VoidLink Malware Framework: AI-Assisted Threats Shows Experimental
For years, cybersecurity professionals debated the practical weaponization of AI to build dangerous malware at scale. That debate has now moved past the theoretical. A new report, titled VoidLink is...
For years, cybersecurity professionals debated the practical weaponization of AI to build dangerous malware at scale. That debate has now moved past the theoretical. A new report, titled
VoidLink is far from a basic tool. It features a modular command-and-control (C2) architecture, eBPF and LKM rootkits, cloud and container enumeration capabilities, and more than 30 post-exploitation plugins.
Its technical quality is so high that analysts who first reviewed the framework believed it was the product of a coordinated, multi-person engineering team that had worked intensively over several months.
That assumption proved wrong, and the true origin of VoidLink changed what security teams understood about AI-generated threats.
Check Point analysts identified VoidLink in January 2026 and uncovered a critical finding: the entire framework was built by a single developer using TRAE SOLO, the paid tier of ByteDance’s AI-powered integrated development environment.
An operational security failure by the developer exposed internal development artifacts, revealing how this advanced malware was actually created.
Those leaked materials showed a disciplined, AI-driven engineering process that produced results indistinguishable from professional software development.
The framework reached its first functional implant around December 4, 2025, just one week after development began. In that short window, the developer produced over 88,000 lines of functional code — work that would have traditionally required three teams and roughly 30 weeks to complete.
The implications are serious: a single threat actor armed with the right knowledge and AI tools can now build enterprise-grade malware in days, dramatically lowering the barrier for sophisticated attacks.
The broader impact extends beyond Linux environments. VoidLink signals that the cybercrime ecosystem is borrowing directly from the same engineering practices used by legitimate software development teams.
Check Point Research’s analysis of generative AI activity across corporate networks found that one in every 31 prompts carried a high risk of sensitive data leakage, affecting roughly 90% of organizations that regularly use AI tools.
The Spec Driven Development Workflow Behind VoidLink
What makes VoidLink stand out is not just what it does, but how it was built.
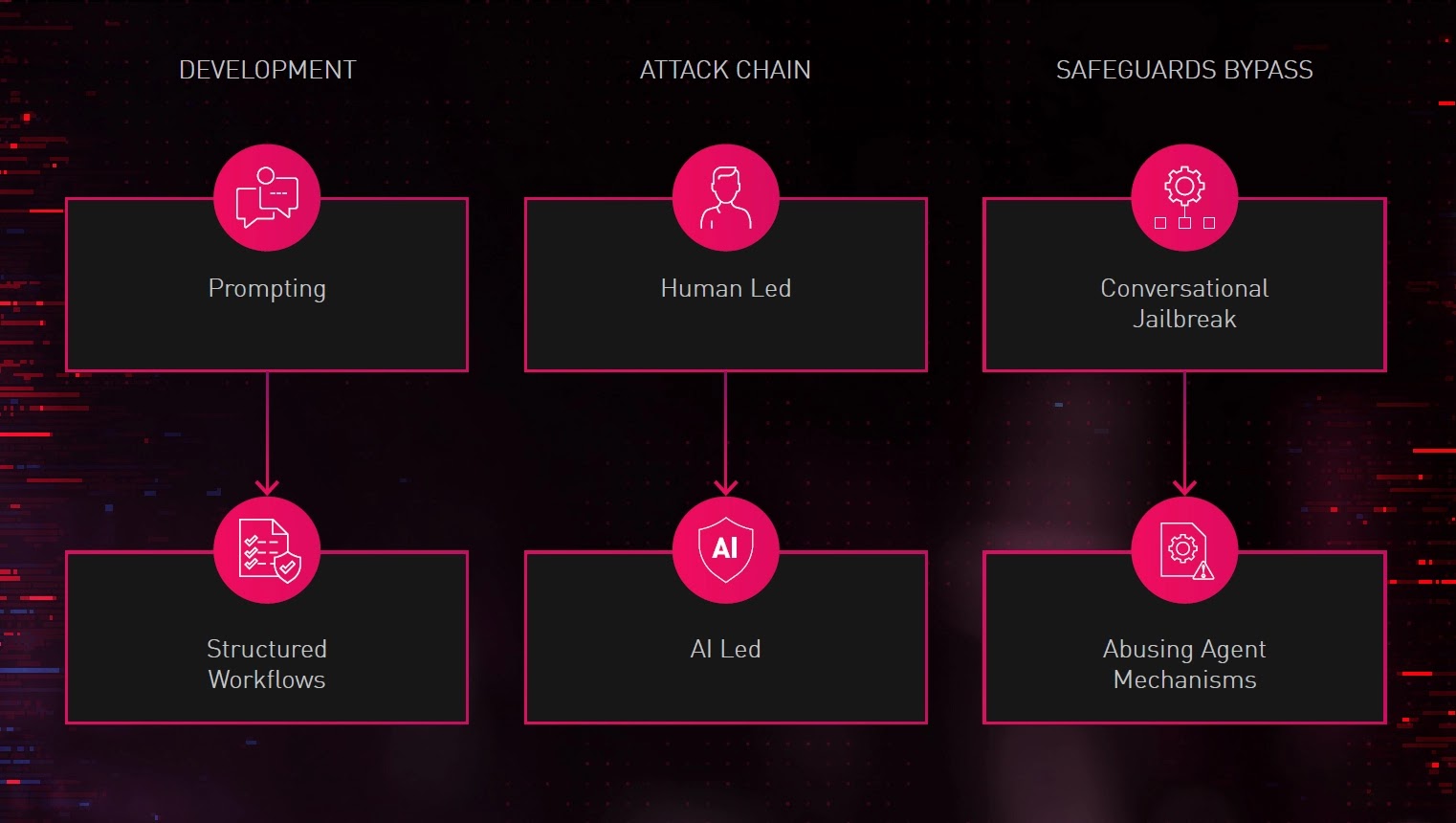
Rather than relying on simple AI prompts, the developer used a method called Spec Driven Development (SDD) — a structured workflow in which detailed project specifications are written first, and an AI agent then implements the code autonomously based on those instructions.
The developer organized the project around three virtual teams: Core, Arsenal, and Backend. Structured markdown files defined goals, sprint schedules, feature breakdowns, coding standards, and acceptance criteria for each team.
The AI agent worked sprint by sprint, producing functional and testable code at every stage. The developer served purely as a product owner — directing, reviewing, and refining — while the AI handled the actual implementation work.
The recovered source code matched the specification documents so precisely that analysts had little doubt the entire codebase was written directly to those instructions.
This contrasts sharply with the unstructured prompting common on cybercrime forums, where actors simply ask AI models for malware as if entering a search query.
SDD demands deep security knowledge, but when combined with a capable AI agent, it delivers output that performs like the work of a seasoned engineering team.
Security teams should treat AI involvement in malware development as a default working assumption, even when there are no obvious indicators.
Organizations are recommended to strengthen monitoring of Linux environments, review endpoint detection rules for eBPF and LKM rootkit behavior, apply strict governance over AI tool usage within corporate networks, and regularly audit cloud and container security configurations.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.