SyncFuture Campaign: Legitimate Software Deploying Malware
Threat researchers uncovered an alarming espionage operation in December 2025, specifically targeting residents of India through sophisticated phishing campaigns. The attack, dubbed SyncFuture,...
Threat researchers uncovered an alarming espionage operation in December 2025, specifically targeting residents of India through sophisticated phishing campaigns.
The attack, dubbed SyncFuture, demonstrates how cybercriminals can abuse legitimate business software as a vehicle for launching advanced malware attacks.
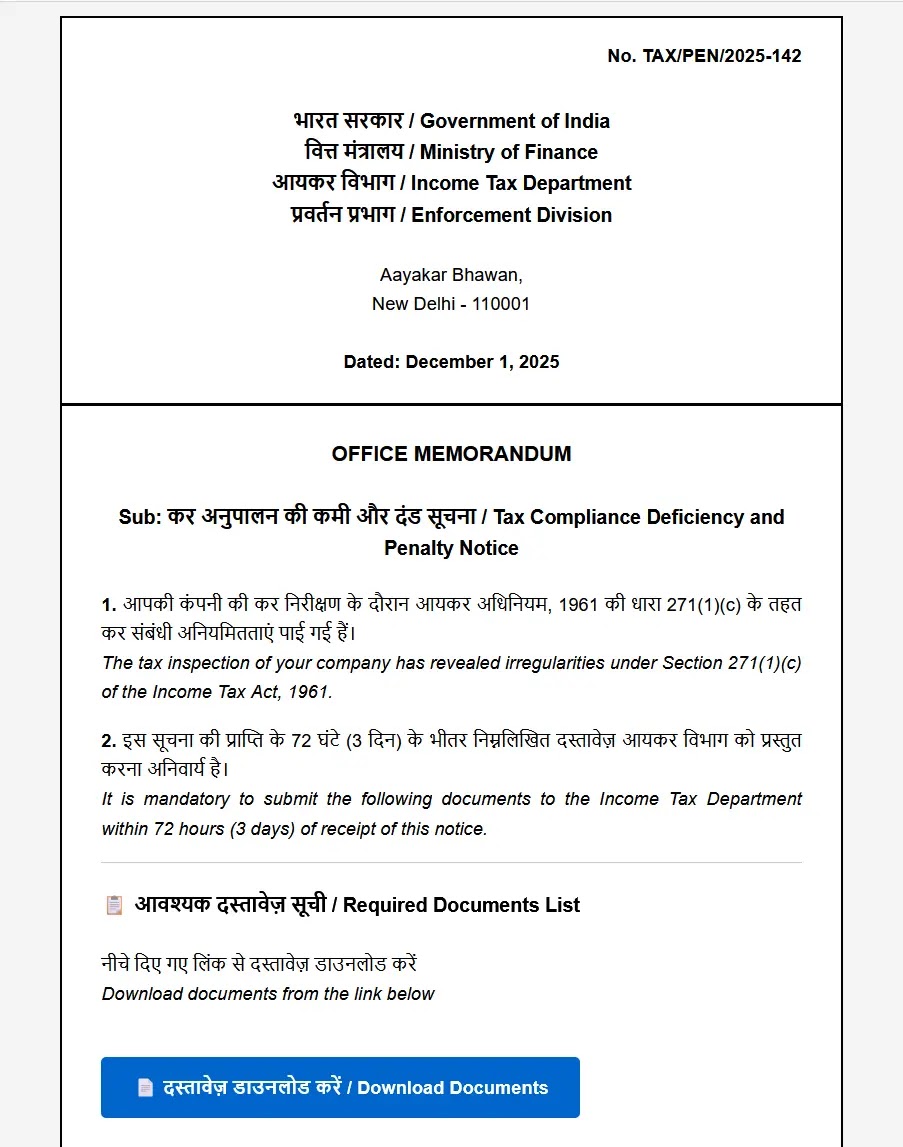
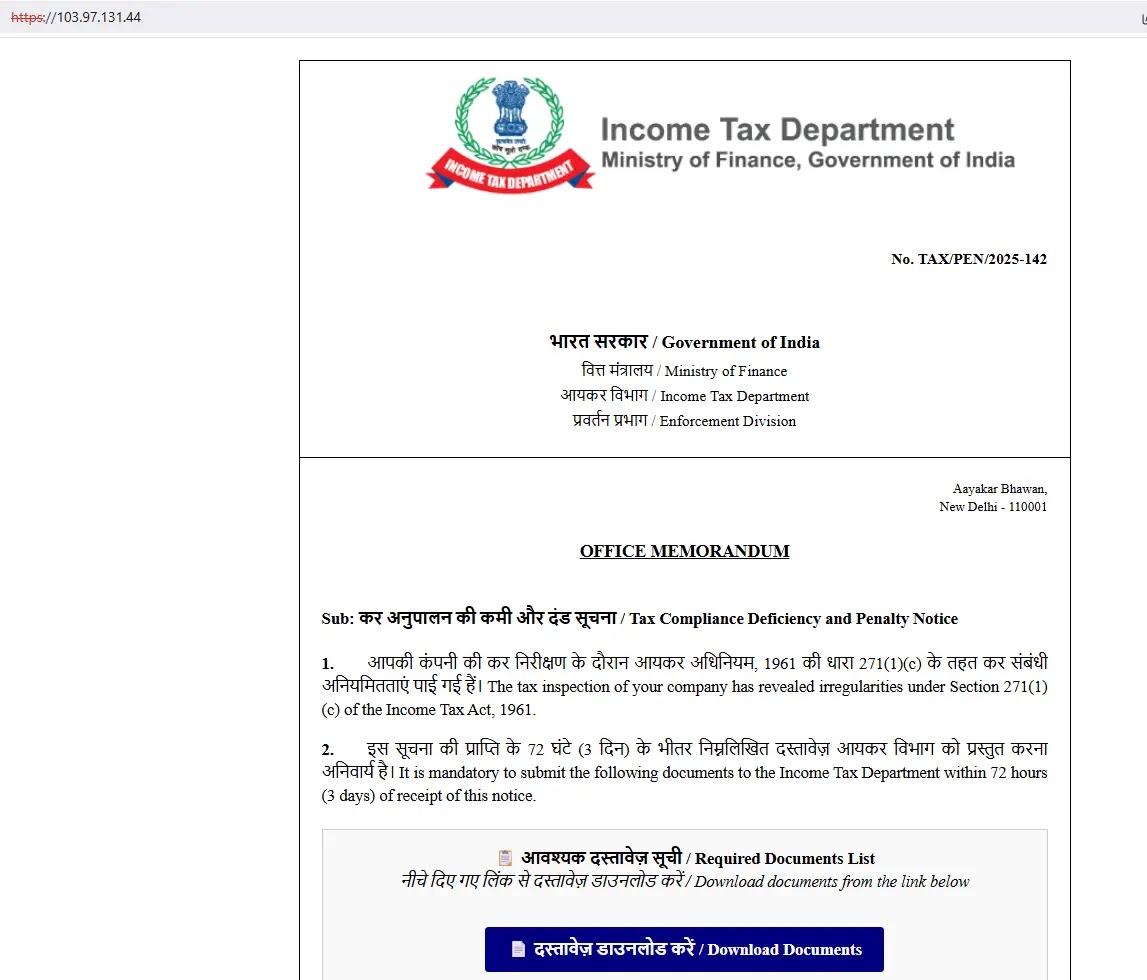
Attackers sent fraudulent emails impersonating India’s Income Tax Department, tricking victims into downloading malicious files containing multiple stages of malicious code.
The infection chain reveals remarkable technical sophistication. Victims who opened the files received a ZIP archive containing what appeared to be a government document review tool.
