STX RAT Evades Detection with Hidden Remote Uses Desktop
A new remote access trojan, dubbed STX RAT, has emerged as a serious cybersecurity threat for 2026. This malware employs a combination of hidden remote desktop access and credential-stealing...
A new remote access trojan, dubbed STX RAT, has emerged as a serious cybersecurity threat for 2026. This malware employs a combination of hidden remote desktop access and credential-stealing features, allowing it to silently compromise targeted machines.
The malware gets its name from the Start of Text (STX) magic byte x02 that it prepends to every message sent to its command-and-control (C2) server—a subtle marker of the precision behind its design.
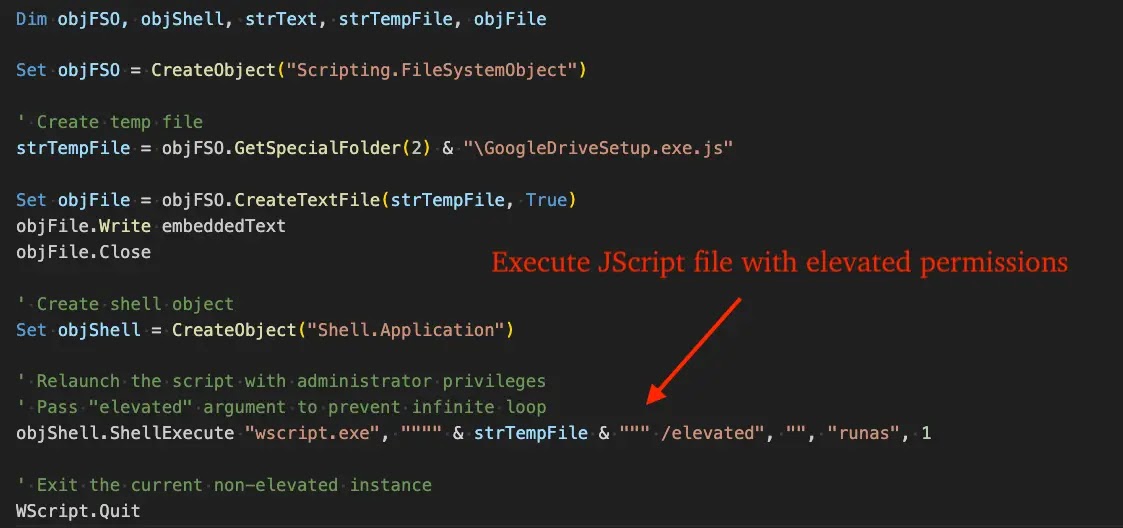
The malware was first observed in late February 2026, when attackers attempted delivery inside a financial sector organization through a browser-downloaded VBScript file.
That script dropped a JScript file, which fetched a TAR archive and passed execution to a PowerShell loader that injected the final payload into memory.
By early March, Malwarebytes reported a separate campaign spreading STX RAT through trojanized FileZilla installers, confirming the operators were already running multiple delivery methods simultaneously.
eSentire’s Threat Response Unit (TRU) researchers identified and analyzed the malware following the late-February incident, tracking it as STX RAT.
Their investigation revealed a technically sophisticated implant with extensive anti-analysis defenses, including artifact checks for VirtualBox, VMware, and QEMU environments.
When such artifacts are detected, the malware performs a “jitter exit”—pausing for a random delay before terminating—making it harder to study in automated sandbox environments.
Beyond VM detection, STX RAT uses an AMSI-ghosting technique that patches a core Windows RPC function, disabling a layer security tools rely on to scan running processes. It hides its terminal window from the Alt+Tab switcher and Taskbar.
Once active, the implant contacts a C2 at 95.216.51.236 and sends an introduction message containing the hostname, username, OS version, admin status, installed RAM, and a list of detected antivirus products.
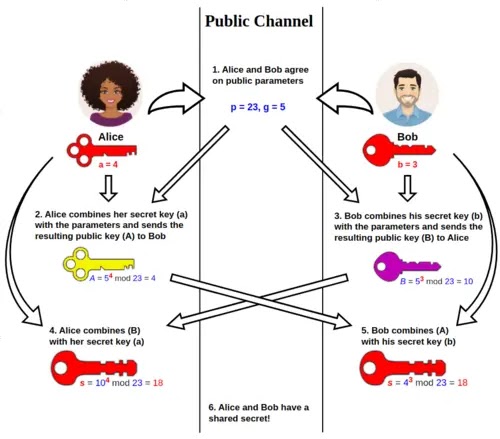
All C2 traffic is secured through an ECDH key exchange using X25519 and ChaCha20-Poly1305 authenticated encryption, making decryption without the session keys highly unlikely.
The infostealer module targets saved credentials from FileZilla, WinSCP, and Cyberduck—applications widely used by developers and IT administrators—and takes a desktop screenshot before transmitting stolen data, giving attackers a direct visual of the compromised machine.
Hidden Remote Desktop Control: How STX RAT Takes Over Silently
The most dangerous feature in STX RAT’s toolkit is its Hidden Virtual Network Computing (HVNC) module, which gives threat actors full interactive control of a victim’s machine without the victim ever noticing.
Unlike conventional remote desktop software that visibly takes over a user’s display, HVNC creates a completely separate desktop session running in the background.
All attacker activity—browsing websites, opening files, launching applications—happens inside this invisible layer, entirely unseen by the victim.
STX RAT initiates HVNC through a start_hvnc command sent by the C2. Once active, attackers can inject keystrokes via key_press, simulate mouse movements with mouse_input, scroll applications using mouse_wheel, and paste content directly with the paste command—all relying on Windows’ SendInput API.
A switch_desktop command lets operators manage multiple hidden desktop sessions at the same time, and when done, connection_lost and channel_closed commands quietly close sessions and clean up desktop handles without leaving traces.
This architecture makes STX RAT far more capable than a typical credential stealer. While the victim continues working normally on their visible screen, an attacker can simultaneously log into internal platforms, browse sensitive files, or stage additional payloads inside the hidden session.
Paired with the credential-harvesting module, HVNC turns an initial breach into an ongoing foothold that is both difficult to detect and hard to fully remove.
Security teams should immediately block the known C2 IP 95.216.51.236 and the associated Tor onion address at the network perimeter.
Deploying YARA detection rules from eSentire’s TRU—covering both the unpacked payload and loader—is recommended for identifying infections in memory.
Monitoring for elevated WScript executions involving JScript files in Temp directories and suspicious PowerShell STDIN executions can help catch early infections.
Where VBScript and JScript are not operationally necessary, disabling them outright can meaningfully shrink the initial attack surface.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.