Top 10 Cyber Attack Maps to Track Digital Threats in
Cyber Attack Maps to Track Digital Threats in
Okay, so it’s 2026, right? And honestly, the whole digital threat landscape? It’s just wild out there. We’re seeing things way more dynamic and complex than ever before. Seriously, cyber attacks aren’t just happening more often; they’re getting smarter, hitting harder, and their impact is just escalating. We’re talking about businesses, governments, even you and me – everyone’s a target, all over the globe.
Table Of Content
- Comparison Table: Top 10 Cyber Attack Maps 2026
- 1. Kaspersky Cyberthreat Map
- Specifications
- Reason to Buy
- Features
- 2. Fortinet Threat Map
- Specifications
- Reason to Buy
- Features
- 3. Check Point ThreatCloud Map
- Specifications
- Reason to Buy
- Features
- 4. Norse Attack Map
- Specifications
- Reason to Buy
- Features
- 5. Imperva Live Threat Map
- Specifications
- Reason to Buy
- Features
- 6. SonicWall Live Cyber Attack Map
- Specifications
- Reason to Buy
- Features
- 7. Bitdefender Threat Map
- Specifications
- Reason to Buy
- Features
- 8. Digital Attack Map
- Specifications
- Reason to Buy
- Features
- 9. Akamai Real-Time Web Attack Monitor
- Specifications
- Reason to Buy
- Features
- 10. FireEye Threat Map
- Specifications
- Reason to Buy
- Features
- Conclusion
If you want to see what I mean, just take a peek at some of the live threat maps online. FireEye’s Cyber Map or Bitdefender’s Threat Map can be pretty eye-opening. You can also get a great visual of DDoS attacks specifically over at Digital Attack Map. Companies like Akamai, SonicWall, and Imperva are constantly working to protect us against these threats, but it’s a never-ending battle.
Real-time visibility into these threats is essential for proactive defense, strategic planning, and rapid incident response.
Cyber attack maps have become indispensable tools for cybersecurity professionals and organizations.
These interactive platforms provide live visualizations of global cyber threats, helping users monitor attack patterns, assess risks, and stay ahead of emerging dangers.
Whether you’re a security analyst, IT manager, or simply interested in cyber trends, understanding the best cyber attack maps can empower your digital defense strategy.
This comprehensive guide reviews the Top 10 Cyber Attack Maps to See Digital Threats in 2026, comparing their features, specifications, and unique advantages.
We’ll help you discover which map best fits your needs, with clear reasons to buy, detailed features, and direct links to try each tool.
Comparison Table: Top 10 Cyber Attack Maps 2026
| Tool Name | Real-Time Data | Attack Types | Customization | Free Access |
|---|---|---|---|---|
| Kaspersky Cyberthreat Map | Yes | Multiple | Yes | Yes |
| Fortinet Threat Map | Yes | Multiple | Yes | Yes |
| Check Point ThreatCloud Map | Yes | Multiple | Yes | Yes |
| Norse Attack Map | Yes | Multiple | No | Yes |
| Imperva Live Threat Map | Yes | Multiple | No | Yes |
| SonicWall Live Cyber Attack Map | Yes | Web Attacks | Limited | Yes |
| Bitdefender Threat Map | Yes | DDoS | Yes | Yes |
| Digital Attack Map | Yes | Multiple | No | Yes |
| Akamai Real-Time Web Attack Monitor | Yes | Multiple | Yes | Yes |
| FireEye Threat Map | Yes | Multiple | No | Yes |
1. Kaspersky Cyberthreat Map
Kaspersky’s Cyberthreat Map is a visually stunning platform that displays real-time cyber threats from around the world.
The map aggregates data from multiple sources, including on-access and on-demand scans, mail and web anti-virus, intrusion detection, and botnet activity.
Users can rotate and zoom on specific countries to view nation-specific data and historical trends.
Kaspersky’s interface is sleek, interactive, and informative, making it a favorite among security professionals and enthusiasts alike.