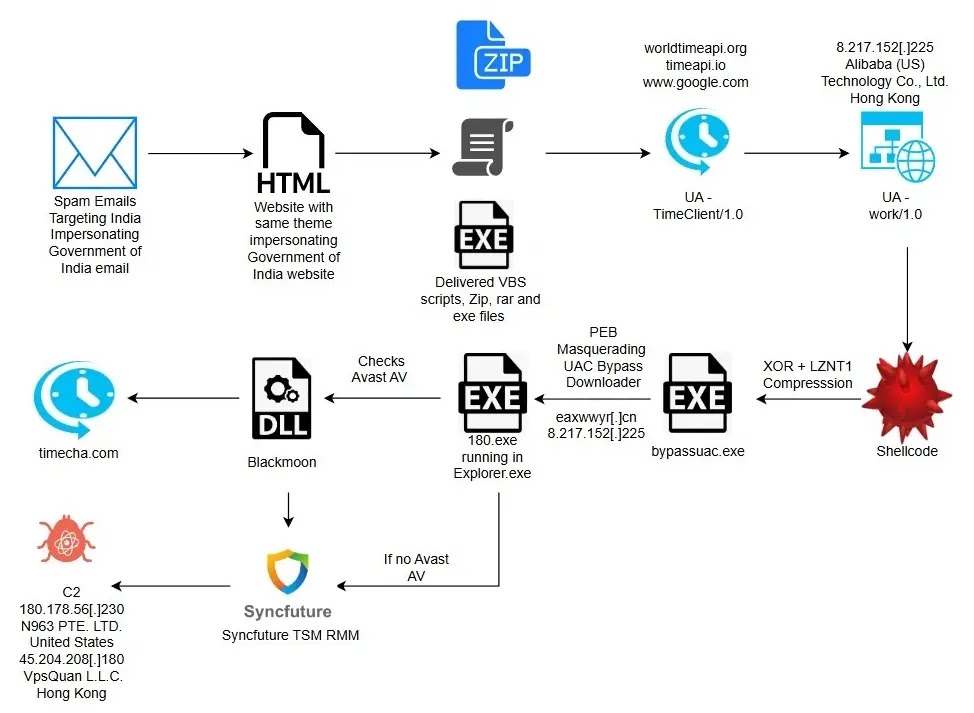
Instead, the archive held a weaponized executable that would begin a multi-stage attack sequence designed to gain complete control over infected computers and maintain long-term access.
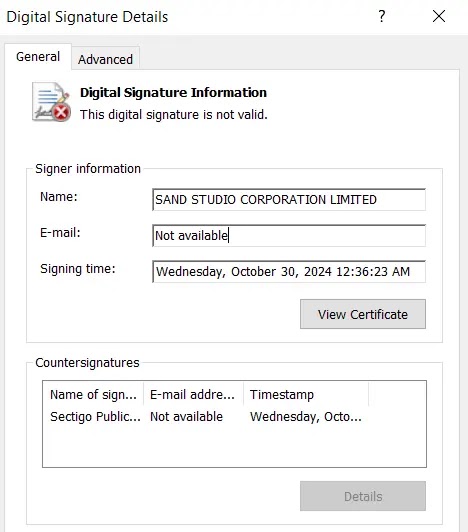
eSentire analysts and researchers identified this campaign and documented how it combines multiple attack techniques to evade security defenses and establish persistent access.
The threat actors employed legitimate Microsoft-signed binaries, automated evasion tactics, and ultimately repurposed a genuine enterprise management platform as their final payload—a particularly troubling indicator of the campaign’s sophistication and resources.
Avast Antivirus Evasion Through Automated Mouse Simulation
The SyncFuture campaign demonstrates advanced detection evasion tactics, particularly targeting Avast Free Antivirus through a technique most wouldn’t expect from automated malware.
When the malware detected Avast running on a victim’s machine, it deployed an innovative approach: simulating mouse movements and clicks to navigate Avast’s interface automatically.
This technique is noteworthy because it shows attackers studying specific antivirus products in detail.
The malware would locate the Avast detection dialog window, then programmatically move the cursor to hardcoded screen coordinates and click on options that create security exceptions.
By simulating human-like user actions rather than attempting to disable the antivirus entirely, the malware successfully added itself to Avast’s exclusion list, effectively whitelisting the malicious files.
This persistence mechanism allowed the threat actor’s tools to operate undetected by the antivirus software.
The batch scripts analyzed contained conditional logic specifically checking whether Avast was running, demonstrating that attackers had thoroughly tested and customized their malware for different antivirus environments.
This infection mechanism represents a significant evolution in malware sophistication—moving beyond simple evasion toward targeted manipulation of specific security products to achieve their long-term espionage objectives.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.