SEO Poisoning Campaign Impersonates 25+ Popular Apps to Deliver
A sophisticated SEO poisoning campaign has quietly targeted Windows users since at least October 2025. The operation lures victims into downloading trojanized installers for more than 25 popular...
A sophisticated SEO poisoning campaign has quietly targeted Windows users since at least October 2025. The operation lures victims into downloading trojanized installers for more than 25 popular software applications.
The operation went undetected for roughly five months before investigators uncovered its full scope in March 2026, revealing a multi-stage infection chain that silently compromises victims’ machines and steals sensitive data.
The campaign works by pushing fake software download pages to the top of search engine results, targeting users looking for tools like VLC Media Player, OBS Studio, KMS Tools, and CrosshairX.
When a victim clicks a download link, they receive a ZIP archive containing both the real software and a hidden malicious component, and because the legitimate application launches normally afterward, most victims notice nothing unusual.
The lure sites were built with fake Schema.org aggregate ratings and hreflang tags for multiple languages to appear credible in search results.
![Screenshot of the SEO optimisation on studio-obs[.]net (Source - NCC Group)](https://hackersradar.com/wp-content/uploads/2026/03/content_1774288833_1813.jpg)
NCC Group analysts, working alongside FOX-IT through a joint investigation triggered by a spike in ScreenConnect-related alerts across client environments, identified the campaign’s full scope in March 2026.
What initially appeared to be unrelated alerts tied to a remote management tool turned out to be a coordinated operation running quietly for months.
The supporting infrastructure spans three ScreenConnect relay hosts and two payload delivery backends, with over 100 malicious files linked to them discovered on VirusTotal at the time of analysis.
The final payload delivered by this campaign is AsyncRAT, an open-source remote access trojan first released in 2019.
This build, labeled internally as “FlowProxy Monitor V3,” goes well beyond standard RAT functionality, incorporating a keylogger, clipboard monitor, a cryptocurrency clipper covering 16 currencies, and a dynamic plugin system letting the attacker push additional capabilities into memory at runtime.
The build also includes a geo-fencing mechanism that deliberately bypasses cryptocurrency interception for victims located in the Middle East, North Africa, and Central Asia.
The delivery infrastructure has also evolved throughout the campaign’s lifespan.
Early payloads were hosted at static, predictable URLs, but by late January 2026, the operator shifted to a randomized token-based system where every download link is uniquely generated, making URL-based blocking ineffective.
The primary delivery backend, fileget[.]loseyourip[.]com, disguises itself as a file-sharing site, but exists solely to distribute malicious installers.
Multi-Stage Infection Mechanism
The infection begins the moment a victim executes the downloaded file. The ZIP archive bundles a genuine VLC installer alongside a malicious libvlc.dll.
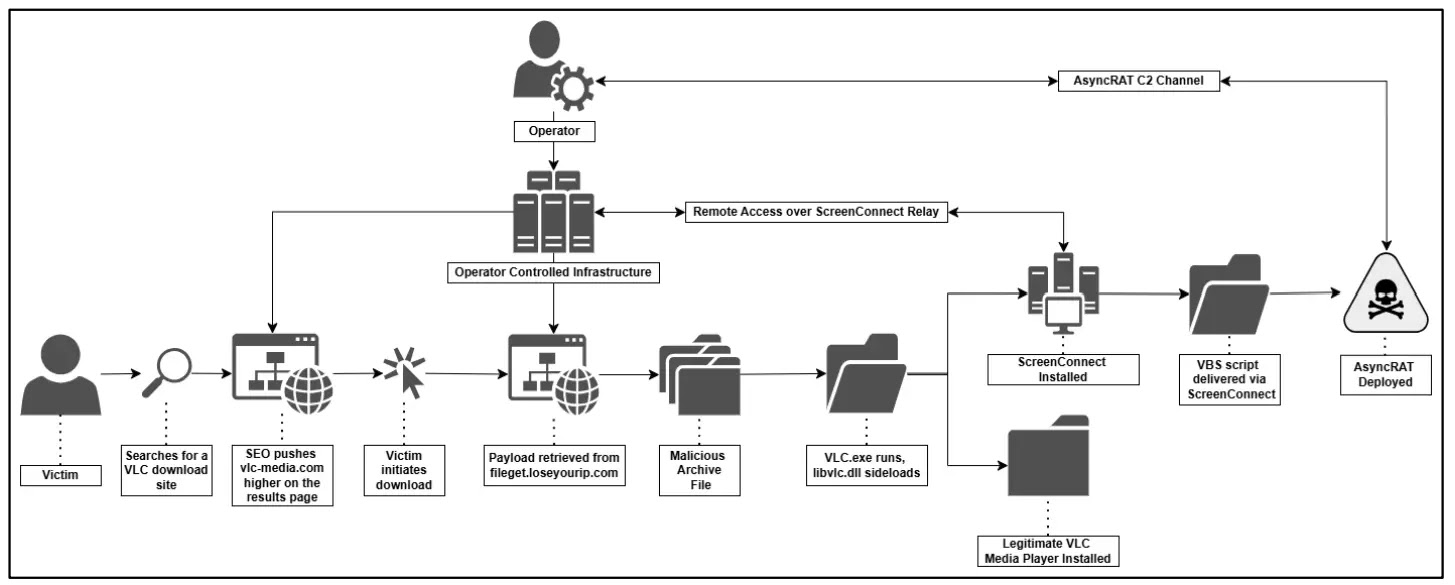
Since libvlc.dll is a core dependency of VLC, Windows loads it automatically when the program starts, running the attacker’s code under a trusted application’s process through a technique called DLL sideloading.
Once active, the DLL extracts a hidden MSI installer and runs it silently. This MSI deploys ScreenConnect as a Windows service, disguised as “Microsoft Update Service,” and immediately reaches out to the attacker’s relay server.
The attacker then uses ScreenConnect to drop a VBScript that writes a PowerShell loader and encoded payload files into C:UsersPublic.
The loader decrypts these files using XOR operations and bit reflection, then compiles a .NET injector entirely in memory, which performs process hollowing to inject AsyncRAT into RegAsm.exe — a legitimate Windows binary — leaving no file on disk for security tools to scan.
To survive reboots and locked sessions, the campaign establishes three persistence mechanisms: a Windows service configured to start automatically, a Windows Authentication Package that loads into LSASS before any user logs in, and a scheduled task named “MasterPackager.Updater” that re-executes the VBScript every two minutes.
Users should always download software directly from official vendor websites and treat unexpected elevation prompts during installation as a warning.
Security teams should monitor for unauthorized ScreenConnect deployments, process hollowing events in RegAsm.exe, and the mutex “confing_me_s” as host-based indicators.
Blocking confirmed lure domains, relay hosts, and AsyncRAT C2 addresses from the indicators of compromise is strongly advised.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.