TrickMo Android Malware Targets Banking & Wallet Apps
A formidable Android banking malware, TrickMo, has resurfaced with a potent new variant. This updated iteration is significantly more stealthy, capable, and challenging to counter than its...
A formidable Android banking malware, TrickMo, has resurfaced with a potent new variant. This updated iteration is significantly more stealthy, capable, and challenging to counter than its predecessors, according to a recent
The malware spreads through fake TikTok apps distributed via Facebook campaigns and a deceptive app disguised as “Live Streaming.”
Once installed, TrickMo tricks users into granting accessibility permissions, which then gives the attacker complete control over the device. From that point forward, the victim’s phone essentially becomes a tool in the hands of a criminal operator.
Analysts at ThreatFabric identified and began tracking this new TrickMo variant between January and February 2026, noting it as a deliberate platform overhaul rather than a completely new malware family.
Their Mobile Threat Intelligence Team observed active campaigns targeting banking and wallet customers in France, Italy, and Austria, with signs pointing to this new strain gradually replacing its older predecessor across operator campaigns.
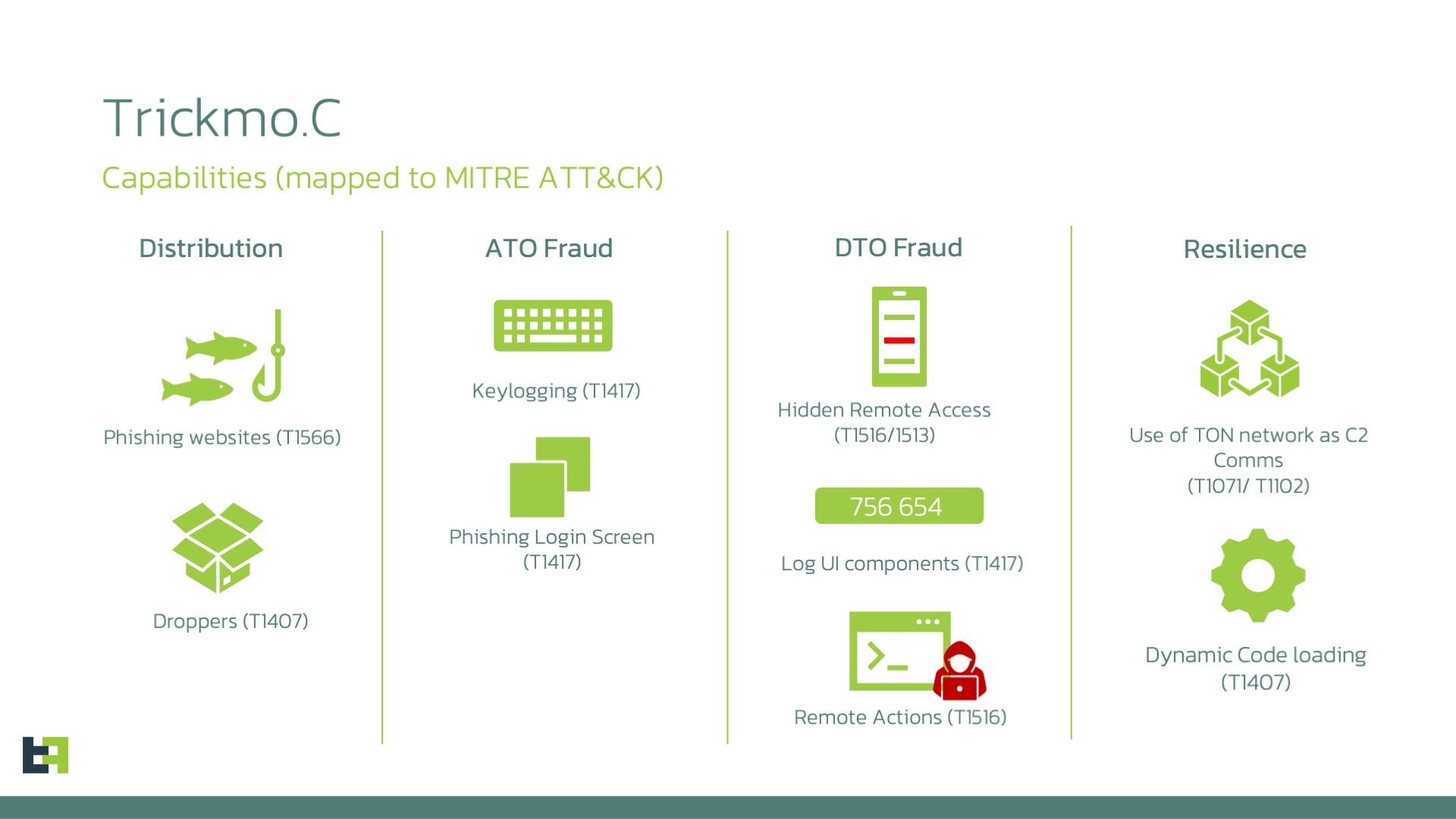
What makes this version especially alarming is that it does not just steal credentials. It records screens, logs keystrokes, intercepts SMS messages, and silently suppresses one-time password notifications before the user ever sees them. The attacker can watch the screen live, replay gestures, and interact with the device in real time, making fraudulent transactions far harder to detect.
