Trivy Compromise: Script Injection Steals Credentials
A sophisticated supply chain attack has globally compromised continuous integration and continuous deployment (CI/CD) pipelines. This incident specifically targeted the official Trivy GitHub Action,...
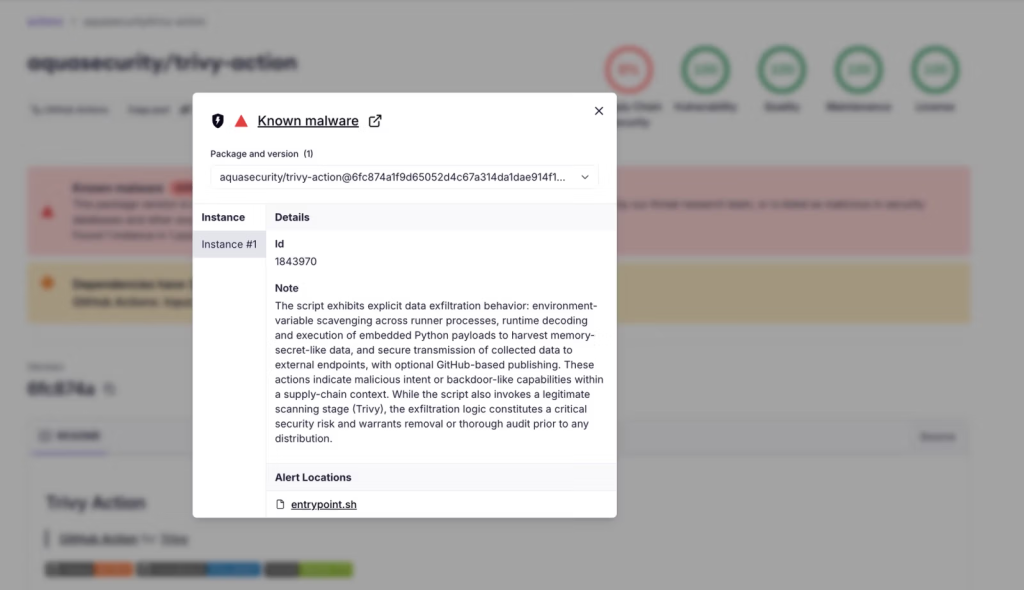
A sophisticated supply chain attack has globally compromised continuous integration and continuous deployment (CI/CD) pipelines. This incident specifically targeted the official Trivy GitHub Action, identified as aquasecurity/trivy-action.
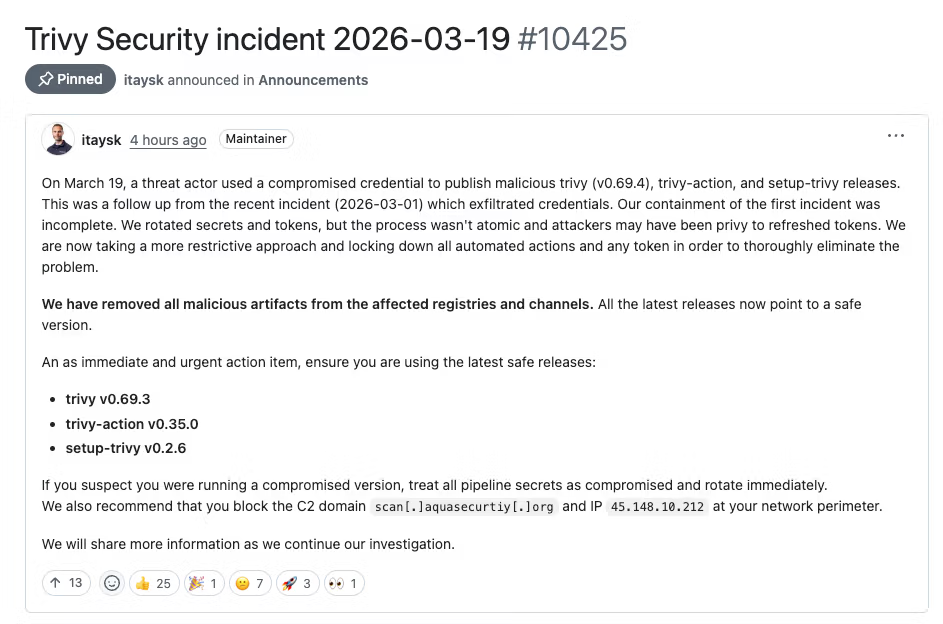
Disclosed in late March 2026, this incident marks the second distinct compromise affecting the Trivy ecosystem within a single month.
Threat actors successfully force-pushed 75 out of 76 existing version tags to distribute a malicious infostealer. With over 10,000 GitHub workflow files relying on this action, the potential credential theft blast radius is massive.
Mechanics of the Tag Poisoning Attack
Instead of pushing code to a branch or creating a new release, the attacker leveraged residual write access from an earlier credential breach to alter existing version tags silently.
The threat actor force-pushed 75 tags, including widely used versions like @0.33.0 and @0.18.0, to point to newly forged commits.
This effectively turned trusted and supposedly immutable version references into a direct distribution mechanism for their custom infostealer malware.
By completely bypassing the need to create new releases, the attacker minimized the chances of triggering automated security alerts or notifying project maintainers of unauthorized branch updates.
To evade detection, the attacker spoofed the Git commit metadata. They cloned the original author names, dates, and commit messages to make the malicious commits appear legitimate in the repository logs.
The modified code used the current master file tree but swapped the legitimate entrypoint.sh file with an infected version.
Because the malicious commit dates conflicted with the March 2026 parent commit, and the commits lacked GitHub’s web-flow GPG signature, careful inspection reveals the forgery. Notably, version @0.35.0 remained untouched and is the only safe tag.
The injected 204-line entrypoint.sh script executes its malicious operations before running the legitimate Trivy scan, allowing it to hide in plain sight.
According to Socket, the infostealer operates in three distinct stages: targeted collection, robust encryption, and stealthy exfiltration.
During the collection phase, the malware targets both GitHub-hosted and self-hosted runners. On GitHub-hosted Linux environments, it uses passwordless sudo privileges to dump the Runner.Worker process memory and extract secrets directly from the heap.
On self-hosted runners, a comprehensive Python script scrapes the filesystem for sensitive data across multiple directories.
This script systematically hunts for SSH keys, database credentials, CI/CD configuration files, and even cryptocurrency wallet data, ensuring an extensive haul of valuable information.
In the second stage, the stolen data is compressed and encrypted using AES-256-CBC, and the encryption key is wrapped with an RSA-4096 public key.
Finally, the malware attempts to exfiltrate the encrypted bundle via an HTTPS POST request to a typosquatted domain, scan[.]aquasecurtiy[.]org.
If this primary channel fails, the script uses the victim’s own GitHub Personal Access Token to create a public repository named tpcp-docs and uploads the stolen data as a release asset.
The malware self-identifies as the “TeamPCP Cloud stealer”. Security researchers track TeamPCP as a cloud-native threat actor known for exploiting misconfigured infrastructure for ransomware and cryptomining operations.
Organizations must immediately stop referencing trivy-action by version tags, with the exception of @0.35.0. To ensure complete security, pipelines should pin the action to the specific safe commit SHA (57a97c7e7821a5776cebc9bb87c984fa69cba8f1).
Any environment that executed a poisoned tag must be considered fully compromised. Security teams should urgently rotate all exposed secrets, including cloud credentials and API tokens.
Additionally, administrators should audit their GitHub organizations for unauthorized tpcp-docs repositories.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.