VoidLink Cloud-Native Malware Attacks Linux with Self
A new cloud-focused malware framework, dubbed VoidLink, is now targeting Linux systems. It leverages advanced evasion techniques and self-deletion capabilities. Written in the Zig programming...
A new cloud-focused malware framework, dubbed VoidLink, is now targeting Linux systems. It leverages advanced evasion techniques and self-deletion capabilities.
Written in the Zig programming language, this malware represents a major shift in how threat actors approach cloud infrastructure attacks.
VoidLink stands out for its ability to recognize major cloud environments like AWS, GCP, Azure, Alibaba, and Tencent, then customize its behavior to match each platform.
The framework can detect when it runs inside Kubernetes or Docker containers and adjusts its tactics accordingly.
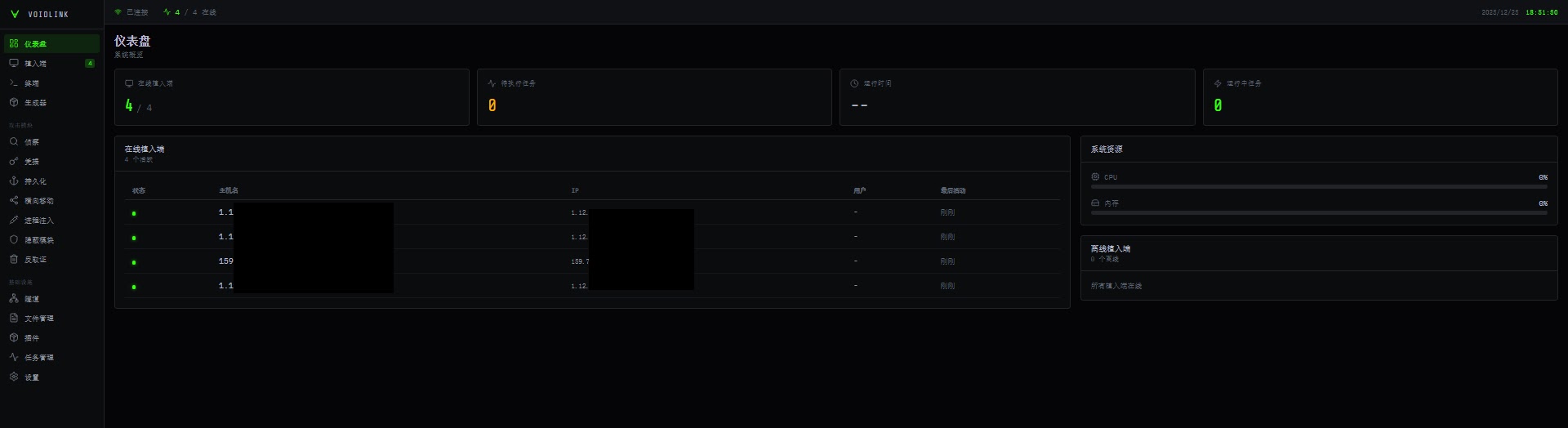
Check Point researchers identified this previously unknown Linux malware in December 2025 after discovering several samples containing debug symbols and development artifacts.
The samples appeared to come from a Chinese-speaking development environment, suggesting the framework was still under active development rather than being a finished product.
The malware targets software engineers and administrators who manage cloud infrastructure, potentially opening doors for espionage or supply chain attacks.