The new variant also transforms infected devices into programmable network nodes. Through built-in SSH tunnelling and an authenticated on-device SOCKS5 proxy, a compromised phone routes malicious traffic while appearing to originate from the victim’s own network. This effectively tricks fraud detection systems at banks and crypto exchanges into treating suspicious activity as entirely legitimate.
TrickMo’s Expanding Attack Surface
TrickMo is classified as Device Takeover malware, meaning it gives an attacker full interactive control over an infected phone. It achieves this by abusing Android’s accessibility service, a built-in feature that, when misused, allows an app to read and interact with everything on screen.
Once active, TrickMo deploys fullscreen fake login pages that closely mimic real banking apps to deceive victims. While the user enters credentials into what they believe is their legitimate app, TrickMo captures every keystroke and sends the data to the attacker in the background.
The malware also intercepts and silently suppresses incoming SMS messages and push notifications, particularly those carrying one-time passwords. This means even two-factor authentication offers limited protection after a device is infected. Users have no visible sign that their messages are being quietly redirected.
Beyond credential theft, TrickMo loads a runtime module called dex.module that delivers its core remote-control engine. This module is fetched from attacker-controlled infrastructure and injected into the running process, making it harder for standard security scans to detect.
Command-and-Control Through the TON Network
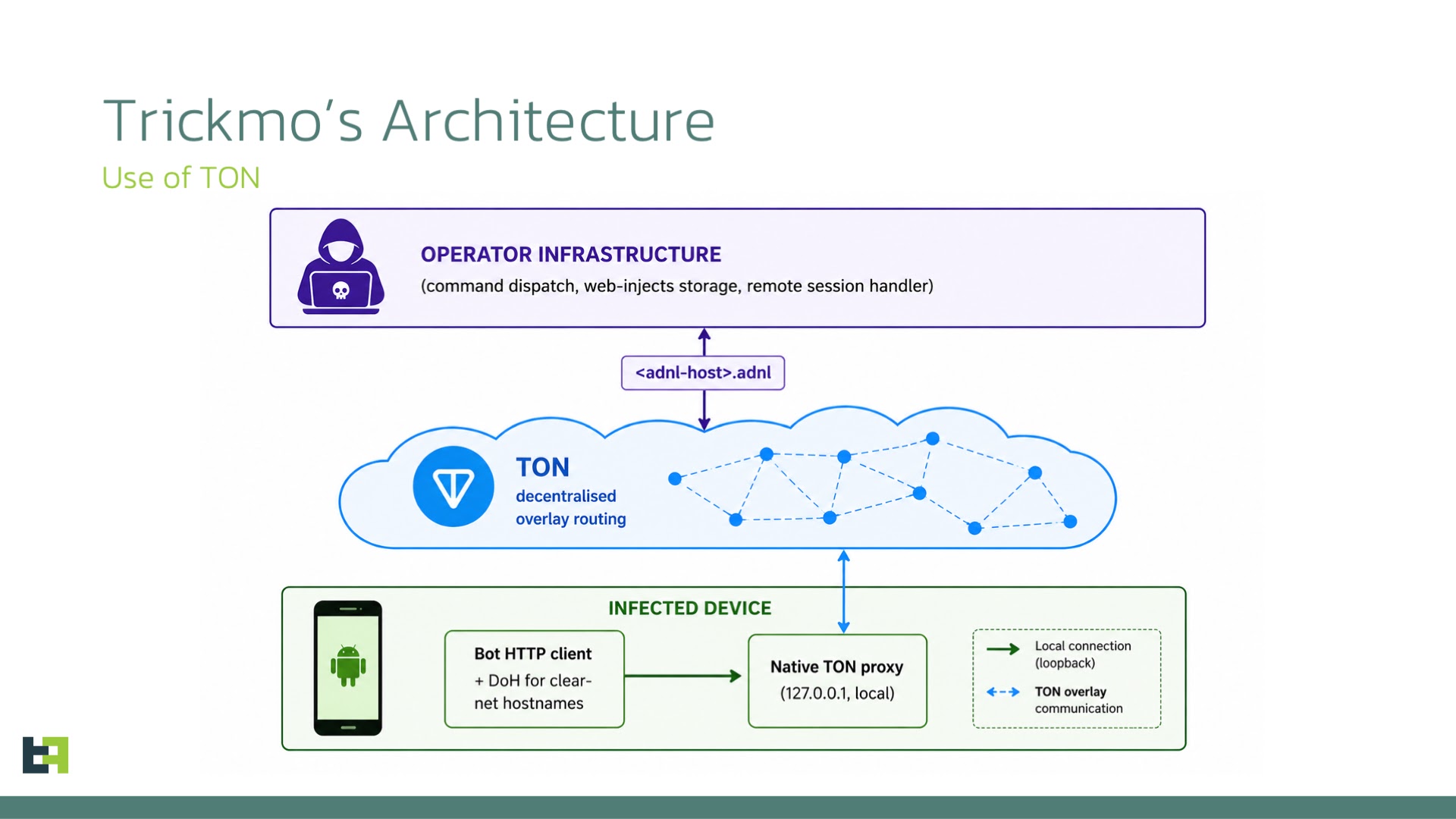
The most significant change in this new variant is how it communicates with operators. Previous versions relied on conventional internet infrastructure, making their command servers easier to locate and shut down. TrickMo now routes all communications through The Open Network, known as TON, a decentralised peer-to-peer overlay.
Instead of connecting to regular web addresses that can be traced and blocked, TrickMo uses .adnl endpoints resolved entirely within the TON network. These addresses do not exist in the public internet’s address system, making traditional domain takedowns largely ineffective. Security teams cannot cut the connection the way they would with a standard malicious domain.
