Vidar Malware Steals Corporate Credentials via Fake YouTube Downloads
Vidar, a credential-stealing malware, has rapidly become one of the most active threats targeting corporate employees in early 2026. Threat actors are using fake software downloads promoted through...
Vidar, a credential-stealing malware, has rapidly become one of the most active threats targeting corporate employees in early 2026.
Threat actors are using fake software downloads promoted through YouTube videos to trick workers into installing it on their machines, resulting in widespread theft of login credentials, browser data, and cryptocurrency wallet information.
The campaign has caught the attention of security researchers worldwide due to its growing scale and targeted nature.
The rise of Vidar did not happen overnight. Throughout 2025, international law enforcement operations dismantled the infrastructure of two widely used infostealers, Lumma and Rhadamanthys.
As those platforms collapsed, cybercriminals quickly scrambled for a reliable alternative. Vidar’s operators saw the opportunity and released Vidar version 2.0 in October 2025, introducing stronger capabilities and improved evasion techniques.
Since then, Vidar has consistently ranked as the top stealer on the Russian Market, based on the volume of stolen logs uploaded each month.
Intrinsec analysts identified a complete kill-chain while investigating a Vidar compromise that affected a corporate employee at one of their client organizations.
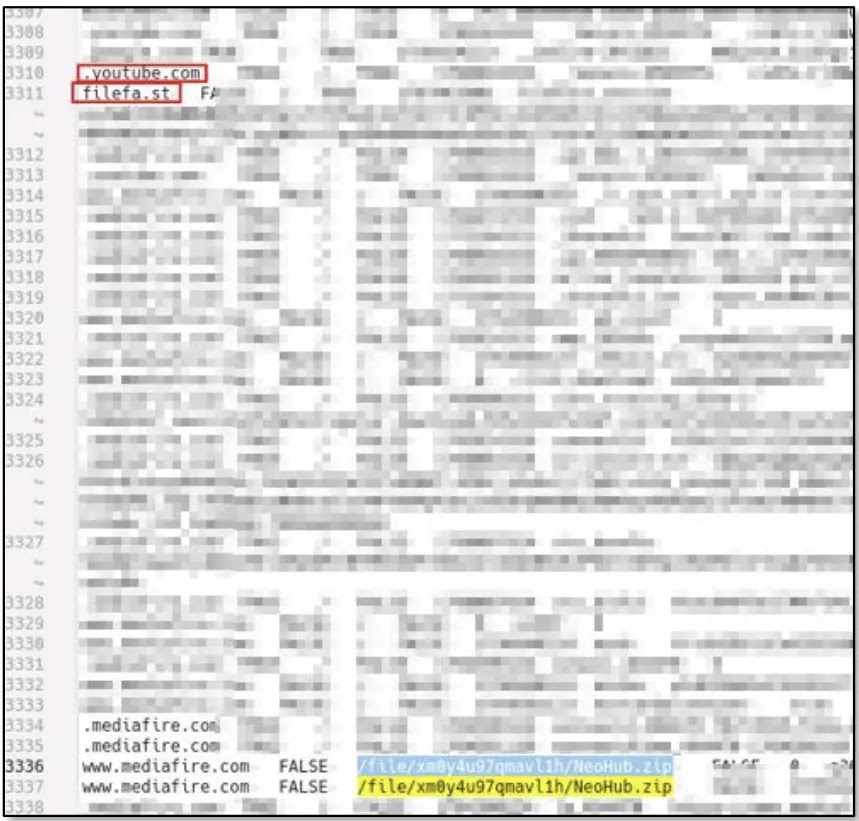
Their analysis showed that the attack started with a YouTube video advertising a fake software tool called NeoHub.
The victim found a link to the file, was redirected through a file-sharing site, and ended up downloading a malicious archive from Mediafire.
The entire process looked like a normal software installation. The impact extends well beyond one compromised employee. Vidar has been adopted by a wide range of threat actors, from individual opportunists to organized groups like Scattered Spider.
