$44 Evilmouse Autonomously Compromises Connected Systems
A new $44 hardware implant has emerged, designed to look like an ordinary computer mouse. This device operates as a covert keystroke injector, much like a Hak5 Rubber Ducky. Crucially, its innocuous...
A new $44 hardware implant has emerged, designed to look like an ordinary computer mouse. This device operates as a covert keystroke injector, much like a Hak5 Rubber Ducky. Crucially, its innocuous form factor allows it to bypass basic user awareness training.
Plug it in, and it autonomously runs payloads that execute commands, deliver reverse shells, or worse, without arousing suspicion.
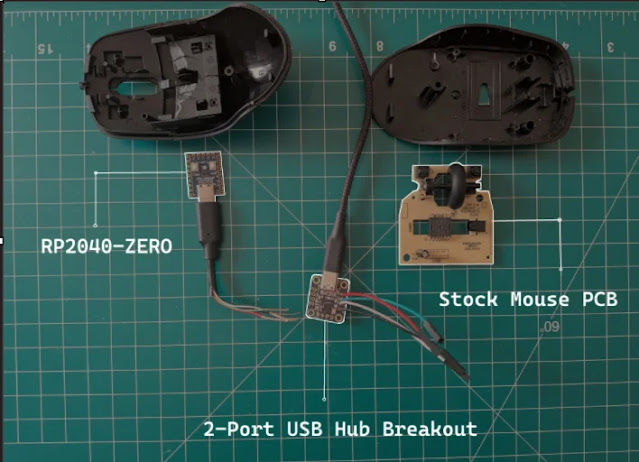
Traditional USB drives trigger alarms post-training, but a functional mouse? It blends seamlessly into any workspace. Evilmouse preserves the host mouse’s optical sensor and buttons via an integrated USB hub, ensuring cursor movement and clicks work normally.
“Everyone knows USB sticks are risky,” NEWO-J notes in the project write-up. “A mouse might not even register as a threat.”
The build repurposes cheap components for under $50:
| Material | Quantity | Approx. Price |
|---|---|---|
| RP2040 Zero microcontroller | 1 | $3 |
| Adafruit 2-Port USB Hub Breakout | 1 | $5 |
| Amazon Basics Mouse | 1 | $6 |
| USB-C Pigtail Cable | 1 | $3 |
| Rosin-core 60/40 Solder | 1 | $8 |
| USB-C Data Cable | 1 | $8 |
| Flux Paste | 1 | $6 |
| Kapton Tape | 1 | $5 |
| Dupont Wires | 4 | ~$0.03 |
| Total | ~$44 |
This undercuts a Rubber Ducky’s $100 price tag, democratizing hardware implants for red teams or malicious actors.
Housed in a $6 Amazon Basics mouse, the compact shell demanded modifications. Researchers must excise plastic ribbing with a multi-tool cutter and delicately desolder the stock PCB’s white connector using a flathead screwdriver.
The RP2040 Zero, flashed with CircuitPython firmware, handles exploitation. Incompatibility with pico-ducky prompted custom code: a Windows AV-safe reverse shell to a listener host.
Soldering the USB hub, pigtail, and wires proved tricky—NEWO-J practiced for a week on through-hole components. Kapton tape insulates against shorts, and precise wire routing allows the shell to snap shut while maintaining functionality.
Full code resides on GitHub, with plans for DuckyScript compatibility. “Built for education only,” the repo warns, disclaiming malicious use.
In a video demo, plugging Evilmouse into “Laptop A” yields an admin-level reverse shell on “Laptop B” within seconds. No user interaction required. Enhancements like hidden command prompts or scheduled tasks add persistence. Stealth tactics evade Windows Defender, though advanced bypasses remain future work.
Evilmouse underscores HID (Human Interface Device) attack vectors. Mice emulate trusted peripherals, exploiting USB’s plug-and-play trust.
Defenses include USB device whitelisting via Group Policy, endpoint detection tools scanning for anomalous keystrokes, and physical port restrictions. For pentesters, it offers a cheap alternative to commercial gear improve it with Rust for faster injection or remote triggers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.