North Korean Hackers Exploit Code Abuse in ‘Cont Tactics Interview’
North Korean threat actors are deploying a sophisticated social engineering campaign, specifically targeting software developers with deceptive recruitment offers. The campaign, known as Contagious...
North Korean threat actors are deploying a sophisticated social engineering campaign, specifically targeting software developers with deceptive recruitment offers.
The campaign, known as Contagious Interview, uses malicious repositories disguised as technical assessment projects to deploy a dual-layer malware system.
Victims are lured through LinkedIn messages from fake recruiters claiming to represent organizations like Meta2140, then directed to download repositories containing hidden malicious code.
The attack operates through a carefully crafted two-stage infection process designed to steal credentials, cryptocurrency wallets, and establish persistent remote access on victim systems.
The malware employs multiple infection vectors, with the most dangerous being a hidden VS Code tasks configuration.
When developers open the project folder to review code or enable AI-assisted inspection, a concealed task automatically executes without requiring direct code execution.
A second vector uses application logic hooks embedded in the server code, where legitimate-looking functions trigger payload download and execution.
If both fail, the attack attempts to install a malicious npm dependency. These methods ensure successful infection even when victims practice caution by avoiding direct code execution.
Security researchers at SEAL Intel identified and analyzed the campaign after three separate victims sought help within a single month.

All victims experienced the same attack pattern and reported significant financial losses.
By examining commit history and metadata, researchers discovered the malware originates from known North Korean IT workers who previously operated fraudulent projects like Ultra-X.
Commit timestamps consistently showed Korean Standard Time zone settings, further confirming attribution.
Infection mechanism
The infection mechanism works in distinct stages. When triggered, the malware downloads a Node.js controller that executes entirely in system memory.
This controller deploys five specialized modules to steal sensitive data. The keylogger and screenshot module monitors user activity and uploads results to the attacker’s command server at 172.86.116.178.
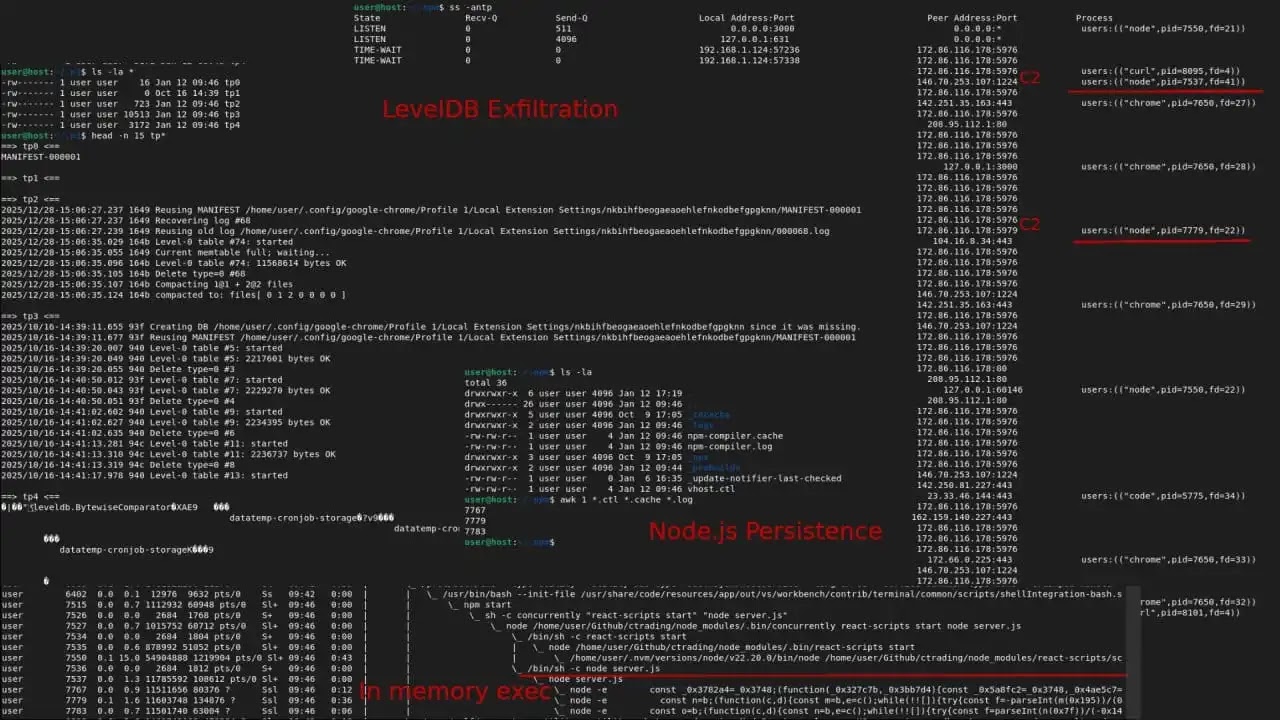
A file grabber scans the home directory for configuration files, secrets, and SSH keys. The clipboard monitor watches for cryptocurrency addresses, while the browser stealer targets Chrome, Brave, and Opera databases containing login credentials and wallet information.
Finally, a remote access tool connects to the attacker’s command center using socket.io, allowing arbitrary shell command execution.
Following the Node.js stage, the malware deploys Python payloads that establish stronger persistence. On Windows systems specifically, the malware creates startup folder injections and scheduled tasks mimicking legitimate Windows processes like RuntimeBroker.exe.
The miner module downloads XMRig cryptocurrency mining software. Throughout execution, the malware creates hidden directories in .npm and system folders to stage stolen data and maintain infection foothold across reboots.
Developers should immediately disable automatic VS Code task execution and enable workspace trust verification.
Systems showing infection signs including hidden .n2, .n3, or .npm directories require full credential rotation and cryptocurrency wallet migration to new addresses from clean devices.
Windows systems suffering infection warrant complete operating system reinstallation due to registry-level persistence mechanisms.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.