FvncBot Exploits Android Accessibility Services to Attack
A new malicious application has emerged, targeting mobile banking customers in Poland. Identified on November 25, 2025, this threat masquerades as a legitimate security tool purportedly from mBank, a...
A new malicious application has emerged, targeting mobile banking customers in Poland. Identified on November 25, 2025, this threat masquerades as a legitimate security tool purportedly from mBank, a major Polish financial institution.
The application serves as a gateway for a novel banking trojan that operates silently in the background.
By mimicking trusted banking software, the attackers successfully deceive users into installing the malware, which then attempts to compromise their financial accounts through sophisticated surveillance techniques.
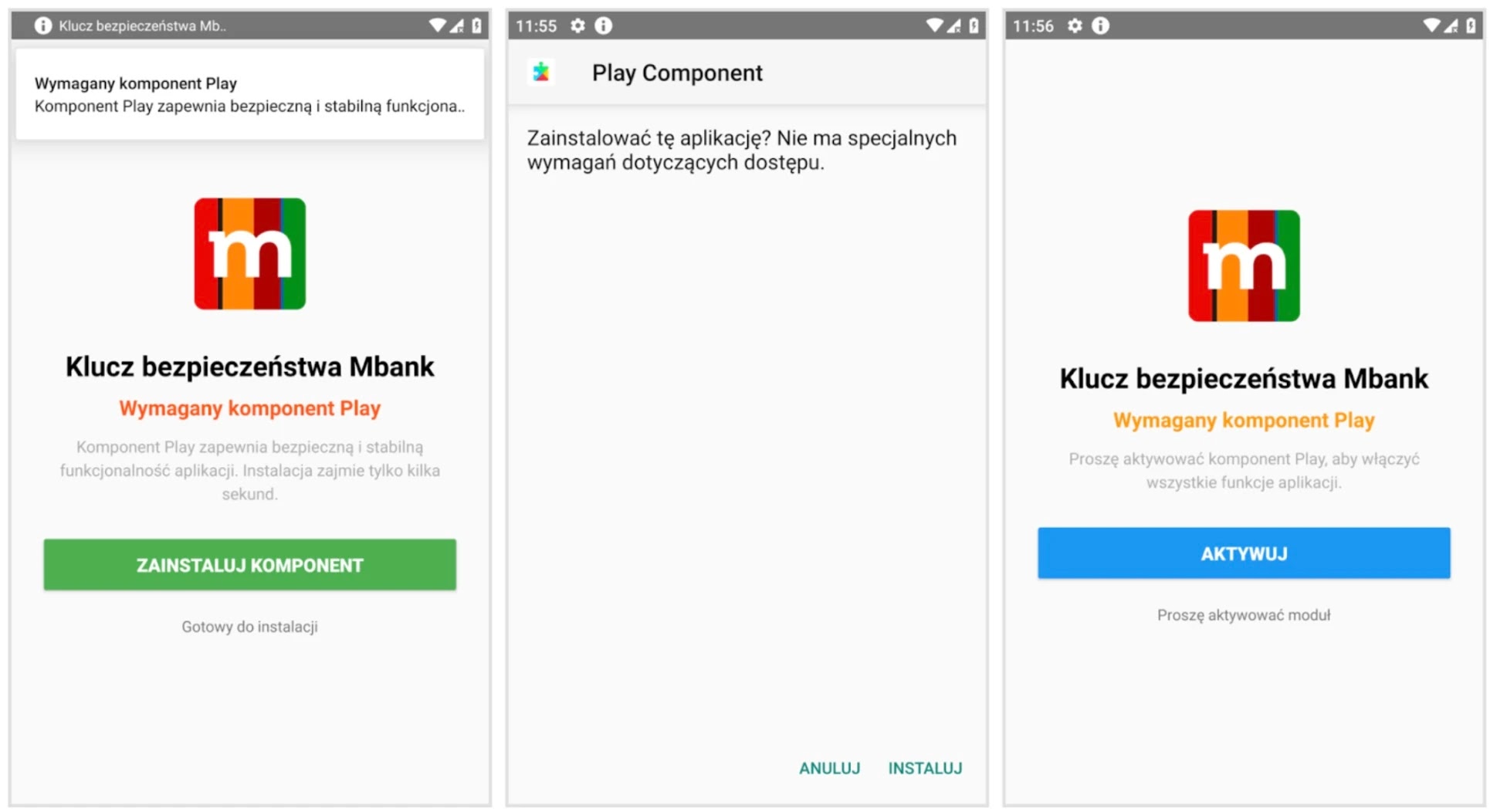
The infection process begins when the fake app prompts the user to install an additional “Play” component, claiming it is required for system stability.
This step is a critical trick designed to bypass security restrictions found on modern Android devices. The malicious loader leverages this permission to deploy the payload, ensuring it can operate persistently on the victim’s phone.