The map not only reveals ongoing attacks but also provides insights into the most infected countries and prevalent threat types.
Its rich data sources and intuitive controls make it an excellent choice for monitoring the global threat landscape or drilling down into local risks.
Specifications
- Real-time visualization of global cyber threats
- Multiple data sources (scans, botnet, anti-virus, etc.)
- Country-specific details and statistics
- Interactive globe view with zoom and rotation
- Historical data and trends
Reason to Buy
- Comprehensive real-time threat monitoring
- User-friendly and visually engaging interface
- Detailed breakdown by country and threat type
- Trusted by cybersecurity professionals worldwide
Features
- Multiple display modes and nation panels
- Top threat types and infected regions
- Customizable views for deeper insights
- Option to embed the map on your website
✅ Best For: Real-time global threat awareness and detailed regional analysis
🔗 Try Kaspersky Cyberthreat Map here → Kaspersky Official Website2. Fortinet Threat Map
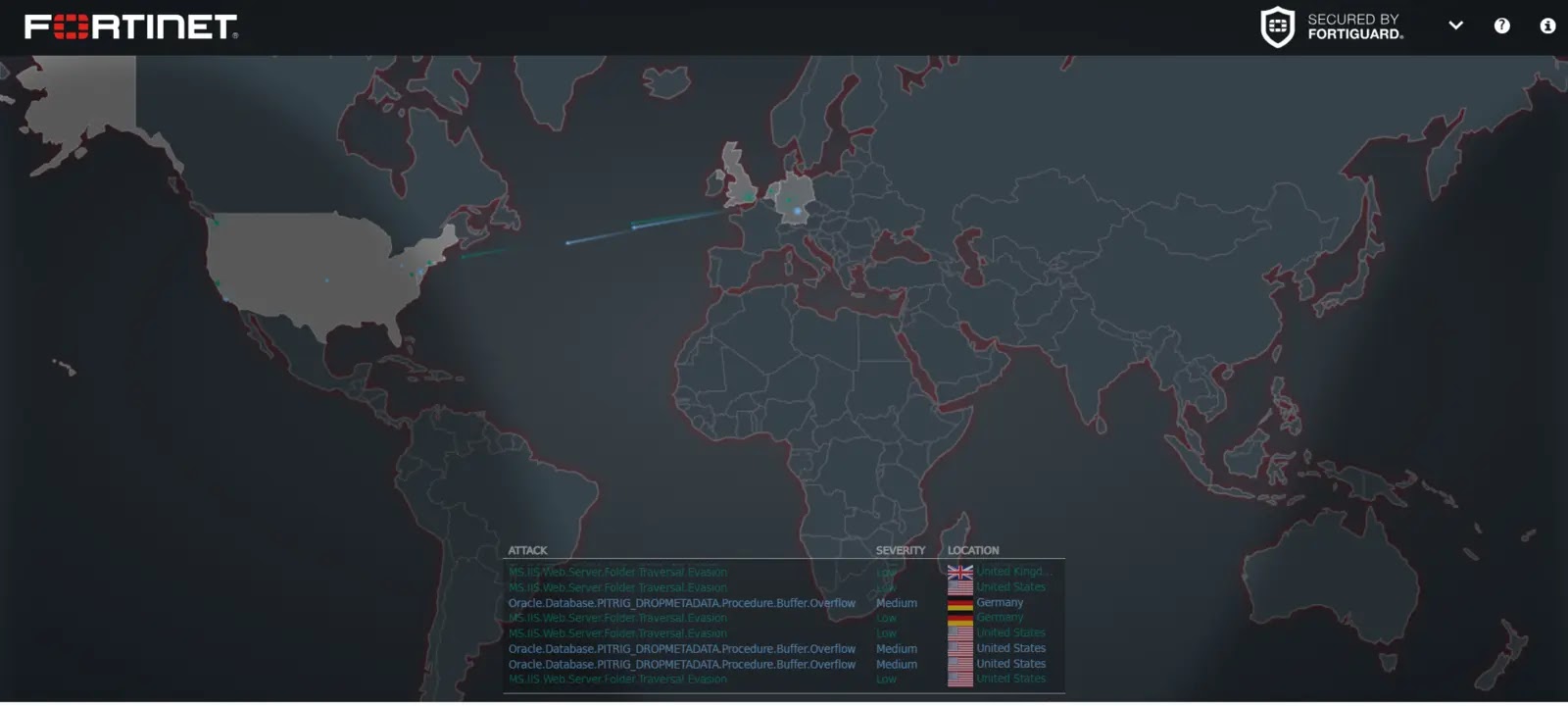
Fortinet’s Threat Map delivers a real-time view of malicious network activity across the globe.
