Transparent Tribe Attacks India’s Startup Ecosystem in New Campaign
Transparent Tribe, a persistent advanced threat group, has initiated a new cyber campaign directly targeting India’s burgeoning startup ecosystem. This marks an unexpected escalation in the...
Transparent Tribe, a persistent advanced threat group, has initiated a new cyber campaign directly targeting India’s burgeoning startup ecosystem. This marks an unexpected escalation in the threat landscape facing the nation’s technology sector.
A Pakistan-based hacking group called Transparent Tribe has shifted its focus from traditional government targets to the country’s vibrant startup ecosystem, particularly companies working in cybersecurity and intelligence domains.
The group, also tracked as APT36, has been active since 2013 and now uses dangerous malware called Crimson RAT to infiltrate Indian startups through carefully crafted fake emails containing malicious files disguised as legitimate documents.
The attack campaign was discovered after researchers found suspicious files uploaded from India containing startup-themed material.
Unlike previous operations that targeted defense organizations and educational institutions, this campaign specifically focuses on individuals connected to startups offering security services to law enforcement agencies.
The hackers used personal information about a real startup founder to create convincing fake documents that appear legitimate to unsuspecting victims.
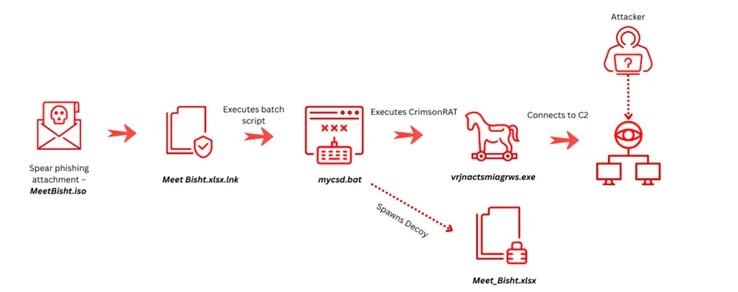
After analyzing the threat, Acronis researchers identified that the group delivers its malware through ISO container files sent via email.
When someone opens what appears to be an Excel spreadsheet, they unknowingly activate a chain of hidden commands that install Crimson RAT on their computer.
This remote access trojan allows hackers to monitor screens, record audio, steal files, and control infected systems without the victim’s knowledge.
Attack Execution and Stealth Mechanisms
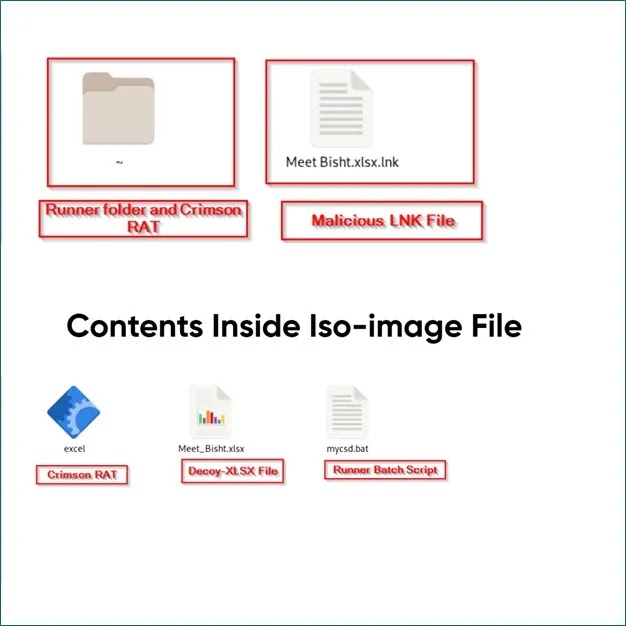
The infection process begins when victims receive an email containing a file called MeetBisht.iso.
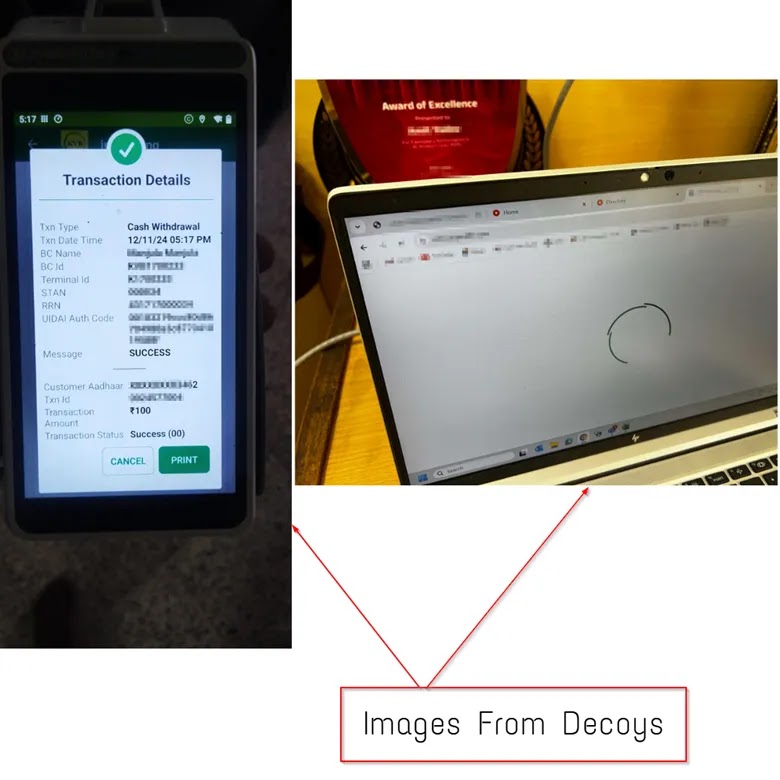
Inside this container sits a shortcut file masquerading as an Excel document alongside a hidden folder containing three components: a decoy document to distract the victim, a batch script that handles execution, and the actual Crimson RAT payload disguised as an excel executable.
Once activated, the malicious shortcut launches a batch script that simultaneously displays a fake Excel file while secretly copying the malware to the computer’s system folders.
The script uses PowerShell commands to remove security warnings that would normally alert users about suspicious files.
It then creates a hard-linked executable with a random name in the user’s application data folder and launches the malware from this trusted location.
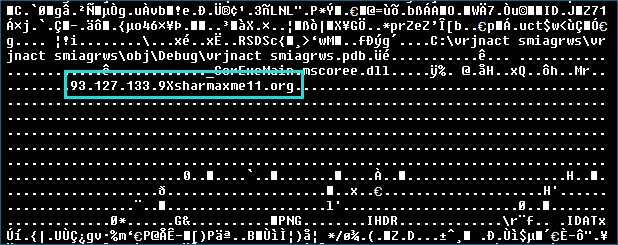
The Crimson RAT payload employs sophisticated evasion tactics. The malware file appears artificially inflated to 34 megabytes through embedded junk data, though the actual malicious code measures only 80 to 150 kilobytes.
This bloating technique helps bypass signature-based detection systems. The malware uses completely randomized function names throughout its code, making analysis extremely difficult.
It communicates with command-and-control servers using custom TCP protocols on non-standard ports including 18661, 20856, 26868, 29261, and 36628.
Organizations should implement email filtering to block ISO and container-based attachments from unknown sources.
Regular security awareness training helps employees recognize social engineering tactics. Deploying endpoint detection solutions can identify suspicious PowerShell activity and unauthorized file modifications.
Network monitoring should flag unusual outbound connections to non-standard ports used by Crimson RAT.
Maintaining updated threat intelligence feeds ensures protection against known command-and-control servers associated with Transparent Tribe campaigns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.