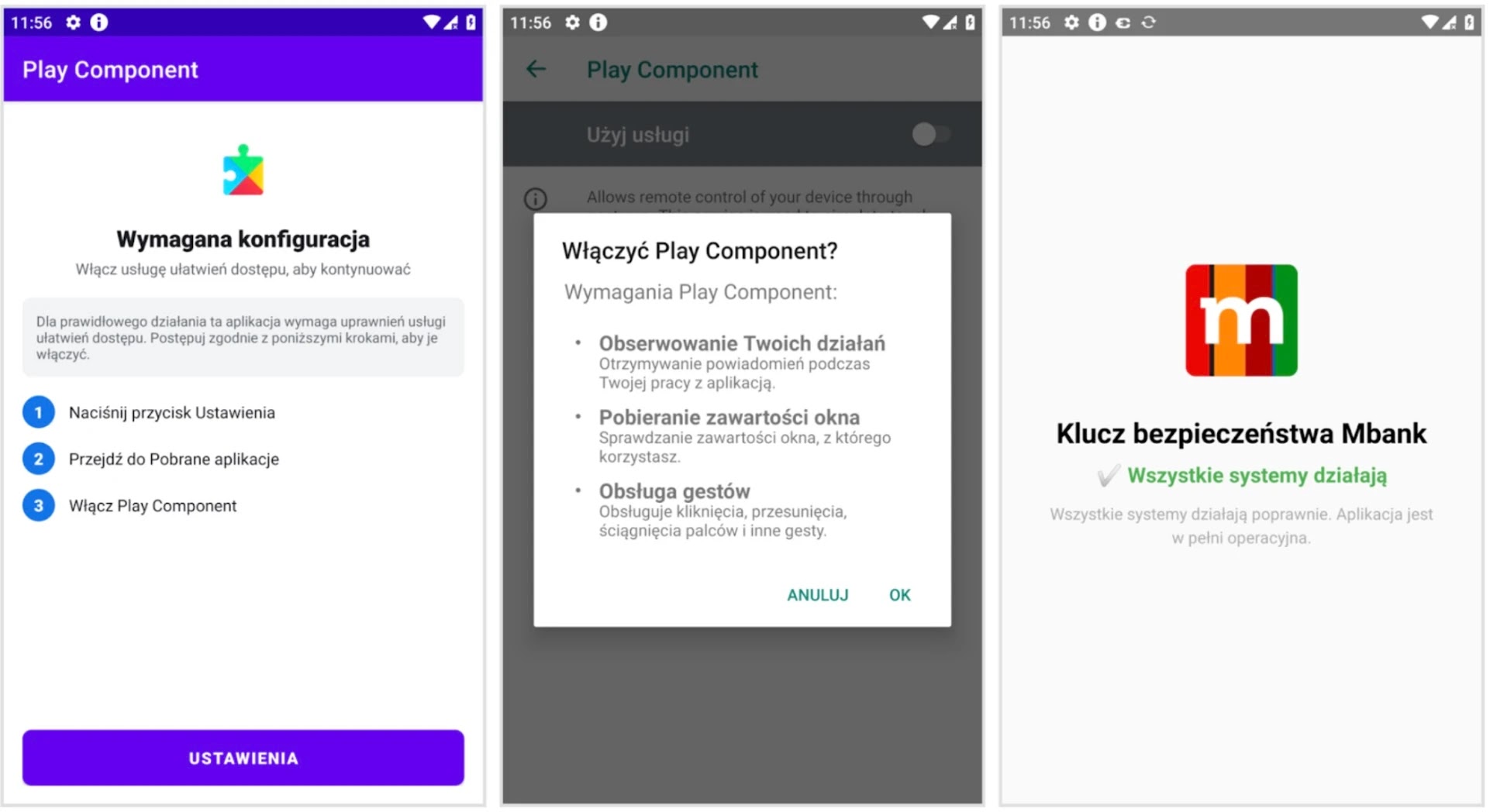
This social engineering tactic effectively lowers the user’s guard, allowing the threat to establish a foothold before any data theft begins.
Intel 471 researchers identified this specific strain and named it FvncBot, noting that its programming code is entirely original and not derived from leaked sources of other notorious banking trojans.
This uniqueness suggests a new group of developers is responsible. FvncBot unleashes invasive features to steal money, primarily by recording keystrokes and capturing screen content.
It also utilizes hidden virtual network computing, which allows cybercriminals to perform actions on the infected device remotely, facilitating fraudulent transfers while the victim remains unaware.
Abusing Accessibility for Persistence
The most alarming aspect of FvncBot is its manipulation of Android’s accessibility services to maintain control. After installation, the malware aggressively requests these high-level privileges, guiding the victim to system settings to approve them.
If the user complies, the malware gains the ability to read text on the screen and track every tap.
With accessibility services enabled, FvncBot can harvest data from any open application, including secure banking portals. It logs these details into a storage buffer and transmits them to a remote server.
Furthermore, the malware establishes a high-speed connection using WebSockets, allowing operators to issue commands instantly.
This setup enables them to stream the victim’s screen and manipulate the device remotely to commit fraud.
To stay safe, users are strongly advised to avoid installing banking applications from unofficial websites and organic search results to prevent such dangerous infections.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.