To further complicate detection, TrickMo replaces the device’s DNS resolver with a DNS-over-HTTPS service for any remaining clearnet connections. This hides the domains the malware queries from network monitoring tools. The traffic produced blends seamlessly with other legitimate TON activity, making it very difficult to spot at the network level.
Users can protect themselves by avoiding sideloaded apps, never granting accessibility permissions to unfamiliar applications, and keeping their Android devices regularly updated.
Financial institutions are strongly urged to deploy mobile threat detection capable of identifying anomalous accessibility usage and unusual outbound tunnelling behaviour on customer devices.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-256 | 01889a9ec2abecb73e5e8792be68a4e3bc7dcbe1c3f19ac06763682d63aa8c21 | TrickMo Dropper — com.app16330.core20461 (TikTokApp18+) |
| SHA-256 | 177ef86c57c31b29850227dbc8288b735bea977587f2f0a49cfc4089a644a2c4 | TrickMo Dropper — com.app15318.core1173 (TikTokApp18+) |
| SHA-256 | e2e218ddf698b4c0099fd2a9619d6912a71f75beb51669a4e3ae4fc71f745d03 | TrickMo Host Application — uncle.collop416.wifekin78 (Google Play Services) |
| SHA-256 | 749bbcbc3e5d2d524344d52b6471dfa7b8d3ecdeb0b11ab82c843d497a056c8f | TrickMo Host Application — nibong.lida531.butler836 (Google Play Services) |
| SHA-256 | 143c0e12d2aa1bdecde59f273139dd5605d00f61cda7f626224e07390119c026 | Dex Module (old variant) — dex.module |
| SHA-256 | 4cd8635062ff6b0885216a0b1658ebcb2938b670f7ac08ecb0b5fb85d8973ea0 | Dex Module (new variant) — dex.module |
| Package Name | com.app16330.core20461 | TrickMo Dropper disguised as TikTokApp18+ |
| Package Name | com.app15318.core1173 | TrickMo Dropper disguised as TikTokApp18+ |
| Package Name | uncle.collop416.wifekin78 | TrickMo Host Application disguised as Google Play Services |
| Package Name | nibong.lida531.butler836 | TrickMo Host Application disguised as Google Play Services |
| Package Name | dex.module | Runtime-loaded offensive DEX module |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.