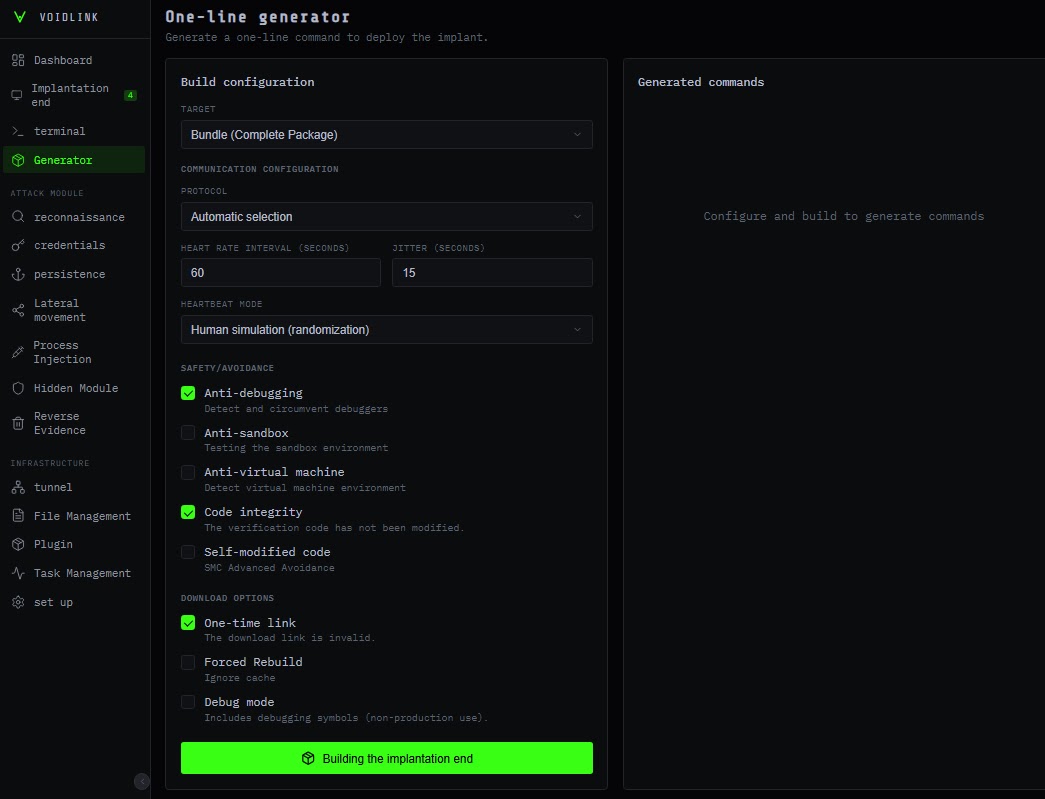
The framework includes more than 37 plugins organized into categories like reconnaissance, credential harvesting, lateral movement, and persistence.
These plugins work as object files that load at runtime and execute directly in memory, similar to how Cobalt Strike‘s Beacon Object Files operate.
VoidLink harvests credentials from cloud environments and version control systems like Git, giving attackers access to sensitive development resources and cloud infrastructure secrets.
Adaptive Stealth and Self-Deletion Mechanisms
VoidLink uses adaptive stealth as its core defense mechanism. When launched, the malware scans for installed security products and kernel hardening technologies, including Linux endpoint detection and response systems.
It then calculates a risk score for the environment and selects the best evasion strategy. In high-risk environments with active monitoring, VoidLink slows down its operations and executes tasks more carefully to avoid detection.
The framework deploys different rootkit types based on the kernel version it detects.
For kernels below version 4.0, it uses LD_PRELOAD techniques. For kernel version 5.5 and higher with eBPF support, it deploys eBPF-based rootkits.
