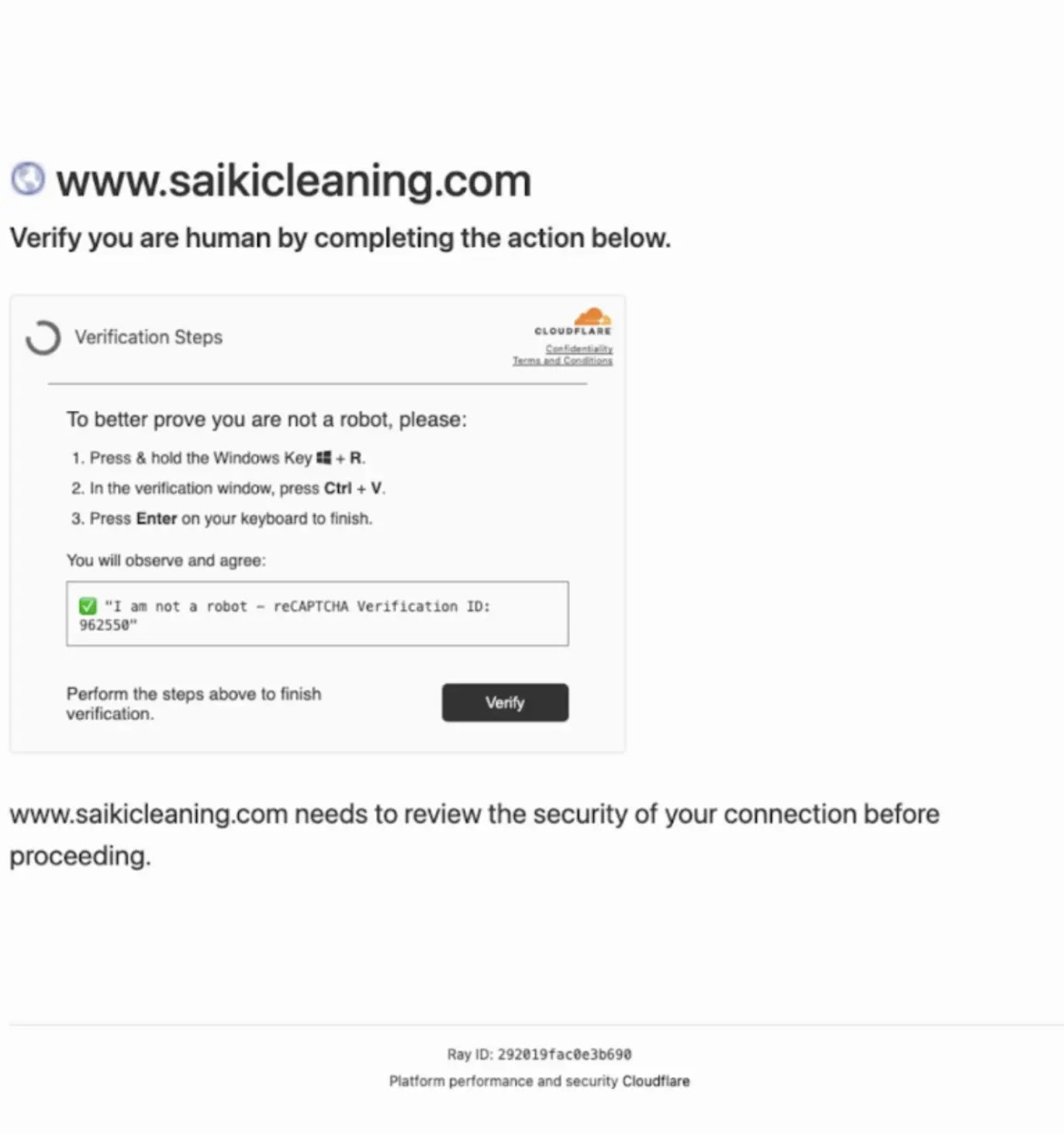
Over the past several years, fake captcha pages have become a common method for spreading malware. These pages look like normal browser verification challenges, similar to the security checks used by platforms like Cloudflare.
