WaterPlum Deploys StoatWaffle Malware in VSCode-Based Supply
North Korea-linked WaterPlum has deployed StoatWaffle, a dangerous new malware, infiltrating developer machines through compromised Visual Studio Code (VSCode) repositories disguised as legitimate...
North Korea-linked WaterPlum has deployed StoatWaffle, a dangerous new malware, infiltrating developer machines through compromised Visual Studio Code (VSCode) repositories disguised as legitimate blockchain development projects.
WaterPlum has been running a campaign known as “Contagious Interview” for some time, drawing victims in through fake job interview setups and tricking them into running harmful code on their systems.
The group is divided into several teams, and Team 8 — also tracked under the names Moralis and Modilus — is responsible for this latest wave. Team 8 previously depended on a malware family called OtterCookie as its main tool.
Starting around December 2025, the team shifted gears and began deploying StoatWaffle instead, signaling a clear and deliberate upgrade in its attack toolkit.
NTT Security analysts identified StoatWaffle while investigating Team 8’s latest activities, noting that the malware marks a meaningful shift in WaterPlum’s operational approach.
Their report, published on March 17, 2026, describes StoatWaffle as a fully modular, Node.js-based framework that operates in stages — consisting of a loader, a credential-stealing module, and a remote access trojan (RAT) component — each working together to give attackers deep access to compromised systems.
The attack starts with a carefully crafted repository shared among developers. Team 8 builds what appears to be a genuine blockchain project and places it where developers are likely to discover it.
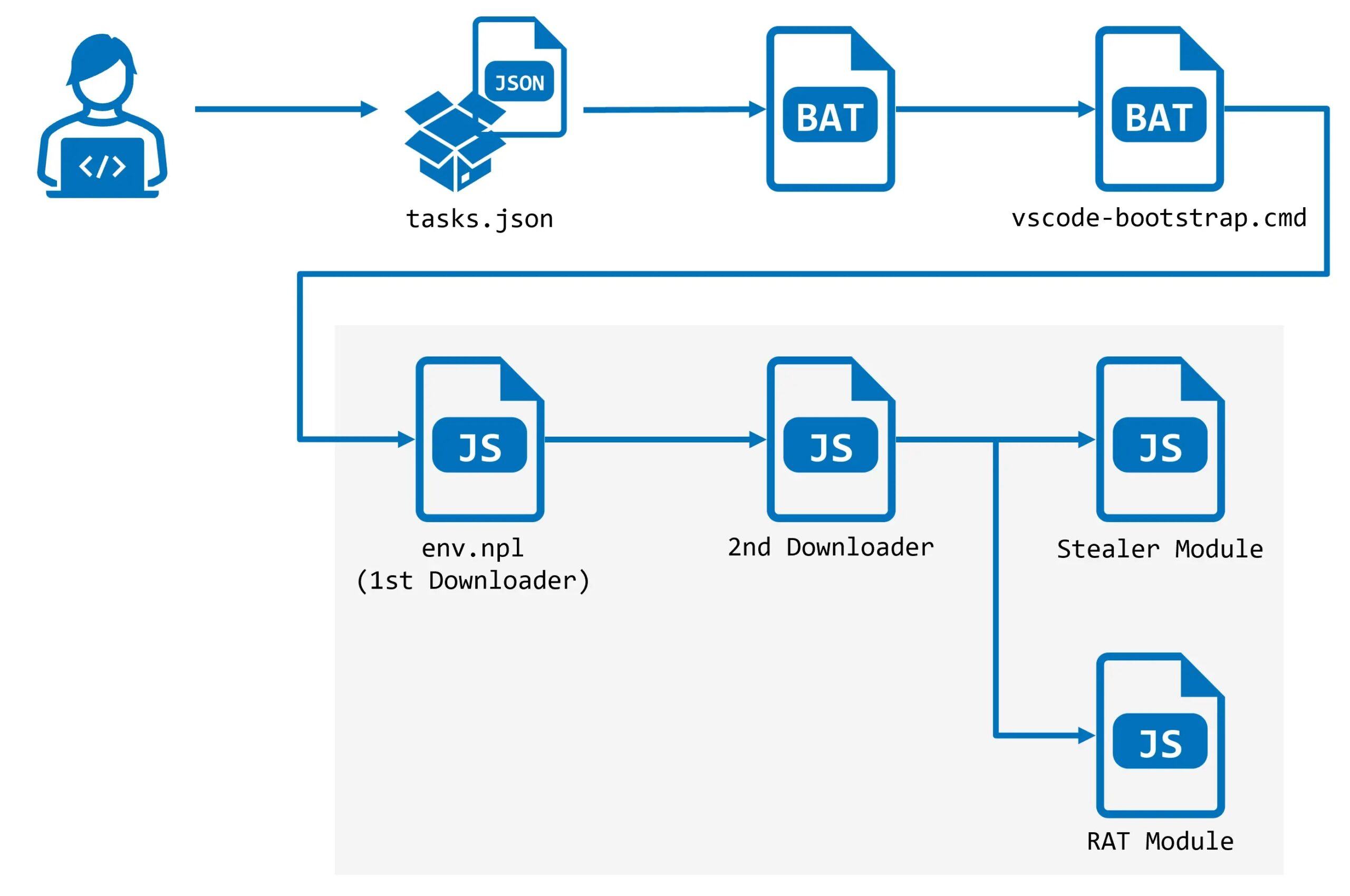
Hidden inside the project is a .vscode folder containing a tasks.json file configured with a runOn: folderOpen setting.
As soon as a developer opens the folder in VSCode and grants it trust, the editor automatically executes a pre-set task — requiring no further action from the victim.
What makes this threat particularly serious is that most developers would not expect that simply opening a VSCode project folder could silently trigger a full malware infection running in the background — no scripts to run manually, no prompts to accept.
StoatWaffle’s Infection Chain
When the malicious task executes, it reaches out to a Vercel-hosted web application and downloads a batch script called vscode-bootstrap.cmd. This script first checks whether Node.js is installed on the machine.
If it is not, the script quietly downloads and installs it from the official Node.js website — removing a key technical barrier without drawing any attention. It then fetches a JavaScript file called env.npl, which acts as the first-stage downloader in StoatWaffle’s infection chain.
The env.npl file connects to a C2 server at 147[.]124.202.208 on port 3000 and polls the /api/errorMessage endpoint every five seconds.
When the server responds with an error status, the loader runs the JavaScript code embedded in that response, pulling down the second-stage payload.
Roughly five minutes into this polling cycle, the second downloader arrives and begins its own loop against the /api/handleErrors endpoint on the same server, silently spawning hidden child processes to stay out of sight.
Once the second downloader is active, StoatWaffle deploys both its Stealer and RAT modules at the same time.
The Stealer targets saved browser credentials and cryptocurrency wallet extension data across Chromium-based and Firefox browsers; on macOS, it also collects the Keychain database.
The RAT module awaits commands from the C2 server and can list files, run shell commands, upload directories, and search for files matching a keyword — giving the attacker wide and persistent control over the infected host.
Developers should avoid trusting unfamiliar or unverified VSCode repositories, particularly those related to blockchain or cryptocurrency work.
VSCode workspace trust settings should be reviewed carefully, and policies restricting runOn: folderOpen behavior should be enforced. Security teams are advised to block these indicators of compromise: 185[.]163.125.196, 147[.]124.202.208, 163[.]245.194.216, 66[.]235.168.136, and 87[.]236.177.9.
Watching for unexpected Node.js installations or hidden child processes spawned from VSCode can also serve as an early warning of compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.