Windows 11 and Server 2025 Update to Block Untrusted Cross-Signed
Microsoft is implementing a significant security change for the Windows operating system. To counter kernel-level threats, the company will no longer trust drivers signed through its deprecated...
Microsoft is implementing a significant security change for the Windows operating system. To counter kernel-level threats, the company will no longer trust drivers signed through its deprecated cross-signed root program.
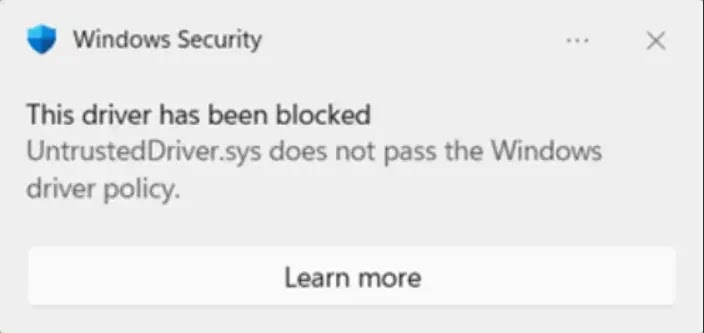
Starting with the April 2026 update, Windows 11 and Windows Server 2025 will block these untrusted drivers by default.
This policy ensures that only drivers certified through the Windows Hardware Compatibility Program can load automatically, significantly reducing the attack surface for malicious actors.
Closing a legacy Security Gap
The cross-signed root program was introduced in the early 2000s to allow third-party certificate authorities to issue Windows-trusted code-signing certificates.
However, this system provided no assurances regarding the security or compatibility of the kernel code. Because developers managed their own private keys, the program became a frequent target for credential theft, allowing threat actors to deploy rootkits.
Microsoft officially deprecated this signing program in 2021, and all related certificates have since expired. Despite this, Windows continued to trust these legacy certificates to maintain compatibility with legacy hardware.
This new update finally severs that lingering trust. Moving forward, the certification pipeline requires vendors to pass strict identity vetting, submit rigorous test results, and undergo malware scanning before receiving a protected Microsoft-owned certificate.
To prevent system crashes, Microsoft is introducing an explicit allow list for highly reputable, widely used cross-signed drivers.
The kernel update will also deploy in a careful evaluation mode. The Windows kernel will audit driver load signals to ensure the new policy will not disrupt critical functions.
The system will only enforce the block after meeting specific runtime and restart thresholds. If an unsupported driver is detected during this audit phase, the system resets the evaluation timer and holds off on enforcement.
Enterprise environments relying on internally developed custom kernel drivers have alternative options. Organizations can securely bypass the default block using an Application Control for Business policy.
By signing this policy with an authority rooted in the device’s UEFI Secure Boot variables, administrators can explicitly trust private signers.
This ensures threat actors cannot arbitrarily load malicious drivers while legitimate internal operations continue uninterrupted.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.