DragonForce Ransomware Decryptor Released for ESXi
DragonForce ransomware has completed its shift from activity observed on underground forums to a full Ransomware-as-a-Service (RaaS) model. It now targets both Windows and VMware ESXi environments....
DragonForce ransomware has completed its shift from activity observed on underground forums to a full Ransomware-as-a-Service (RaaS) model. It now targets both Windows and VMware ESXi environments.
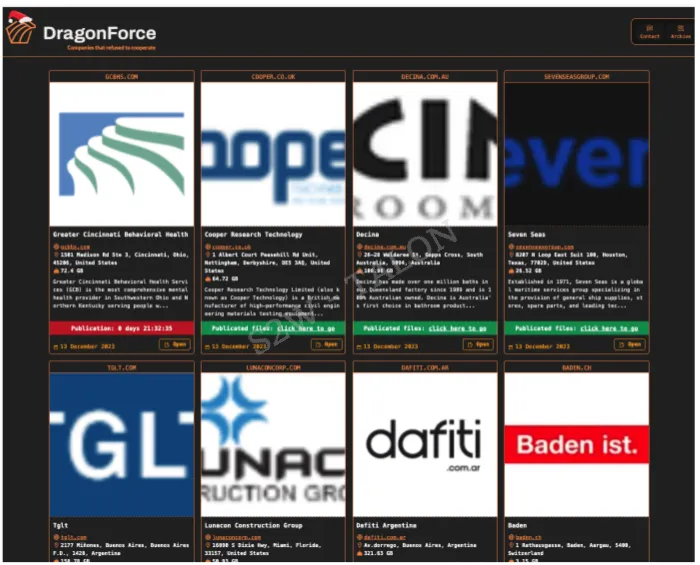
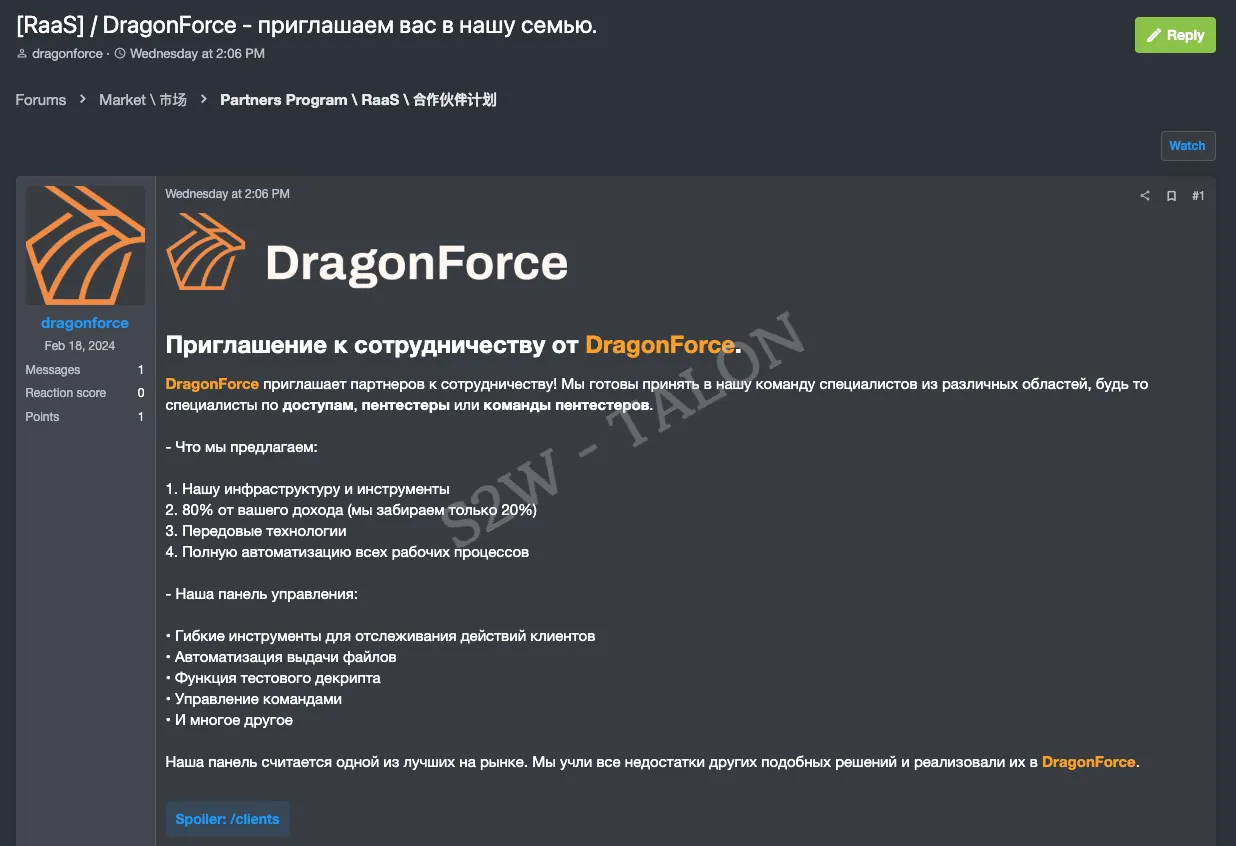
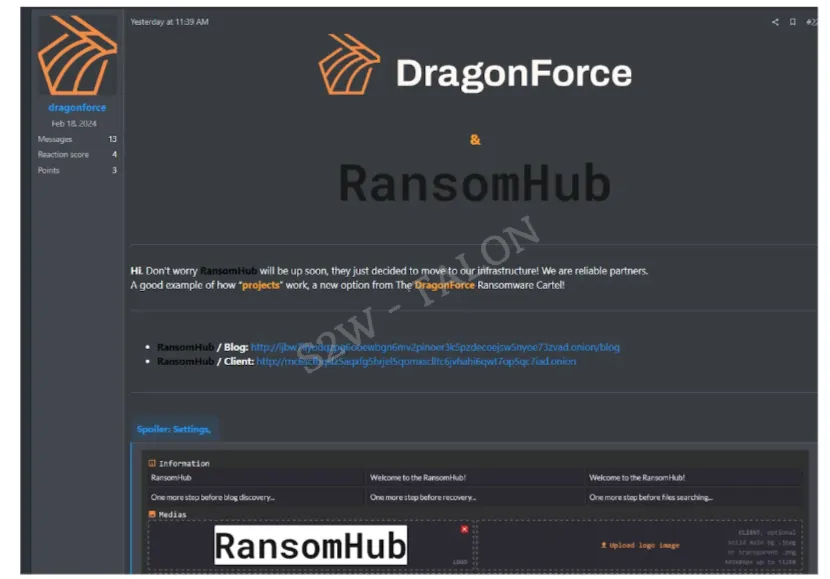
First seen in December 2023 on BreachForums, the group advertises stolen data and uses a dark web blog to pressure victims. The early leak post revealed the new cartel-style operation.
The group built its payload from leaked LockBit 3.0 and Conti code, but tuned it for flexible, high-speed encryption across local disks and network shares.
Operators usually gain access through exposed remote desktop servers, then use tools like Cobalt Strike and SystemBC to move laterally before launching the ransomware. Impact ranges from encrypted file servers and virtual machines to stolen data prepared for public release.

S2W analysts identified a custom DragonForce build that hides nearly all strings with a home-grown deobfuscation routine and relies on ChaCha8 plus RSA-4096 for file encryption.
