Threat Actors Use Google Ads for Malicious Mac Cleaner Scams
Cybercriminals are exploiting Google Search Ads to lure Mac users to deceptive websites. These sites falsely claim to offer computer cleaning services. These sponsored ads appear when users search...
Cybercriminals are exploiting Google Search Ads to lure Mac users to deceptive websites. These sites falsely claim to offer computer cleaning services.
These sponsored ads appear when users search for common terms like “mac cleaner” or “clear cache macos,” making them look legitimate at first glance.
The landing pages are designed to resemble Apple’s official website, complete with familiar layouts and navigation menus. However, beneath this professional appearance lies a dangerous scheme that targets unsuspecting Mac owners.
The attackers have set up fake posts on platforms like Medium and Google’s own services to distribute malicious instructions that can give hackers full control of a victim’s computer.
The attack campaign exploits a simple but effective tactic: users trust Google’s advertising system and recognize Apple’s design language.
When they click on these ads, they get redirected to pages filled with technical-sounding instructions about freeing up disk space or installing system updates.
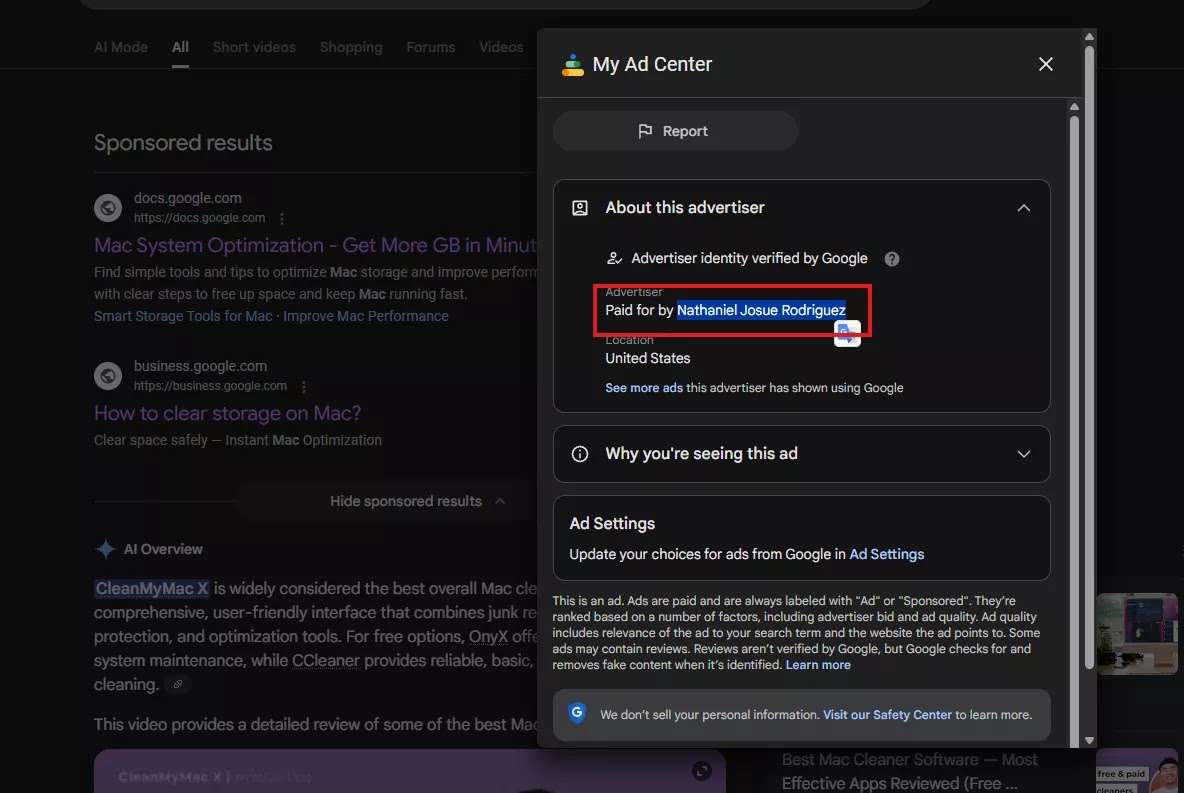
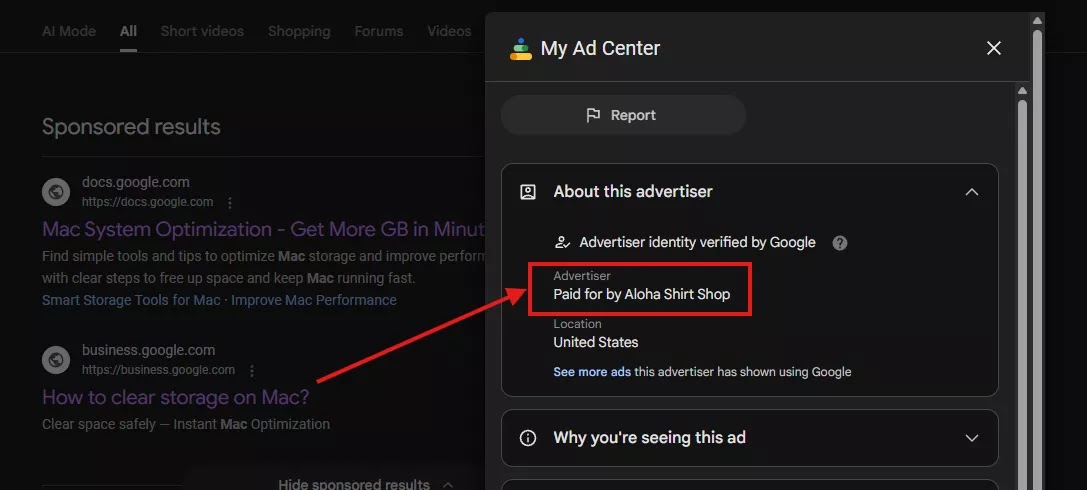
MacKeeper analysts identified that the threat actors are using hijacked Google Ads accounts to run this operation, suggesting they may have compromised legitimate advertiser profiles belonging to users like Nathaniel Josue Rodriguez and companies such as Aloha Shirt Shop.
How the Malware Infection Works
The core of this attack relies on a deceptively simple but powerful command disguised as legitimate system maintenance.
When users copy and paste the provided instructions into their Terminal application, they unknowingly trigger a remote code execution attack.
The command chain starts with an innocent-looking instruction that reads “Cleaning macOS Storage” or “Installing packages please wait,” which are merely social engineering tactics designed to make users feel confident they are performing normal maintenance.
Beneath these friendly messages lies base64-encoded text that hides the real attack code.
The system decodes this hidden text using the base64 command, which transforms it into an actual shell command that downloads a malicious script from a remote server without any user knowledge or consent.
Once downloaded, this script runs with full user permissions, giving attackers the ability to install malware, steal SSH keys, create system backdoors, mine cryptocurrency, steal personal files, or modify critical system settings.
The attackers use various obfuscation techniques to hide where the commands actually connect, making detection more difficult.
This pattern of disguised downloads and automatic execution is extremely common in professional malware operations and supply chain attacks.
MacKeeper researchers successfully identified and reported these dangerous ads to Google, and the tech giant has taken action to remove them from search results.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.