Threat Actors Continuously Attacking MS-SQL Servers to Deploy ICE
The persistent threat actor Larva-26002 is actively targeting poorly managed Microsoft SQL (MS-SQL) servers. In its latest campaign, the group deploys a new scanner malware identified as ICE Cloud...
The persistent threat actor Larva-26002 is actively targeting poorly managed Microsoft SQL (MS-SQL) servers. In its latest campaign, the group deploys a new scanner malware identified as ICE Cloud Client.
The campaign has been active since at least January 2024 and continues into 2026, with the attacker upgrading their tools with every cycle. What started as a ransomware operation has now shifted toward large-scale scanning of vulnerable database infrastructure.
In January 2024, the group first made its mark by deploying Trigona and Mimic ransomware on MS-SQL servers exposed to the internet with weak credentials.
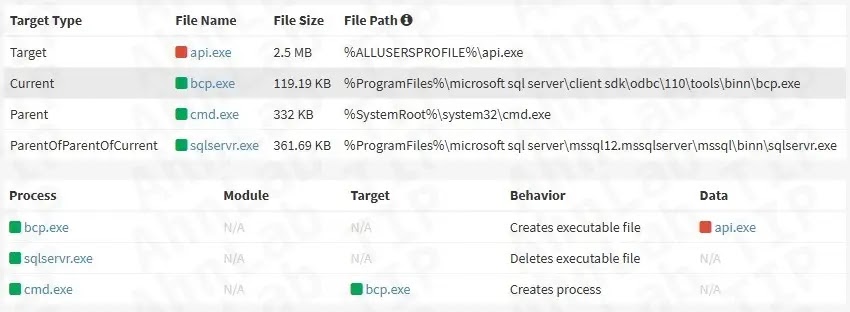
The attackers exploited the Bulk Copy Program (BCP) utility — a legitimate MS-SQL tool — to extract and drop malware directly onto compromised hosts.
Tools like AnyDesk were also installed for remote access, along with port forwarders for RDP connections. By 2025, the group had added Teramind, a remote monitoring and management (RMM) tool, and switched to a scanner written in Rust.
ASEC analysts identified a fresh wave of attacks in 2026 in which the same threat actor compromised the same MS-SQL servers that had been targeted in previous years.
This time, the attacker deployed ICE Cloud — a scanner malware written in the Go programming language — a clear departure from the Rust-based scanner used in 2025.
The binary strings embedded inside ICE Cloud are written in Turkish, a detail that directly ties this campaign to the Mimic ransomware attacks from 2024. This pattern of repeated targeting points to a deliberate, long-term strategy against unpatched database servers.
What makes this campaign particularly concerning is the shift away from ransomware toward scanning.
By building a growing pool of compromised servers that silently probe other databases for weak credentials, the threat actor appears to be laying the groundwork for something larger.
The collected data is forwarded to the attacker’s C&C server, giving the group a detailed picture of exposed database assets across the internet.
ICE Cloud Scanner: The Infection Mechanism
The attack starts when Larva-26002 identifies an MS-SQL server exposed to the internet with poor password hygiene.
After gaining access through brute force or dictionary attacks, the attacker runs system commands like hostname, whoami, and netstat -an to profile the host.
Malware is then created using the BCP utility, which exports a malicious binary from the database table uGnzBdZbsi to a local path as api.exe, guided by a formatting file named FODsOZKgAU.txt — a setup that has not changed since 2024.
In systems where BCP fails, the malware is fetched using Curl or Bitsadmin via PowerShell.
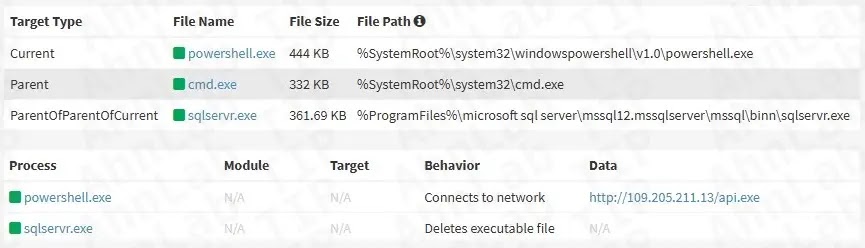
The api.exe file, labeled ICE Cloud Launcher, connects to a C&C server for authentication before downloading the core scanner — ICE Cloud Client.