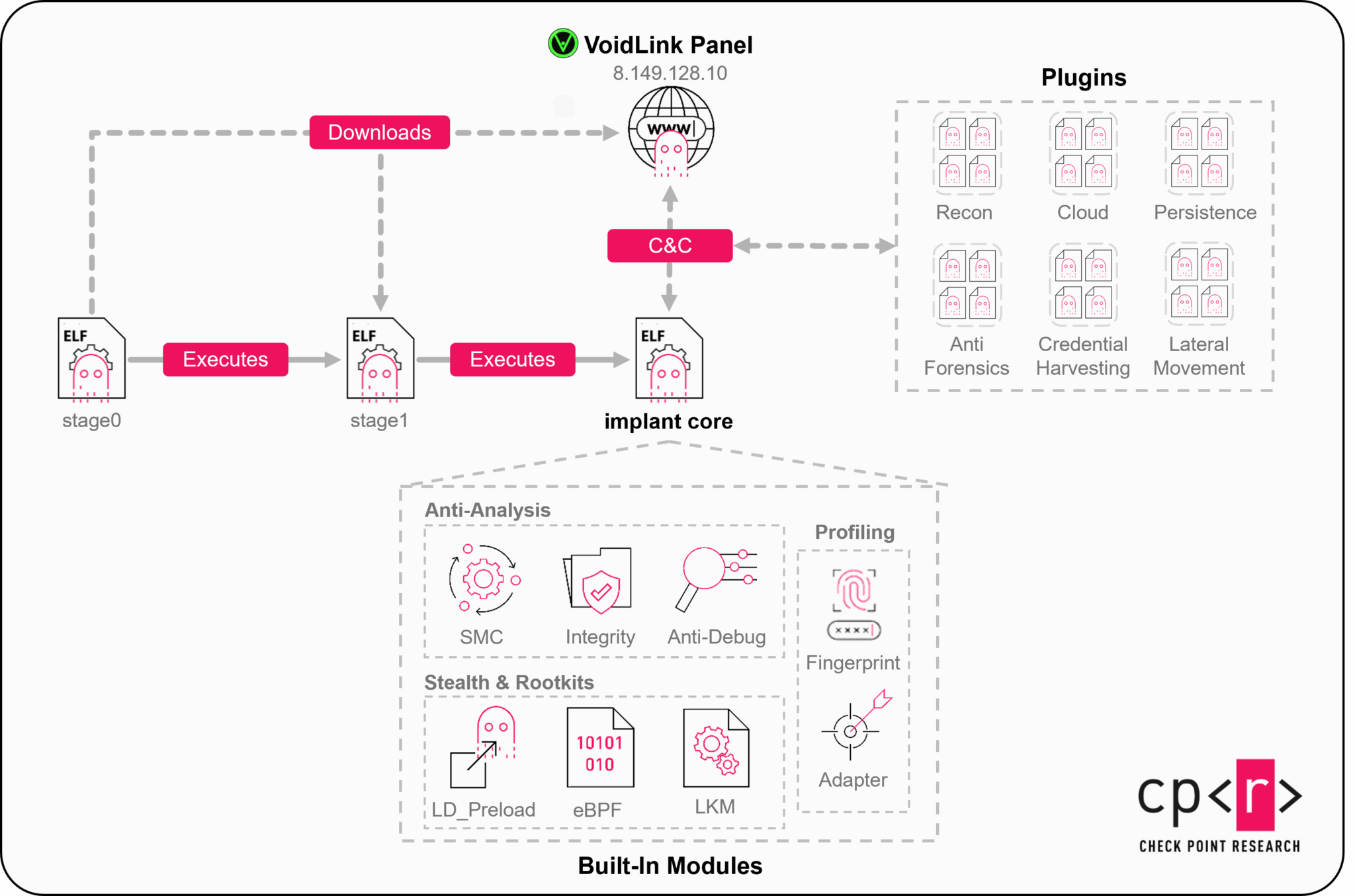
For kernels version 4.0 and above, it installs loadable kernel modules. These rootkits hide processes, files, network sockets, and even the rootkit modules themselves from system administrators and security tools.
VoidLink includes self-modifying code that decrypts protected regions at runtime and encrypts them when not in use.
This technique helps the malware evade memory scanners that look for suspicious code patterns. The framework constantly performs runtime integrity checks to detect hooks and patches that security tools might introduce.
If VoidLink detects any tampering or debugging attempts, it immediately triggers its self-deletion mechanism, removing all traces from the infected system and preventing forensic analysis.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.