CISA published a security advisory naming Vidar among the tools used by that group. Stolen credentials are then sold on Russian Market, putting corporate networks and internal accounts at serious risk.
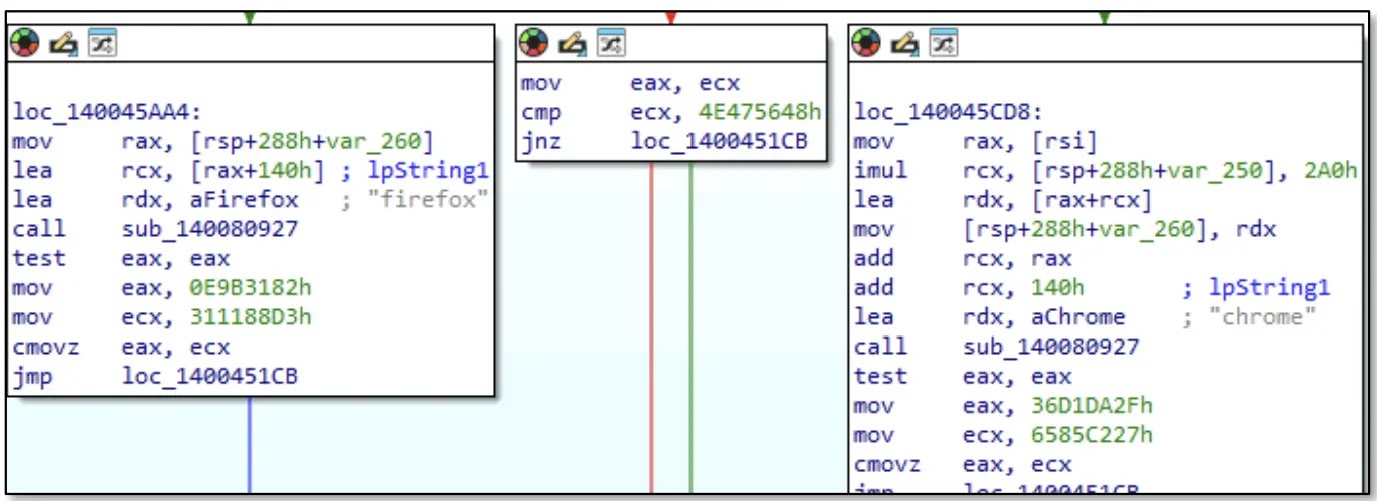
The malware targets Chrome, Firefox, Edge, Opera, Vivaldi, Waterfox, and Palemoon, collecting passwords, cookies, credit card data, and cryptocurrency wallet files.
The Infection Mechanism: A Carefully Staged Attack
The kill-chain behind this campaign is built to avoid suspicion from start to finish. After the victim downloads the archive from Mediafire, they are presented with what appears to be a standard software package.
