SLOTAGENT Malware Evades Reverse Engineering with Uses Hashing
SLOTAGENT, a newly identified malware, is drawing significant attention across the cybersecurity community. Its formidable anti-analysis and evasion capabilities set it apart. Crucially, it does not...
SLOTAGENT, a newly identified malware, is drawing significant attention across the cybersecurity community. Its formidable anti-analysis and evasion capabilities set it apart. Crucially, it does not rely on brute force tactics.
Instead, it uses two precise techniques, API hashing and encrypted strings, to make reverse engineering extremely difficult for researchers.
This level of technical sophistication signals that the developers behind SLOTAGENT have put significant effort into building a tool that can stay hidden and keep working without being easily studied or stopped.
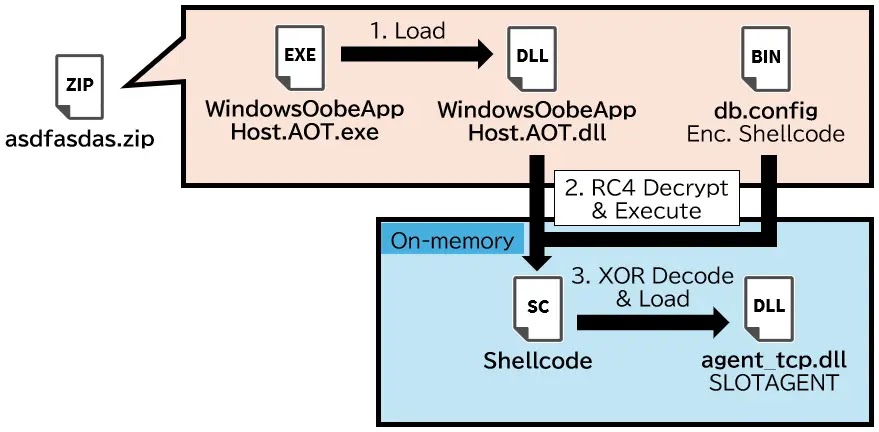
SLOTAGENT spreads primarily through phishing emails carrying malicious attachments, often disguised as routine business documents or software update files.
Once a target opens the attachment, the malware runs quietly in the background, with no immediate signs that anything has gone wrong.
It quickly contacts a remote command-and-control server to receive further instructions. This early phase is handled carefully, keeping network activity minimal to avoid triggering alerts in endpoint security systems.
The choice of phishing as the entry method reflects how social engineering remains one of the most effective ways for attackers to gain initial access.
IIJ-SECT analysts identified SLOTAGENT during a detailed investigation into suspicious network traffic linked to a targeted intrusion attempt.
Upon reviewing the malware sample, the researchers found that the code was carefully structured to obstruct both static and dynamic analysis.
Strings that would normally reveal key details about the malware’s behavior were encrypted and hidden from basic scanning tools.
In addition, the malware did not display its API dependencies in the standard import table. Those functions were instead resolved at runtime through a custom hashing process, which added a significant barrier for any analyst attempting to study the sample.
The consequences of a SLOTAGENT infection go well beyond the headaches it causes for security analysts. Organizations targeted by this malware face real and immediate risks, including data theft, unauthorized access to internal systems, and the potential loading of secondary payloads that can cause further harm.
Since the malware is built to stay invisible, infections may go undetected for weeks or even months. This extended dwell time gives attackers broad access to sensitive data and internal resources, deepening the damage with every passing day.
API Hashing and Encrypted Strings: The Core Evasion Engine
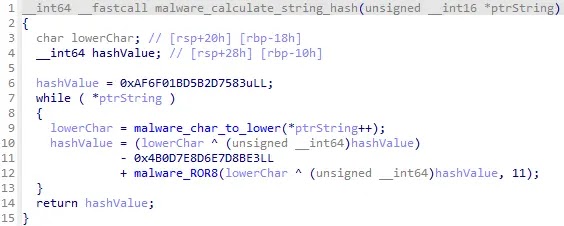
The most technically notable feature of SLOTAGENT is its runtime API resolution through hashing. When standard malware runs, it typically lists the Windows API functions it needs in an import table that analysts can read directly.
SLOTAGENT takes a different approach by calculating a hash value for each required function name and scanning loaded system modules until it finds a match. Because no function names appear in the import table, most static analysis tools fail to reveal what the malware is doing.
Researchers must identify and reverse the hashing algorithm before any meaningful analysis can begin, which significantly slows an investigation.
Encrypted strings serve as the second major defense layer within SLOTAGENT. Key data such as server addresses, registry paths, and configuration values are not stored in plain text inside the binary.
They sit in encrypted form and are only decoded in memory at the exact moment the malware needs them. This approach defeats string extraction tools used during static analysis, since those tools return nothing useful.
Even dynamic analysis can fall short if memory is captured at the wrong point in the execution timeline, leaving analysts with incomplete visibility into what the malware is doing.
Security teams should implement behavioral detection rules focused on spotting runtime API resolution activity, rather than depending solely on signature-based methods. Monitoring for unusual memory allocation and unexpected process injection can help flag SLOTAGENT infections early.
Network defenders should watch outbound traffic for patterns consistent with command-and-control communication, particularly from processes that do not normally initiate external connections.
Keeping endpoint tools updated and ensuring threat intelligence feeds remain current are both important steps. Finally, training staff to recognize phishing emails directly addresses the delivery method SLOTAGENT relies on for its initial access.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.