Users are instructed to complete steps that appear to be legitimate security measures but actually trigger harmful scripts or grant dangerous browser permissions. The attacks exploit the trust people have developed for routine security interactions online.
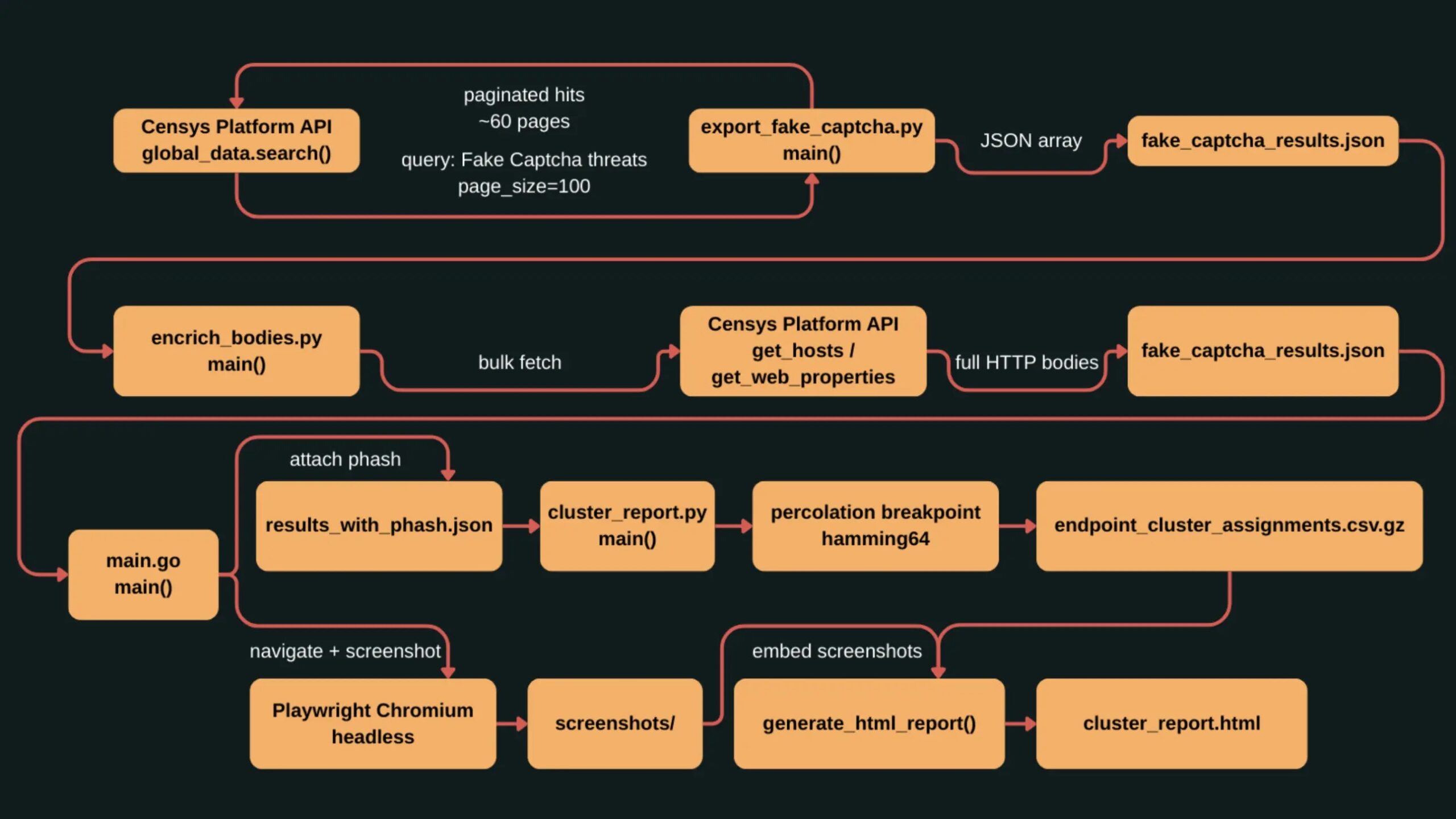
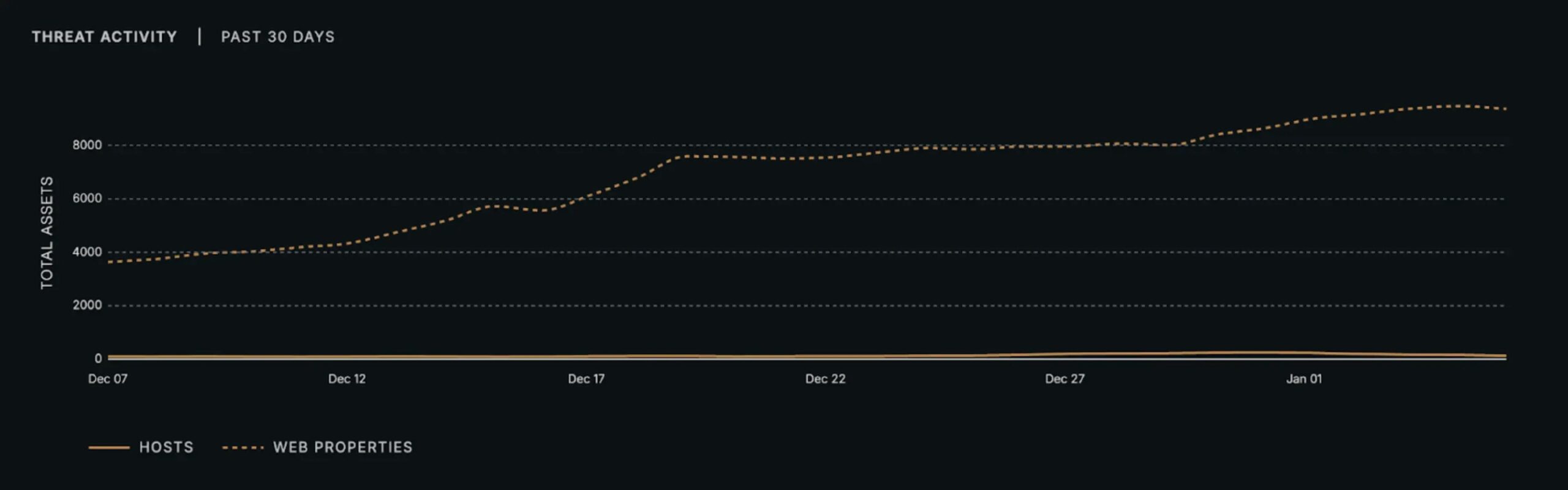
Censys analysts identified that this threat landscape involves approximately 9,494 distinct compromised websites and malicious properties actively hosting fake captcha pages.
The researchers tracked these assets through continuous monitoring of exposed web infrastructure and found that roughly 70% of all observed fake captcha activity shares a nearly identical visual appearance.
However, this visual similarity masks a fragmented ecosystem of different attack methods operating behind the same interface.
Diverse Infection Mechanisms Behind Uniform Appearance
Despite looking almost identical, fake captcha pages employ fundamentally different infection techniques.
Censys researchers noted that within the largest visual cluster of fake captcha sites, at least 32 distinct payload variants were discovered across multiple incompatible execution models.
Some attacks use clipboard manipulation to execute PowerShell or VBScript commands that download malware. Others rely on Windows Installer packages delivered through MSI files hosted on compromised domains.
A third category uses server-driven push notification frameworks that avoid exposing any visible payload during the initial interaction.
The clipboard-driven approach remains the most common technique. VBScript downloaders account for approximately 1,706 observed assets, while PowerShell-based methods appear on roughly 1,269 sites.
These attacks copy malicious commands to the user’s clipboard and instruct victims to paste and execute the code through seemingly legitimate verification steps.
However, installer-based delivery through MSIEXEC represents about 1,212 assets, shifting the attack into different security surfaces entirely.
The Matrix Push C2 framework introduces a completely fileless delivery model found on approximately 1,281 assets. This technique tricks users into granting browser notification permissions rather than executing immediate payloads.
Once permissions are granted, attackers can push malicious content later through the browser’s notification channel. Static analysis of these pages reveals no executable artifacts because delivery is deferred and controlled entirely by remote servers.
This makes traditional payload-centric detection strategies ineffective against this particular attack vector.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.