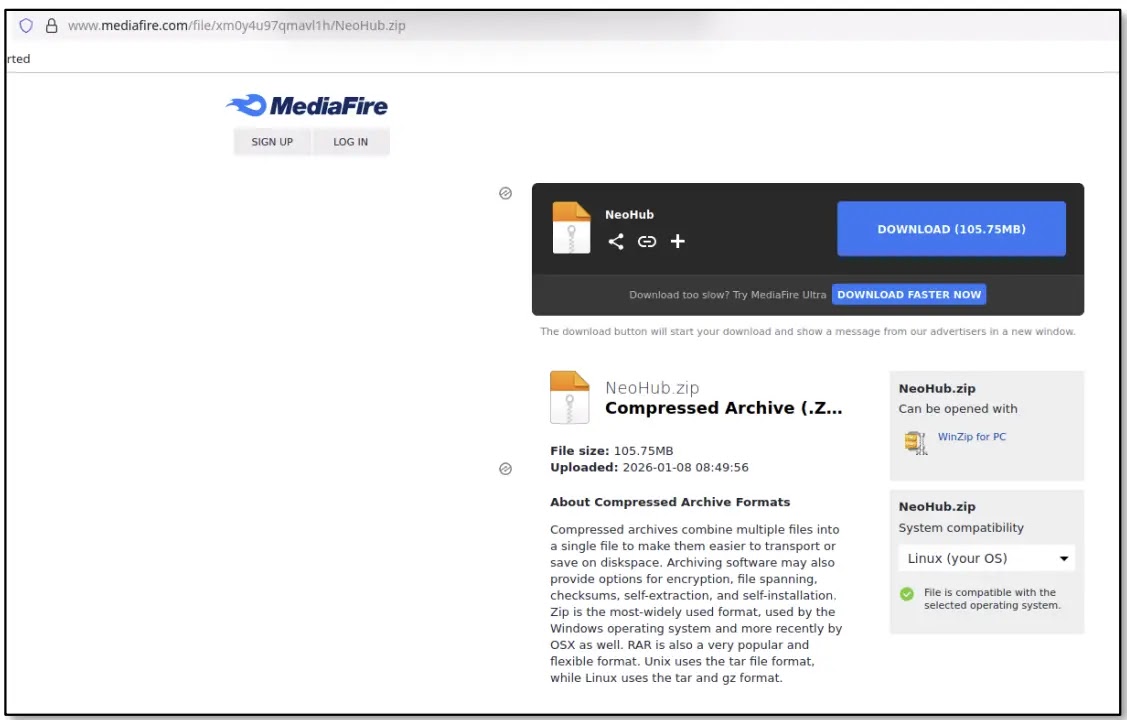
The most visible file is NeoHub.exe, which looks like a normal installer. In reality, this executable secretly loads a second file named msedge_elf.dll, which carries the actual Vidar payload.
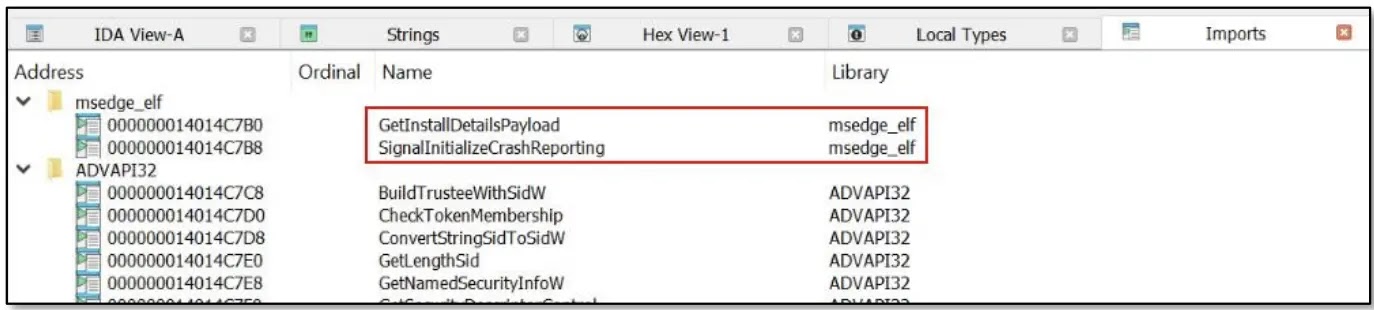
Together, both files work in sync to quietly launch the infection. The msedge_elf.dll file was built to mimic a genuine Microsoft Edge browser component, making it harder to spot during a quick review.
To add another layer of believability, the file was signed using a fake code-signing certificate. The first version impersonated GitHub under the name “githab.com”, and a later version impersonated grow.com.