Leveraging data from Fortinet’s extensive network of security appliances, the map displays attack types, severity, and geographic locations.
Users can click on any country to see detailed statistics for incoming and outgoing attacks, providing a granular perspective on the threat environment.
The platform’s clean interface and ongoing statistics, such as botnet C&C attempts and malware programs per minute, make it a valuable resource for organizations seeking actionable intelligence on current threats.
Specifications
- Live visualization of attack types and locations
- Real-time statistics and activity logs
- Country-level breakdowns
- Integration with Fortinet’s security ecosystem
Reason to Buy
- High-fidelity, real-time threat intelligence
- Deep integration with Fortinet solutions
- Country-specific analytics for targeted defense
- Continuous updates from a global sensor network
Features
- Detailed logs of attack types and severity
- Customizable threat monitoring
- Day/night map overlay
- Ongoing botnet and malware statistics
✅ Best For: Organizations using Fortinet products or seeking granular attack analytics
🔗 Try Fortinet Threat Map here → Fortinet Official Website3. Check Point ThreatCloud Map
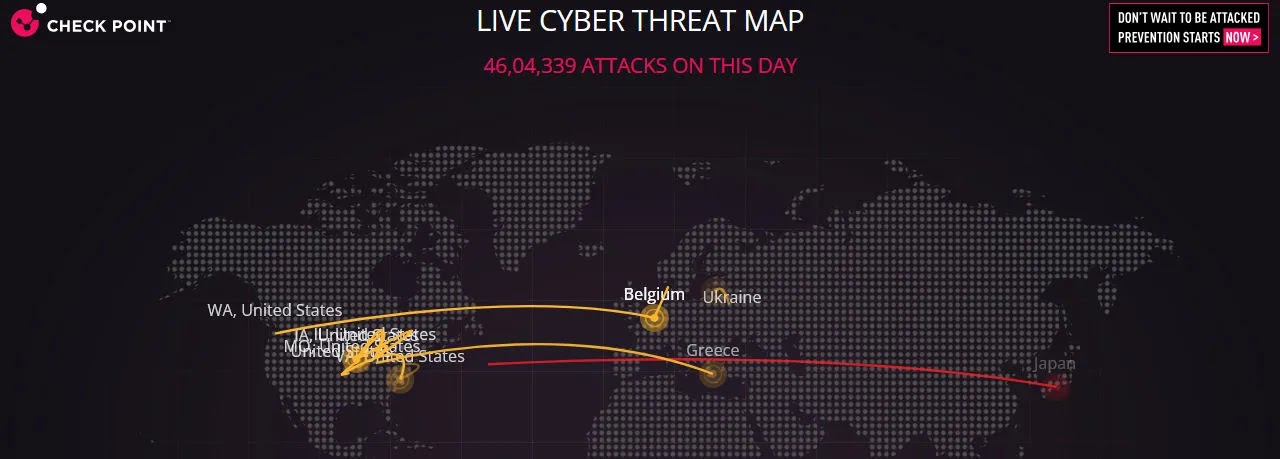
Check Point’s ThreatCloud Map offers a daily-updated, real-time visualization of global cyber attacks.
The platform presents a clear chart of recent attacks, top targeted countries, and industries, along with the most-used malware types.
Its historical playback feature allows users to review past attack data for deeper analysis.
