WhatsApp Usernames: Connect Without Sharing Phone Numbers
WhatsApp is preparing to launch a long-anticipated username feature. This upcoming functionality will allow users to communicate without ever revealing their phone numbers, marking a significant...
WhatsApp is preparing to launch a long-anticipated username feature. This upcoming functionality will allow users to communicate without ever revealing their phone numbers, marking a significant privacy upgrade for one of the world’s most widely used messaging platforms.
First spotted by WABetaInfo in the WhatsApp beta for iOS 26.1.10.70, the username system is compatible across Android, iOS, Windows, and Web.
The feature is currently limited to a small group of beta testers, with a phased expansion planned over the coming months as WhatsApp continues monitoring stability and performance ahead of a broader release.
Once the feature becomes available, users can navigate to their profile settings to check eligibility. Those with access will find a dedicated username option that guides them through a simple, step-by-step setup. Chosen usernames are then linked directly to the account and can be shared in place of a phone number.
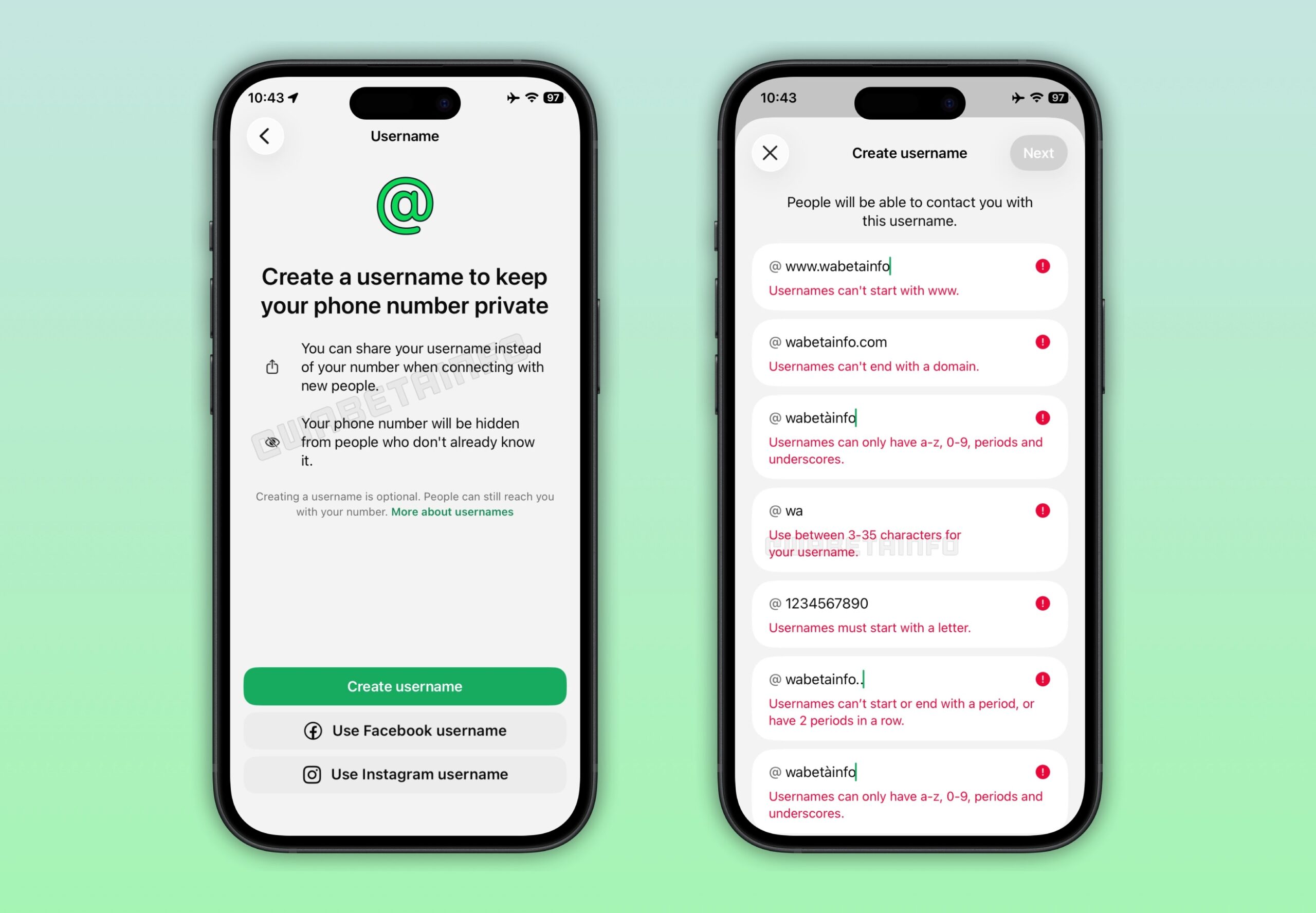
WhatsApp has established strict character requirements: usernames must be between 3 and 35 characters, include at least one letter, and may only contain lowercase letters (a–z), numbers (0–9), periods, and underscores.
WABetaInfo noted that usernames cannot begin with “www.” or end with a domain extension such as .com or .net, rules designed to prevent impersonation and phishing attempts that could mislead users into trusting fraudulent contacts.
One of the more notable security considerations involves username availability across Meta’s ecosystem. A username can only be claimed on WhatsApp if it is also available or verifiably owned by the same user on Instagram and Facebook.
Ownership verification is handled through Meta’s Accounts Center, a centralized hub for managing connected accounts.
However, security-conscious users should note a critical privacy implication: selecting the same username across Meta platforms effectively links your WhatsApp identity to your Instagram or Facebook profiles.
This cross-platform linkage could enable unknown contacts to identify and locate a user across multiple services, expanding the potential attack surface for social engineering or targeted harassment.
To address contact control, WhatsApp is introducing an optional “username key,” a 4-digit code that serves as a secondary authentication layer. When enabled, anyone attempting to contact a user for the first time must supply both the username and the correct key.
This mechanism limits unsolicited contact to trusted individuals, offering meaningful protection against spam and unwanted outreach.
All messages exchanged through username-based contacts remain end-to-end encrypted, consistent with WhatsApp’s existing security architecture.
While the username feature marks a genuine step forward for privacy decoupling phone numbers from communication, users should carefully evaluate cross-platform username consistency and enable the username key to minimize exposure to unknown actors.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.