Unprotected Database Exposes 48M Gmail, Instagram Exposed
A vast database containing 149 million stolen login credentials was recently discovered exposed online. Critically, the massive trove of sensitive data remained entirely unsecured, lacking any...
A vast database containing 149 million stolen login credentials was recently discovered exposed online. Critically, the massive trove of sensitive data remained entirely unsecured, lacking any password protection or encryption. This significant exposure presents a considerable risk, potentially enabling widespread account compromise for affected individuals.
Posing serious security risks to users of Gmail, Instagram, Facebook, Netflix, and thousands of other platforms worldwide.
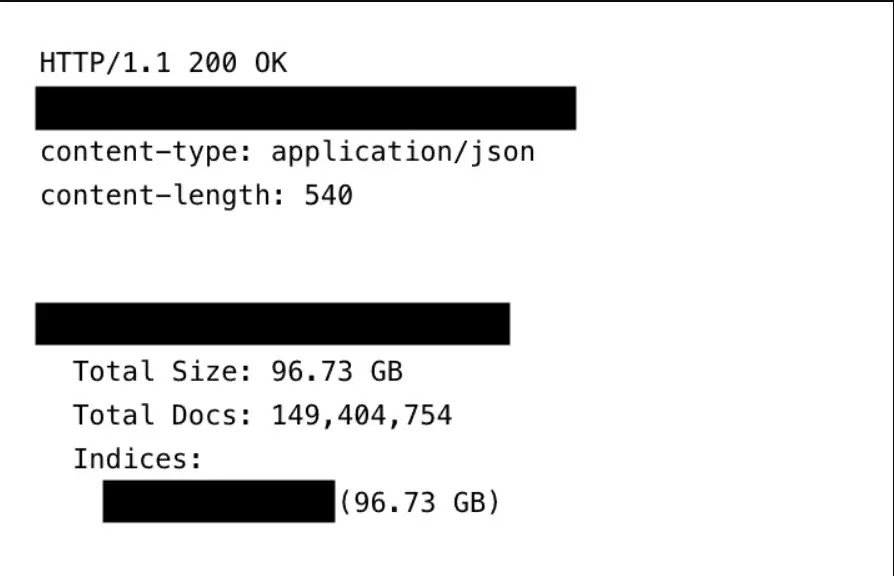
The publicly accessible database contained 149,404,754 unique logins and passwords harvested through infostealer malware and keylogging software.
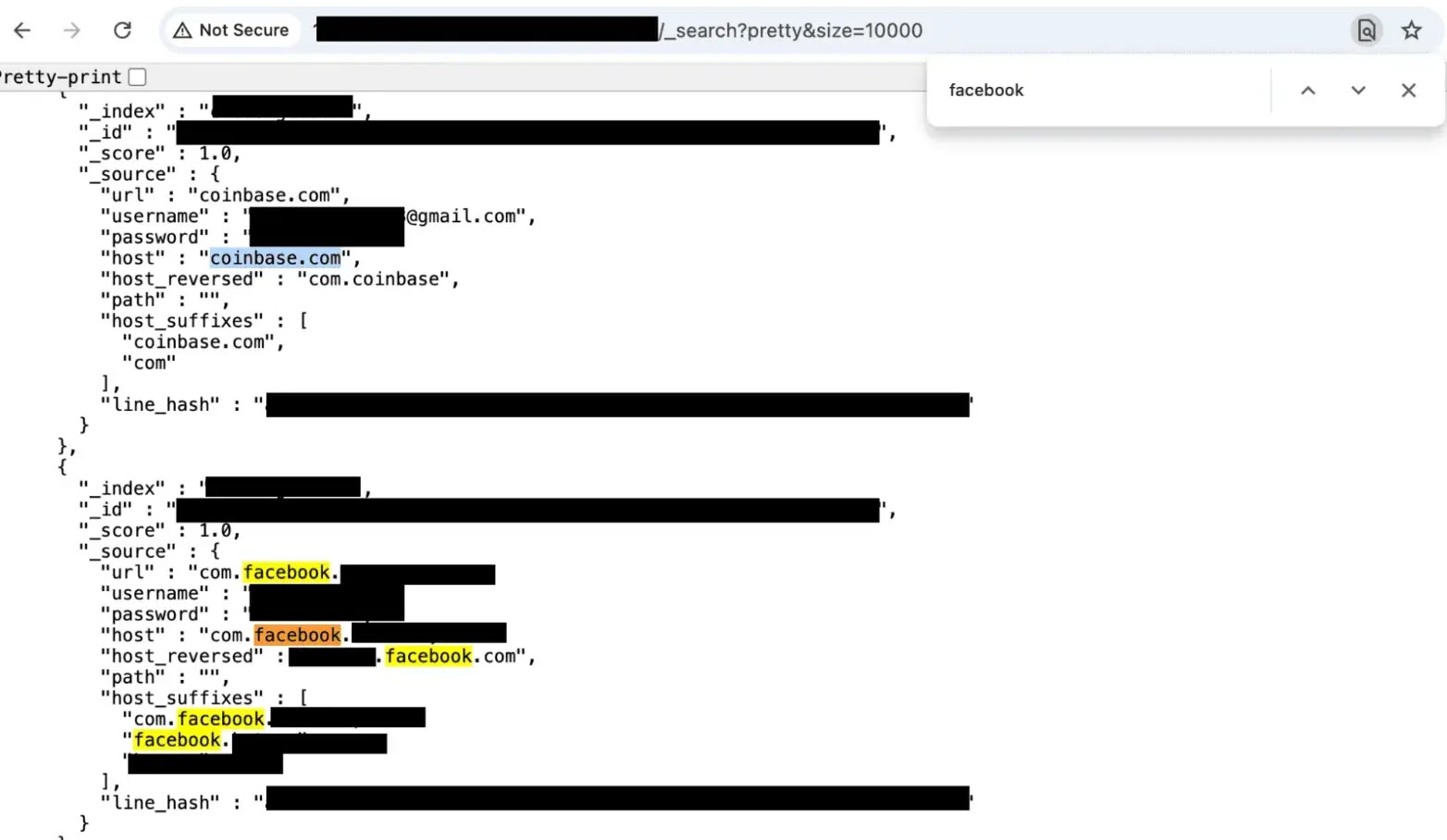
Each record included email addresses, usernames, passwords, and the exact URL links for account authorization.
This provides cybercriminals with everything they need to execute automated credential-stuffing attacks against millions of victims who may not realize their information has been compromised.
Breakdown of Exposed Accounts
A limited sampling of the exposed data revealed alarming statistics across major email providers and popular platforms.
Approximately 48 million Gmail accounts were compromised, alongside 4 million Yahoo accounts, 1.5 million Outlook accounts, 900,000 iCloud accounts, and 1.4 million .edu email addresses from educational institutions.
Social media platforms sustained substantial exposure, with 17 million Facebook credentials, 6.5 million Instagram logins, and 780,000 TikTok accounts appearing in the dataset.
Entertainment streaming services were heavily affected, including 3.4 million Netflix accounts, while financial platforms showed 420,000 Binance cryptocurrency accounts exposed.
The database even contained 100,000 OnlyFans credentials, affecting both content creators and subscribers.
