CISOs Accelerate Security Modernization for Third-Party
Panorays has published the latest edition of its annual CISO Survey for Third-Party Cyber Risk Management, a report that delivers significant implications for security professionals. The biggest...
Panorays has published the latest edition of its annual CISO Survey for Third-Party Cyber Risk Management, a report that delivers significant implications for security professionals.
The biggest takeaway is that software supply chain attacks are rising once more, as cybercriminals look to take advantage of their complexity by targeting a growing laundry list of third-party components.
The situation isn’t helped by the mass adoption of AI, which not only increases the threat surface, but also provides cybercriminals with more advanced tools for carrying out their attacks.
However, AI works both ways, and there are encouraging signs for enterprise security as more security leaders turn to such tools to bolster their cyber defense.
According to Panorays, 60% of the 200 U.S.-based CISOs surveyed said they’ve witnessed an increase in third-party security incidents this year. Of those, 9% said the jump had been “significant,” while 51% said the number of attacks had only slightly increased.
But the bigger concern for CISOs is the impact of those incidents.
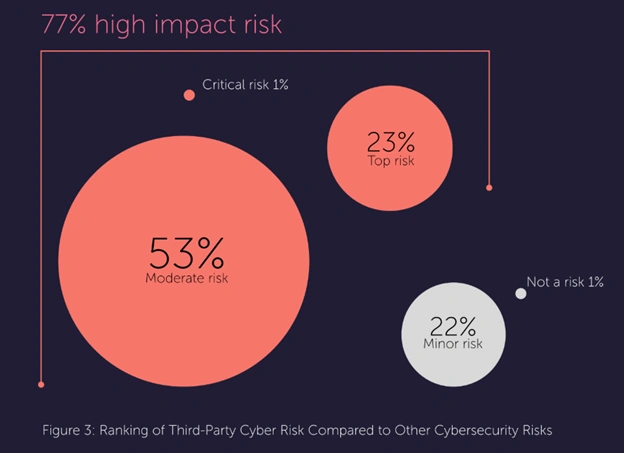
More than three-quarters of respondents said third-party software risks are one of the most substantial cybersecurity concerns they face, with 23% going as far as to say it’s the number one risk to their organization.
Just 22% said they rank third-party risk as a “minor” concern.
The findings demonstrate that CISOs are becoming acutely aware of their reliance on third-party software vendors, and that’s just as well given how deeply embedded such tools have become in their business operations.
An earlier study by JumpCloud showed that the average enterprise uses anywhere from 100 to 300 software-as-a-service applications, and that is really just the tip of the iceberg, for it doesn’t include elements like cloud infrastructure and the open-source components used in proprietary applications.
As Static Surveys Go Stale, CISOs Turn to AI Tools
Third-party software has created a growing attack surface that few CISOs really know how to handle, primarily due to an alarming lack of visibility.
According to Panorays, just 15% of respondents claimed to have full insight into their entire software supply chains.
The lack of visibility into third-party software supply chains stems from organization’s continued reliance on outdated threat assessment methods.
The report found that the vast majority of CISOs still use traditional vendor security questionnaires as their primary source of threat intelligence, yet 71% admit they are unable to accurately assess third-party risk.
Typically, organizations will provide vendors with a static list of questions during the onboarding phase, but while the insights gleaned might be useful, they cannot identify evolving threats.
It’s primarily a problem of scale – vendor ecosystems are growing exponentially, and so these manual processes can no longer keep up with the changing threat landscape.
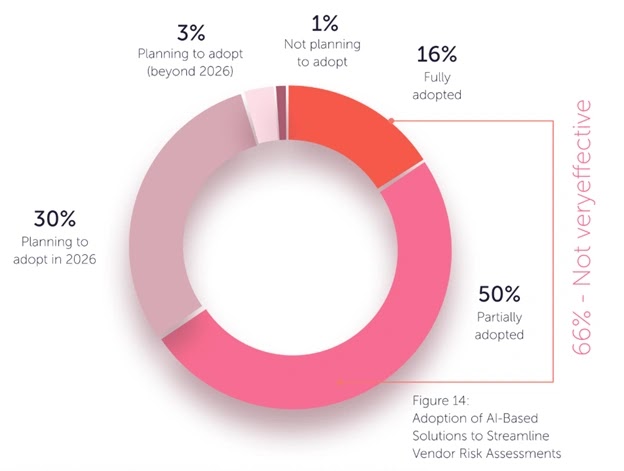
Fortunately, the growing awareness around the deficiencies of static questionnaires appears to have kick-started a modernization push, with two-thirds of CISOs responding by embracing newer, AI-powered tools to try and enhance vendor risk assessment.
Among those who haven’t yet adopted AI tools, the majority intend to do so soon, with just 1% of CISOs saying they have no such plans.
The growing adoption of AI for cyber threat visibility underscores the changing nature of the CISO’s role. Modern CISOs are no longer just technical gatekeepers – instead, they have to act like orchestrators of enterprise-wide risk management.
They’re required to build a culture of cyber resilience, and that explains why so many are embracing AI-enabled security platforms.
With AI, it’s possible to automate many of the more time-consuming aspects of threat assessment, auto-filling responses based on historical data and freeing security teams to focus on risk validation.
AI also improves accuracy because it eliminates human fatigue, reducing the number of false positives and creating space for deeper oversight.
Visibility Isn’t Enough
AI clearly has transformative potential for threat visibility, but much work remains. Enhanced visibility doesn’t do much good if CISOs don’t also have a comprehensive, tried-and-tested incident response plan in place to deal with the threats they surface.
Unfortunately, just 21% of CISOs currently do have a plan to deal with breaches that stem from external software suppliers, while the rest lack any kind of standardized framework on how to deal with them.
The good news is that fixing this appears to be on CISOs’ agendas, particularly at larger organizations. The survey found that 36% of CISOs at enterprises with 10,000 or more employees do have a proper incident response plan, compared to just 16% of CISOs at smaller companies with less than 5,000 employees.
Panorays founder and CEO Matan Or-El blamed the rise in third-party security vulnerabilities on the “rampant adoption” of AI tools, but said he’s also optimistic that AI will be the solution to many of these woes.
“CISOs are increasingly seeing the value of AI-driven solutions to increase clarity around the evolving threat landscape,” he explained.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.