The map’s straightforward visuals and regularly refreshed data make it ideal for both quick overviews and in-depth threat investigations.
Specifications
- Real-time and historical attack data
- Daily updates and playback feature
- Global and regional attack statistics
- Malware type breakdowns
Reason to Buy
- Trusted, up-to-date threat intelligence
- Historical data for trend analysis
- Simple, clean interface for rapid insights
- Focus on top targeted sectors and regions
Features
- Attack playback and daily charts
- Customizable filters for attack types
- Malware and target country statistics
- Easy-to-understand data visualizations
✅ Best For: Security teams needing daily threat updates and historical analysis
🔗 Try Check Point ThreatCloud Map here → Check Point Official Website4. Norse Attack Map

The Norse Attack Map is renowned for its mesmerizing real-time visualizations of cyber attacks.
This map detects your location and displays live stats for your country, including top local attacks and infection types.
The platform’s graphical interface is sleek and engaging, offering a dramatic view of ongoing cyber battles worldwide.
Although not the most feature-rich, Norse’s map is highly effective for raising awareness and illustrating the scale of global cyber threats.
Specifications
- Real-time attack visualization
- Geolocation of sources and targets
- Attack types and targeted services
- Sleek, interactive interface
Reason to Buy
- Eye-catching, live cyber attack displays
- Immediate awareness of global threats
- Simple, intuitive user experience
- Free and accessible to all users
Features
- Country-specific stats and trends
- Toggle map color and globe view
- Demo mode for presentations
- Helpful articles and buzz tap
✅ Best For: Visualizing attack patterns and public cybersecurity awareness
🔗 Try Norse Attack Map here → Norse Official Website5. Imperva Live Threat Map

Imperva’s Live Threat Map provides a real-time global view of DDoS attacks, hacking attempts, and bot assaults.
The map is powered by Imperva’s security services, offering instant visibility into ongoing threats and their geographic spread.
Its clean interface and focus on actionable intelligence make it a practical tool for both security professionals and the general public.
Imperva’s map is especially useful for organizations concerned with DDoS and botnet activity.
Specifications
- Real-time global attack visualization
- DDoS, hacking, and botnet coverage
- Data sourced from Imperva’s security services
- Simple, intuitive interface
Reason to Buy
- Real-time, actionable threat intelligence
- Focus on DDoS and bot attacks
- Trusted by enterprises worldwide
- Free and open access
Features
- Global attack mapping
- Multiple threat categories
- Instant updates
- Easy-to-understand visuals
Best For: DDoS and botnet threat monitoring
Try Imperva Live Threat Map here → Imperva Official Website6. SonicWall Live Cyber Attack Map
SonicWall’s Live Cyber Attack Map offers a graphical view of attacks over the past 24 hours, including malware, ransomware, encrypted traffic, intrusion attempts, and spam/phishing.
The map highlights both the origin and target of each attack, providing actionable intelligence for security teams.
SonicWall’s platform is particularly valuable for organizations seeking to monitor a wide range of threat types in real time.
Specifications
- 24-hour attack visualization
- Multiple attack categories
- Source and target mapping
- Security news and research integration
Reason to Buy
- Broad threat coverage (malware, ransomware, etc.)
- Real-time and historical insights
- Integration with SonicWall research
- Easy-to-use graphical interface
Features
- Attack site statistics
- Security news updates
- Multiple threat categories
- Interactive global map
Best For: Comprehensive, multi-threat monitoring
Try SonicWall Live Cyber Attack Map here → SonicWall Official Website7. Bitdefender Threat Map
Bitdefender’s Threat Map is an interactive platform that displays live attacks, infections, and spam worldwide.
The map provides real-time reports with details on attack type, time, and location, helping users identify emerging threats quickly.
Its clear visuals and up-to-date information make it a strong choice for anyone seeking a comprehensive view of global cyber risks.
Bitdefender’s focus on infections and spam adds an extra layer of intelligence for organizations facing diverse threat vectors.