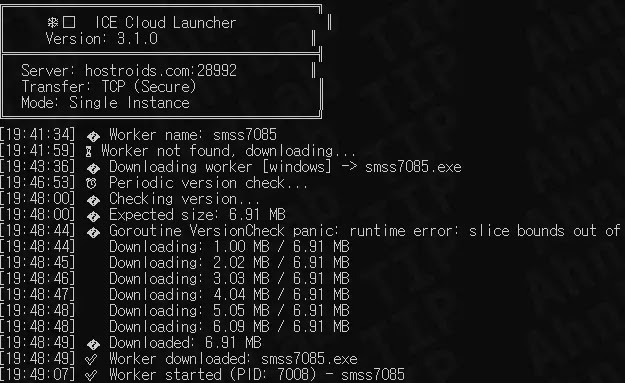
Once downloaded, ICE Cloud Client is saved under a random filename to disguise it as a legitimate program.
The malware then registers with the C&C server, which sends it a list of MS-SQL addresses to target along with a credential pair such as ecomm/ecomm and the task string TASK.
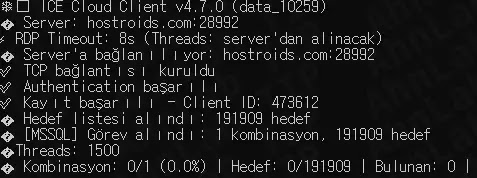
The scanner attempts to log in using those credentials and reports any successful access back to the server.
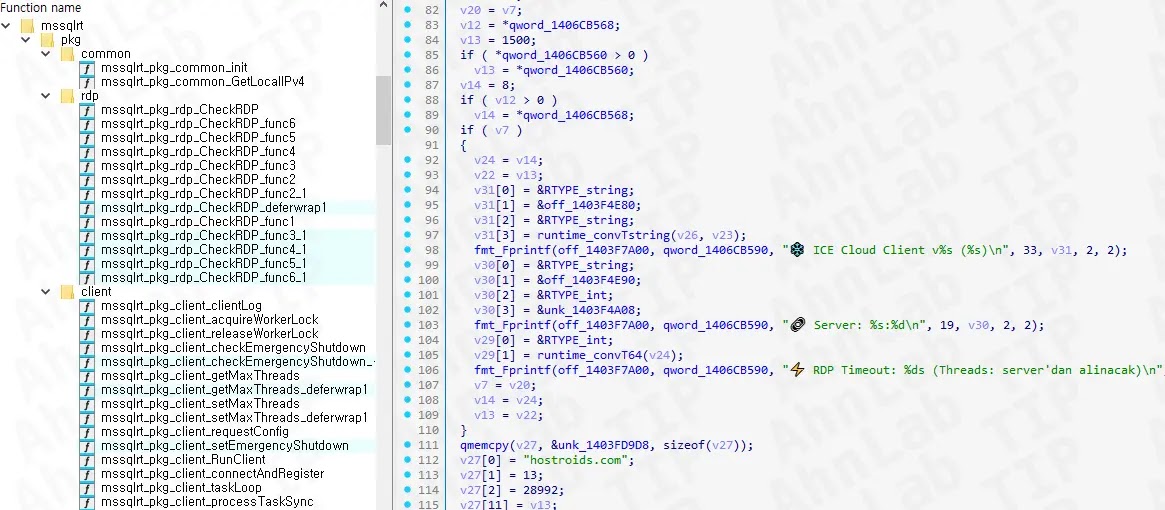
Internal binary strings are written in Turkish and include emoji characters, suggesting the developer may have relied on generative AI to write parts of the code.
Database administrators should set strong, hard-to-guess passwords for all MS-SQL accounts and update them regularly to prevent brute force access.
Any MS-SQL server facing the internet must be protected behind a firewall that only allows authorized connections.
It is also important to keep endpoint security software updated so that known malware is caught before it executes on the host.
Administrators should watch for unusual BCP activity, unexpected files like api.exe in C:ProgramData, or unrecognized outbound connections, and treat any such sign as a potential compromise requiring immediate investigation.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.