Their research shows that command-line flags let affiliates choose local, network-only, or mixed modes, and even tune partial encryption ratios to speed up attacks. While its DLS shows the internal workflow from configuration decryption to process killing and file scrambling.
During wider threat hunting, S2W researchers obtained a working decryptor for both Windows and ESXi systems, giving some victims a path to recovery without paying ransom.
The Windows tool looks for files with the .RNP extension, while the ESXi version checks for .RNP_esxi files that also end with a specific eight-byte magic value called build_key. Besides this it maps the full decryption chain from RSA key loading to metadata parsing and file restoration.
This complete technical breakdown gives defenders insight into DragonForce tools and recovery options.
Encryption and Decryption Workflow
On execution, the ransomware first decrypts its internal configuration using ChaCha8, then reads options such as encryption mode and target path.
A common command seen by S2W analysts is dragonforce.exe -m net -p C:\ -j 8, which tells the malware to hit network targets under that path with multiple worker threads.
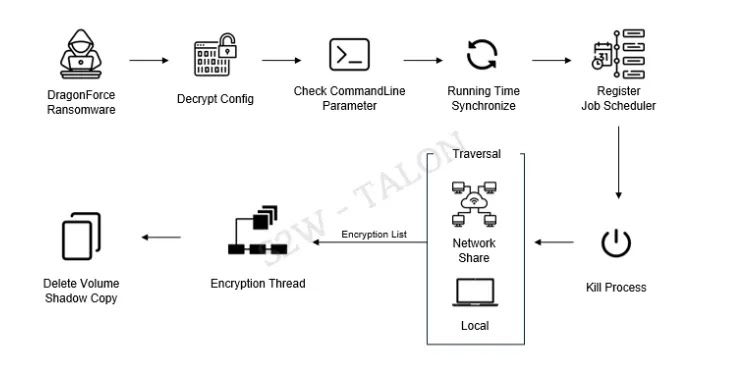
As it scans local and remote paths, DragonForce skips core system areas, then encrypts chosen files. For big virtual disk images it encrypts only chunks instead of the whole file to save time.
At the end of each file it writes 534 bytes of metadata with an RSA-encrypted ChaCha8 key and nonce plus flags that store mode, ratio, and original size.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.