Particularly concerning was the presence of credentials associated with .gov domains from numerous countries.
While not every government account grants access to classified systems, even limited access could enable targeted spear-phishing campaigns and impersonation attacks.
Serve as entry points into government networks, posing national security and public safety risks.
The database also included banking logins, credit card credentials, crypto wallet access, and trading account information.
The records contained structured metadata including “host_reversed path” formatting (com.example.user.machine) to organize stolen data by victim and source, with unique line hashes serving as document IDs to prevent duplicates.
Delayed Response and Growing Threat
Cybersecurity researcher Jeremiah Fowler uncovered the 96 GB repository and reported his findings to ExpressVPN as part of ongoing efforts to highlight critical data exposure threats.
After discovering the exposure, Fowler reported it directly to the hosting provider through their abuse form.
The response was delayed, with the provider initially claiming they did not host the IP address and that a subsidiary operated independently.
It took nearly one month and multiple attempts before the database was finally suspended and removed from public access.
Disturbingly, the number of records increased between initial discovery and final restriction, indicating ongoing data collection during the exposure period.
The hosting provider refused to reveal who owned the database, leaving uncertainty over its purpose, exposure duration, and potential access by others.
Security experts recommend installing antivirus software immediately, with a 2025 report showing that only 66 percent of U.S. adults use such protection.
Users should enable two-factor authentication across all accounts, utilize password managers with unique credentials for each service, and monitor login histories for unauthorized access attempts.
Anyone who suspects device infection should immediately update operating systems, scan for malware, and review app permissions and browser extensions.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.