nmapUnleashed Makes Nmap Scanning More Comfortable and Effective
nmapUnleashed is a new, powerful command-line interface (CLI) wrapper designed to enhance Nmap’s capabilities for penetration testers and network auditors. Released in late January 2026 by...
nmapUnleashed is a new, powerful command-line interface (CLI) wrapper designed to enhance Nmap’s capabilities for penetration testers and network auditors.
Released in late January 2026 by developer Sharkeonix, this open-source tool streamlines complex scans while retaining full Nmap compatibility.
nmapUnleashed, or “nu,” wraps Nmap to add multithreading, allowing up to customizable parallel scans (default 4 threads) for faster execution across large networks.
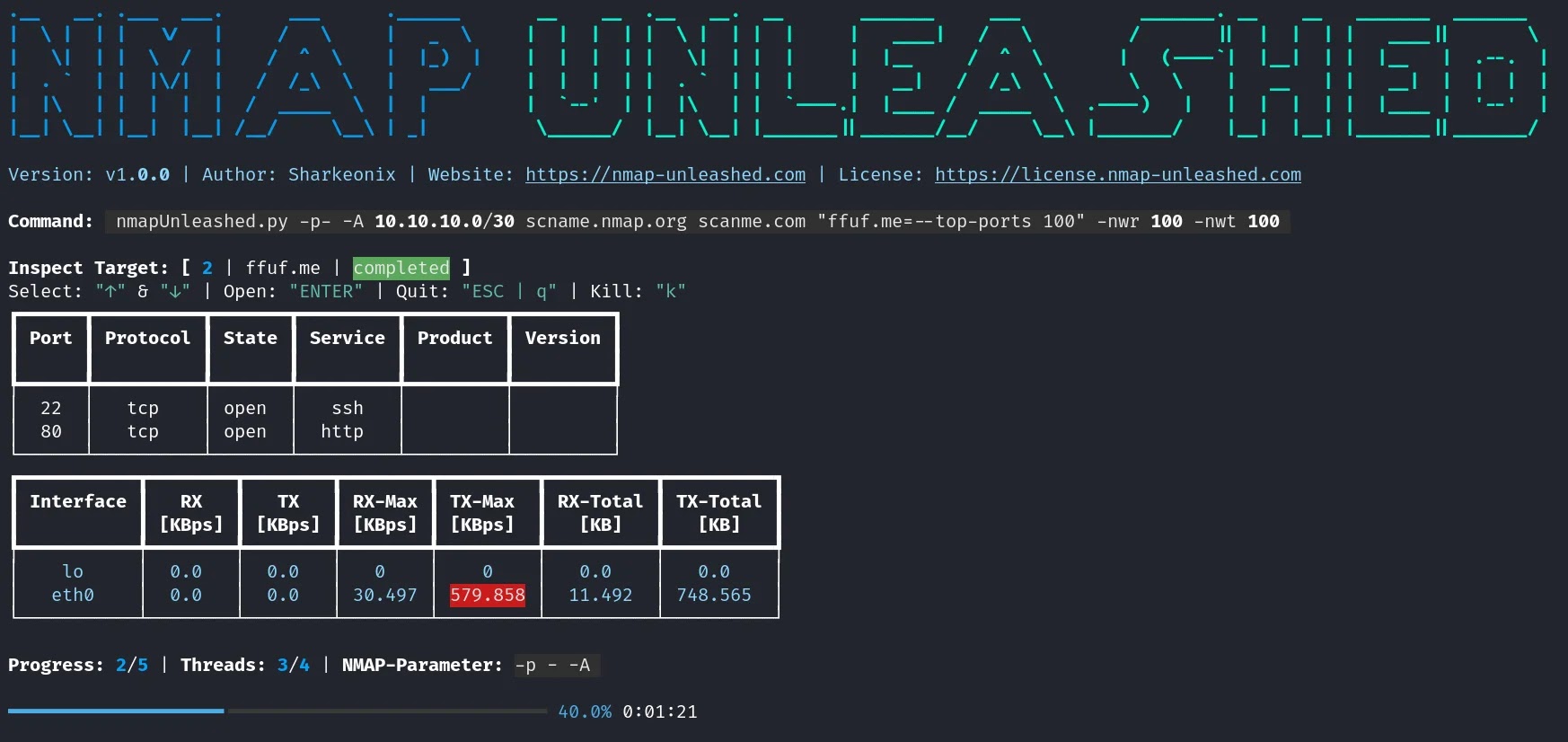
It introduces a persistent dashboard for real-time monitoring of queued, active, aborted, and completed scans, complete with network throughput warnings to prevent bandwidth overload.
Users benefit from automatic timeouts, manual abort options, and merged outputs like scans.xml and scans.html for easy post-analysis.
The tool excels in target specification, supporting IPs, CIDRs, hostnames, and files, with syntax for per-target Nmap parameters like “10.10.1.0/24=–top-ports 100 -A“.
Exclusions via -ex flag refine scopes, while presets (-ps) load predefined scan profiles from config files, speeding up repetitive tasks. For instance, a “basic” preset might run “-d -p- -A,” ideal for comprehensive port and version detection.
Dashboard and Monitoring
A standout feature is the interactive dashboard, displaying live progress, network receive/transmit rates (with thresholds like -nwr 1000), and scan navigation via arrow keys. Post-scan, dashboard.txt summarizes all activities, aiding audits.
Live results show ports during scans, with full service/version details afterward. Options like -fs fix dashboard size for stable viewing in terminals.
| Option | Purpose | Default |
|---|---|---|
| -th | Threads for parallel scans | 4 |
| -kt | Auto-abort timeout (minutes) | None |
| -nwr/-nwt | Network warning thresholds (KBps) | 0 (disabled) |
| -ko | Keep offline target files | False |
| -ps | Load parameter preset | None |
Installation is straightforward on Linux (e.g., Kali): ensure nmap, xsltproc, grep, then pipx install git+https://github.com/Sharkeonix/nmap-unleashed.git. Basic usage mirrors Nmap: “nu -d -p- -A scanme.nmap.org” for aggressive scanning.
Advanced example: “nu -th 8 -kt 120 -nwr 1000 -p- -sV scanme.nmap.org” launches 8 threads, aborts after 120 minutes, warns at 1000 KBps incoming. Output controls include -os for only merged files or -rf “xml;html” to cleanup specifics.
As pentesting demands efficiency amid rising threats, nmapUnleashed positions itself as an essential upgrade, blending familiarity with productivity boosts.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.