Specifications
- Live attack, infection, and spam data
- Real-time reporting by type and location
- Interactive, user-friendly interface
- Global coverage
Reason to Buy
- Comprehensive threat intelligence
- Focus on infections and spam trends
- Real-time updates for rapid response
- Backed by Bitdefender’s research
Features
- Attack and infection breakdowns
- Global and regional views
- Spam and malware tracking
- Simple, interactive controls
Best For: Organizations monitoring infections, spam, and malware
Try Bitdefender Threat Map here → Bitdefender Official Website8. Digital Attack Map
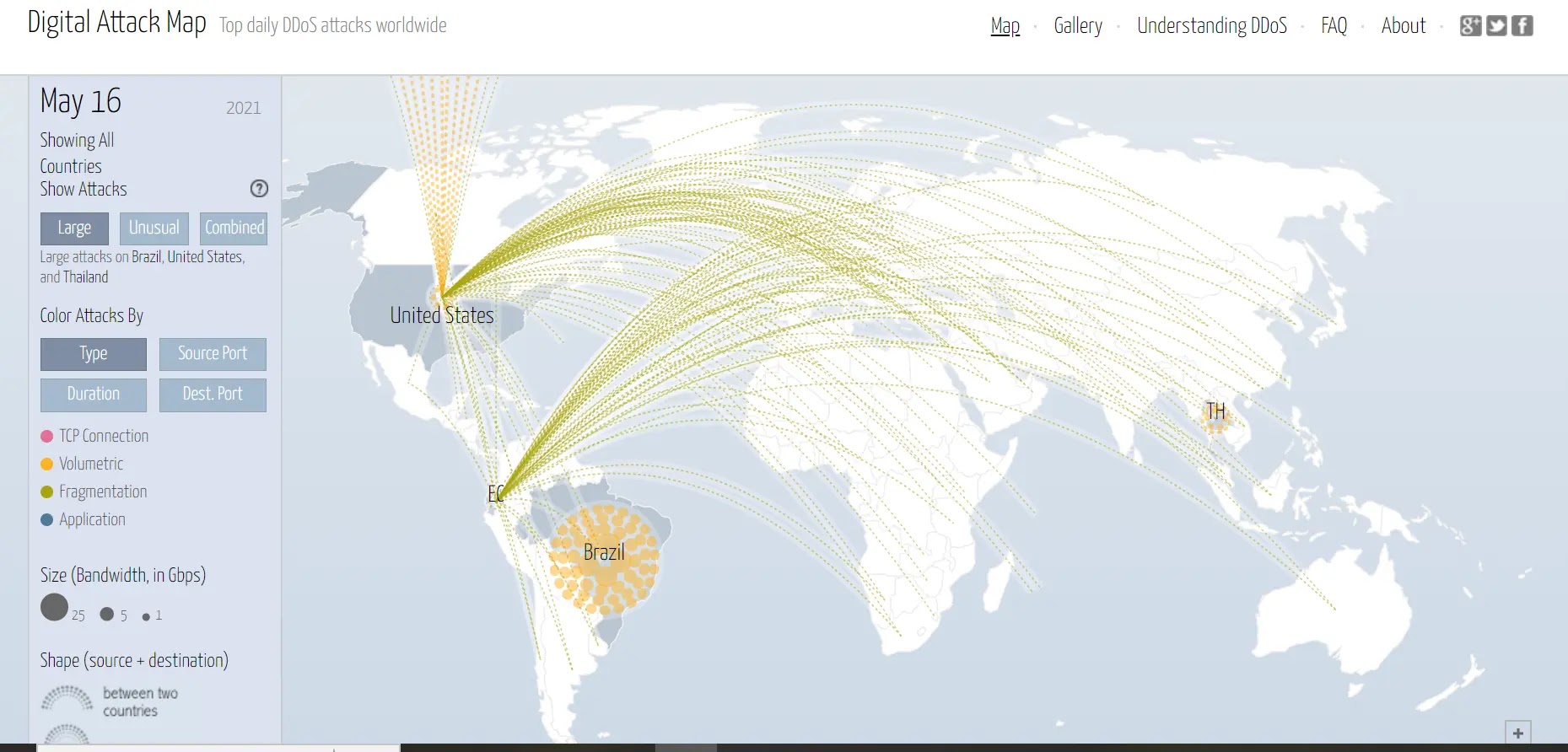
The Digital Attack Map, created in collaboration with Arbor Networks and Google, specializes in visualizing global DDoS attacks.
