ZeroDayRAT Attacks Android/iOS: Real- Attacking Real-Time
ZeroDayRAT, a new mobile spyware platform, was first observed in activity on February 2, 2026. Sold openly through Telegram, it targets Android (5–16) and iOS (up to 26), offering attackers a single...
ZeroDayRAT, a new mobile spyware platform, was first observed in activity on February 2, 2026. Sold openly through Telegram, it targets Android (5–16) and iOS (up to 26), offering attackers a single cross-platform tool.
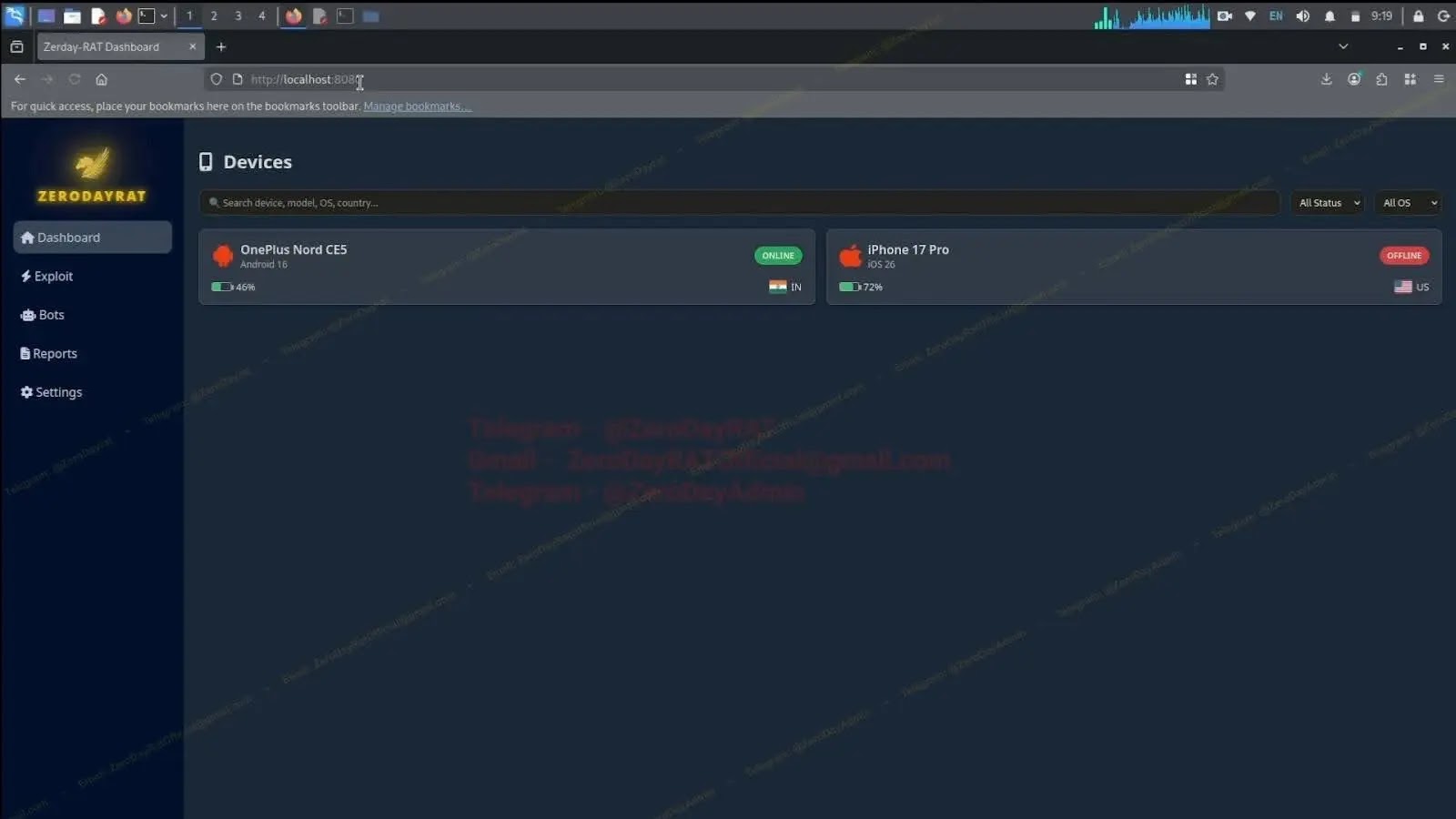
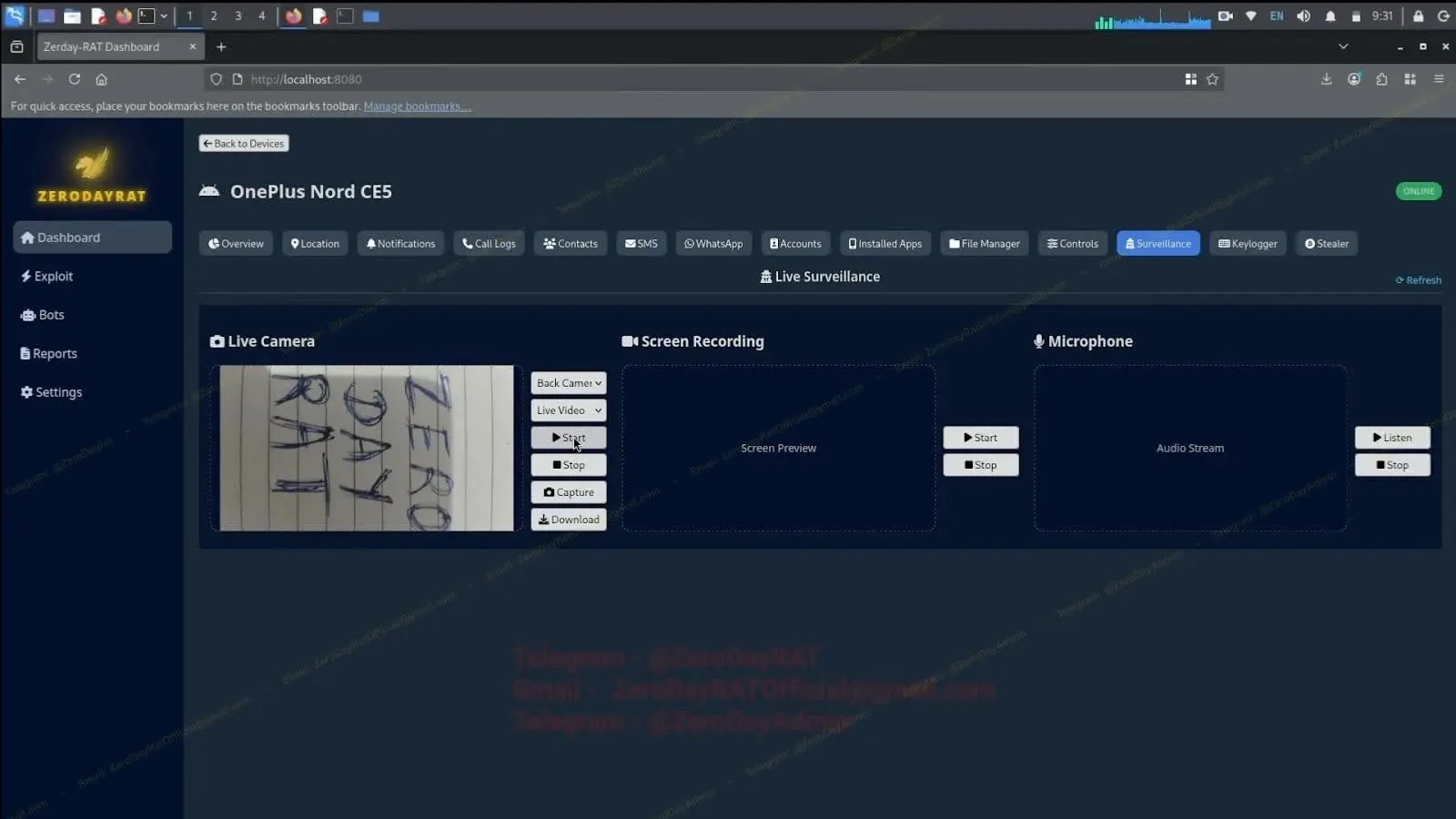
From a browser-based control panel, an operator can monitor and control an infected phone.
The panel supports GPS tracking, notification capture, SMS access (including OTP codes), live camera and microphone feeds, screen recording, and keylogging tied to app context.
It can list accounts registered on the device and includes theft features such as crypto clipboard address swapping and banking overlays for credential capture.
iVerify researchers identified ZeroDayRAT while reviewing the fast-growing market for “ready to run” mobile spyware. After installation, the tool is built so an operator can act without deep technical knowledge.
Delivery often relies on smishing, where a text message pushes a link that leads to a fake app download.
Similar lures can arrive via phishing emails, fake app stores, or links shared in WhatsApp or Telegram chats, ending in an Android APK or an iOS payload.
Once installed, an operator can profile the user by viewing device details, SIM and carrier data, app usage, and intercepted messages.
With SMS visibility, SMS-based two-factor codes can be exposed and abused, increasing the risk of account takeover and direct financial loss.
Infection mechanism
A typical infection chain starts with a message that creates urgency and sends the target to a download page that looks legitimate.
If the user installs the app, the implant reports into the operator’s dashboard, where the attacker can pull location history, read notifications, and harvest SMS that may include banking alerts and OTP codes.
The overview can show device model, OS version, lock status, country, and a live activity timeline, which speeds up targeting decisions.
Defenders should treat phones like endpoints: stick to official app stores, limit sideloading, and verify links received by text before tapping.
Use stronger MFA than SMS where possible, rotate passwords after suspected exposure, and investigate sudden permission prompts, battery drain, or unknown accessibility services.
For organizations, add mobile threat monitoring and a clear process to triage suspected spyware. Rapid reporting can limit damage.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.