Shadow DNS Hacking Routers Internet Traffic Through Compromised
Users generally trust their routers to direct internet traffic accurately. However, few consider that these critical “signposts” of the web are themselves vulnerable to manipulation. A...
Users generally trust their routers to direct internet traffic accurately. However, few consider that these critical “signposts” of the web are themselves vulnerable to manipulation.
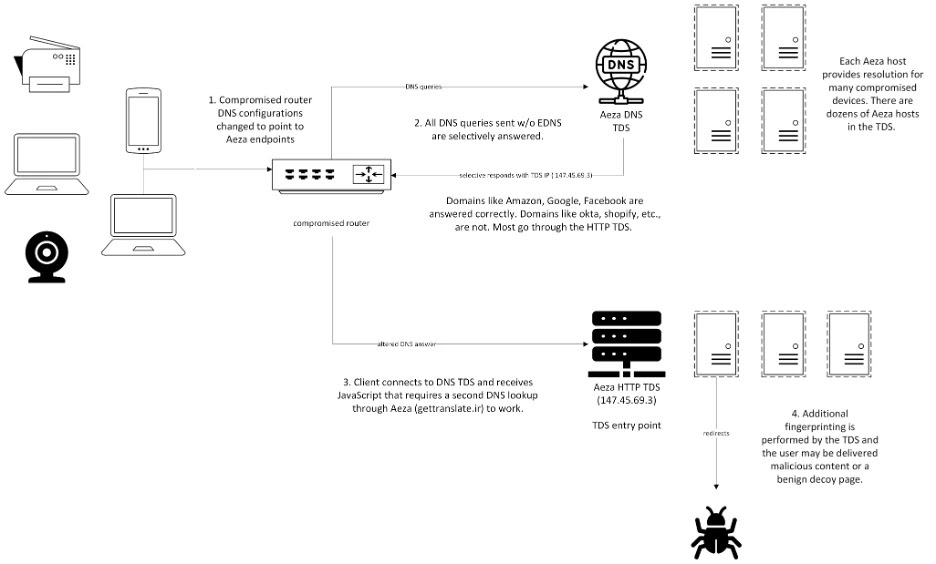
A sophisticated “shadow” network has been silently hijacking home internet connections by compromising vulnerable routers and altering their DNS configurations.
Instead of using a legitimate Service Provider’s servers, these infected devices send all web traffic queries to malicious resolvers hosted by Aeza International, a bulletproof hosting firm previously sanctioned by the US government.
This silent redirection allows threat actors to selectively manipulate which websites users can reach, often steering them toward fraudulent advertising platforms or malicious scams.
While popular sites like Google often resolve correctly to avoid suspicion, specific targets trigger a complex redirection chain.
This involves a secondary HTTP-based Traffic Distribution System (TDS) that fingerprints the victim’s device before delivering the final payload.
Infoblox analysts this widespread campaign after connecting scattered user reports of “insane” internet behavior with anomalous DNS patterns.
They observed that the threat actors largely target older router models, fundamentally altering the trust chain for every device on the home network.
Victims reported bizarre issues, such as an inability to access Google Sheets or persistent browser redirects, often assuming their computers—not their routers—were at fault.
The EDNS0 Evasion Technique
The most technically intriguing aspect of this campaign is its stealthy evasion method. Security analysts initially struggled to replicate the malicious DNS responses because the rogue servers would not answer standard queries.
The breakthrough came when analysts discovered that the shadow resolvers only respond if the Extension Mechanisms for DNS (EDNS0) protocol is explicitly disabled.
Since EDNS0 is a standard protocol extension used by almost all modern legitimate resolvers to handle larger packet sizes and security features, standard security scanning tools automatically include it.
By configuring their servers to ignore these standard queries, the attackers effectively made their infrastructure invisible to automated scans and most security researchers.
This simple yet effective filter allowed the malicious network to operate undetected for years, serving correct IP addresses to researchers while delivering hijacked responses to actual victims using older, non-compliant equipment or specific configurations.
To mitigate this threat, users must audit router configurations for unauthorized DNS settings.
Updating router firmware to the latest versions is critical, as is replacing obsolete hardware that no longer receives security patches to prevent initial compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.