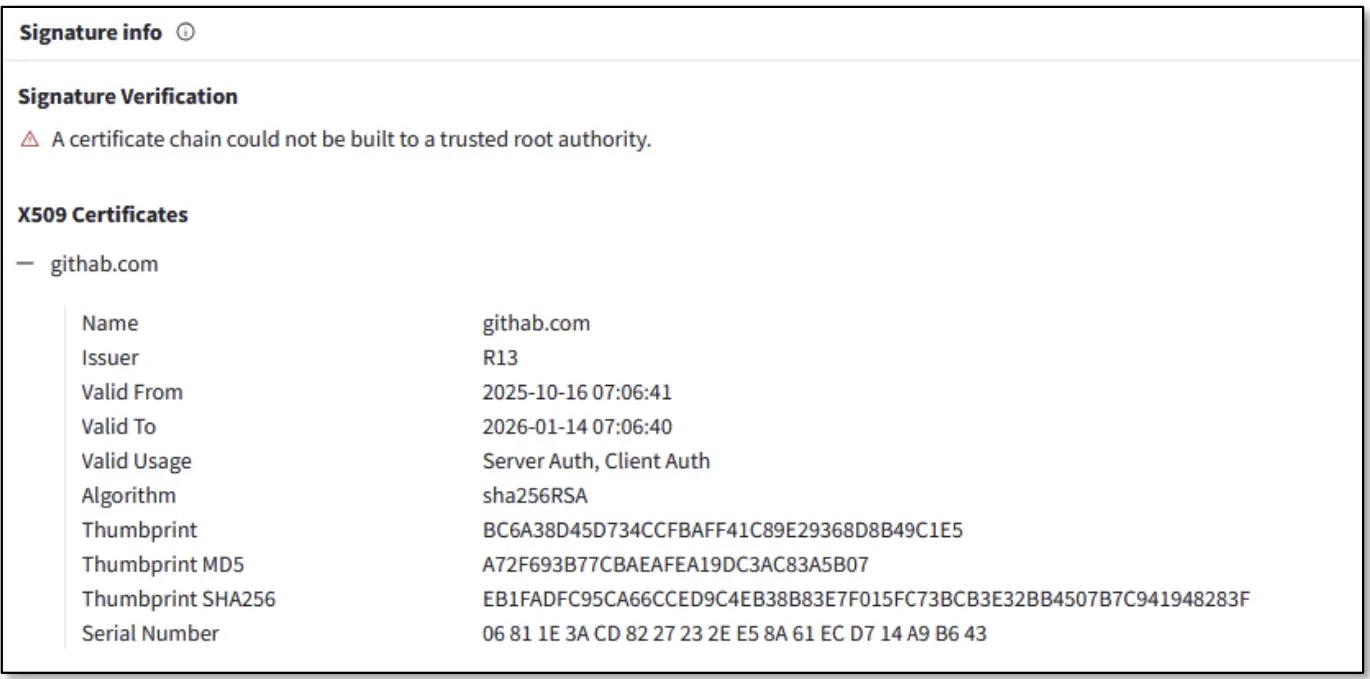
Both certificates were tied to multiple other malicious files, pointing to either a shared threat actor or a third-party service generating counterfeit signatures.
The malicious DLL is packed using a GO-based packer with unusual section names and control flow flattening. This method deliberately breaks the code’s natural structure, making it very hard for security tools and analysts to examine.
Once running on the victim’s machine, Vidar uses a Dead Drop Resolver to locate its command-and-control server. Rather than hardcoding a C2 address, the malware hides the real server location inside public Steam profiles and Telegram channels, giving attackers the ability to rotate infrastructure quickly without updating the malware itself.
Organizations should train employees to avoid downloading software through YouTube video links or unknown file-sharing websites. Multi-factor authentication (MFA) should be enabled on all browser-linked accounts to lower the risk of credential theft.
Security teams are advised to block malicious domains and IP addresses using published indicators of compromise, and set up network monitoring to catch unusual outbound connections to unknown C2 servers.
Secure Web Gateways and DNS filtering can stop malicious redirections before they reach users. Sandboxing downloaded files before execution adds a critical layer of defense.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.