The platform offers real-time data on attack intensity and frequency, with options to view historical trends and filter by size or type.
The map’s intuitive interface and focus on DDoS make it a go-to tool for organizations needing to track large-scale disruptions.
Although the tool’s maintenance status should be checked for 2025, it remains a valuable resource for DDoS situational awareness.
Specifications
- Real-time DDoS attack visualization
- Attack traffic intensity and location
- Historical data and filtering options
- Collaboration with Arbor Networks and Google
Reason to Buy
- Focused insight into DDoS activity
- Historical trends for incident analysis
- Easy-to-use, interactive interface
- Recognized by industry leaders
Features
- Real-time and historical filtering
- Attack size and type customization
- Global and regional monitoring
- Intuitive data visualizations
Best For: DDoS threat monitoring and historical analysis
Try Digital Attack Map here → Digital Attack Map Official Website9. Akamai Real-Time Web Attack Monitor
Akamai’s Real-Time Web Attack Monitor leverages its massive global network to visualize web-based attacks as they happen.
The map pinpoints sources and targets, displaying the most significant attack locations over the past 24 hours.
Users can choose different regions and languages, making it accessible to a global audience.
Akamai’s map is ideal for organizations concerned with web application security and large-scale DDoS attacks.
Specifications
- Real-time web attack visualization
- Global and regional filtering
- Multi-language support
- Data from Akamai’s CDN and security services
Reason to Buy
- Extensive global attack coverage
- Focus on web and DDoS threats
- Regional and language customization
- Backed by Akamai’s industry-leading infrastructure
Features
- Top attack locations and trends
- Adjustable dashboards and notifications
- Learning resources and glossary
- 24-hour attack history
Best For: Monitoring web-based attacks and DDoS trends
Try Akamai Real-Time Web Attack Monitor here → Akamai Official Website10. FireEye Threat Map
FireEye’s Threat Map provides a real-time summary of cyber attacks detected by its global network. The platform highlights the total number of daily attacks, top targeted industries, and leading attacker countries.
While it offers less granular detail than some competitors, FireEye’s map excels in presenting a quick, easy-to-read overview of the current threat landscape.
This tool is particularly useful for identifying advanced persistent threats and monitoring global attack campaigns.
Specifications
- Real-time attack summaries
- Daily attack totals and trends
- Industry and country breakdowns
- Data sourced from FireEye’s global network
Reason to Buy
- Fast, accessible threat overview
- Focus on advanced persistent threats
- Industry-specific attack insights
- Backed by FireEye’s threat intelligence
Features
- Top attacker and target statistics
- Simple, user-friendly interface
- Daily updated data
- Overview of global attack campaigns
✅ Best For: Quick threat overviews and industry-specific monitoring
🔗 Try FireEye Threat Map here → FireEye Official WebsiteConclusion
Cyber attack maps are now essential tools in the fight against digital threats.
In 2026, with cyber risks evolving at breakneck speed, these platforms empower organizations and individuals to visualize, understand, and respond to global and local threats in real time.
Whether you need granular analytics, historical playback, or simply a live snapshot of the world’s digital battles, there’s a cyber attack map tailored to your needs.
By leveraging the top 10 cyber attack maps reviewed here, you gain a strategic edge in threat detection, risk assessment, and incident response.
Stay informed, stay vigilant, and let these powerful visualization tools guide your cybersecurity journey in the ever-changing digital landscape.









No Comment! Be the first one.