New VECT 2.0 Ransomware Destroys Files Over 128 KB Across Windows,
The cybersecurity community is closely monitoring a new ransomware strain named VECT 2.0. This variant isn’t just encrypting files; it’s designed with a critical flaw that causes...
The cybersecurity community is closely monitoring a new ransomware strain named VECT 2.0. This variant isn’t just encrypting files; it’s designed with a critical flaw that causes permanent data destruction. Specifically, it destroys any file larger than 128 KB across compromised Windows systems. Its highly damaging operational method represents a concerning evolution in ransomware attacks.
Unlike typical ransomware that locks files and demands payment for decryption, VECT 2.0 permanently destroys any file larger than 128 KB, making recovery impossible even if a victim pays the ransom.
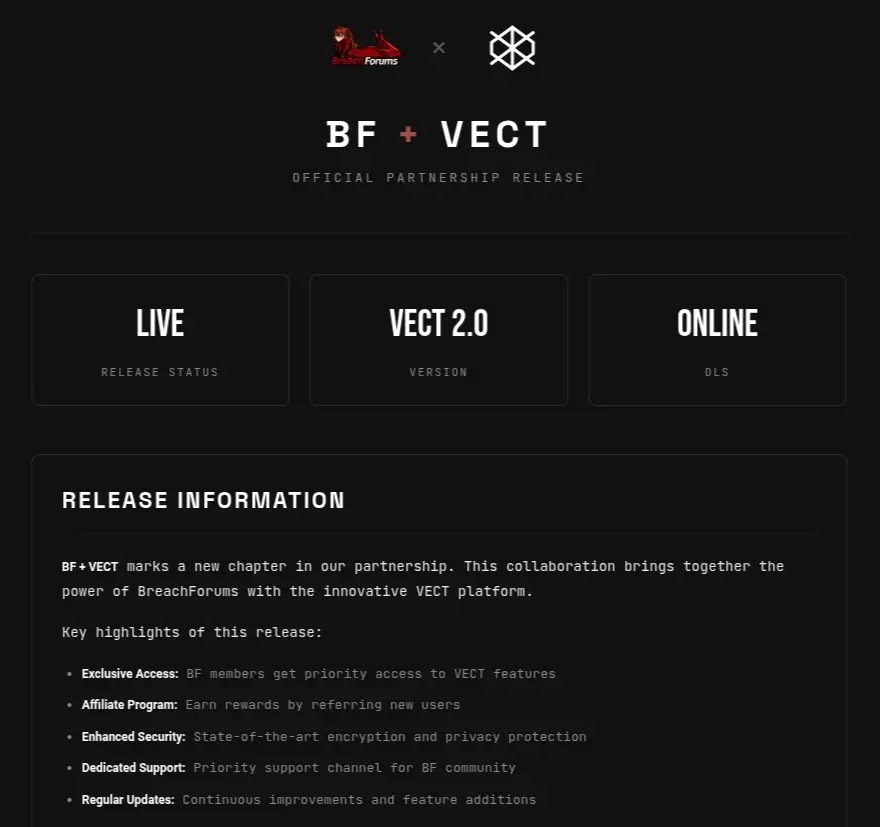
VECT Ransomware first appeared in December 2025 on a Russian-language cybercrime forum, operating as a Ransomware-as-a-Service (RaaS) program.
The group claimed its first two victims in January 2026 and released version 2.0 in February 2026, expanding its reach across Windows, Linux, and VMware ESXi systems.
The malware gained more visibility in March 2026 when VECT announced a partnership with TeamPCP, a threat actor behind supply-chain attacks that injected malware into widely-used packages including Trivy, Checkmarx KICS, LiteLLM, and Telnyx, affecting a large number of downstream users.
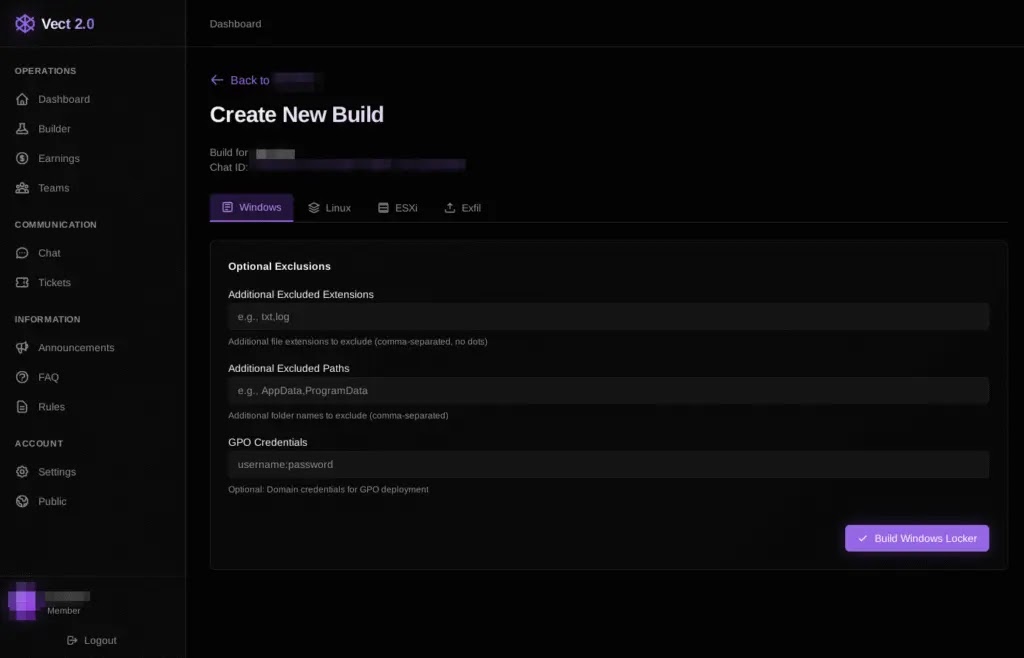
Check Point Research analysts identified and analyzed all three VECT 2.0 variants after gaining access to the builder panel through a BreachForums account.
Their investigation uncovered that VECT also entered a partnership with BreachForums itself, giving every registered forum member free access to deploy the ransomware as an affiliate.
This open-affiliate model removes the usual vetting process, significantly lowering the barrier for less experienced attackers to join the operation.
The ransomware is written in C++ and targets all three platforms through statically compiled executables that share a common codebase.
Each variant uses the ChaCha20-IETF (RFC 8439) cipher via the libsodium cryptographic library and renames encrypted files with the .vect extension, dropping a ransom note named !!!READ_ME!!!.txt on each compromised system.
Despite its polished builder panel, the technical execution falls well short of a professionally developed ransomware tool.
The most alarming aspect of VECT 2.0 is a critical coding flaw that effectively turns it into a data wiper.
Any file exceeding 131,072 bytes (128 KB) is not properly encrypted but instead rendered permanently unrecoverable, targeting the very assets organizations depend on to keep operations running.
The Nonce-Handling Flaw That Destroys Large Files
At the heart of the problem is a fundamental error in how VECT 2.0 handles cryptographic nonces during file encryption.
When the malware processes a large file, it divides it into four chunks and encrypts each one using a freshly generated, random 12-byte nonce.
All four encryption calls write their nonces into the same shared memory buffer, meaning each new nonce overwrites the previous one.
By the time encryption finishes, only the nonce from the fourth and final chunk survives and gets written to the encrypted file on disk.
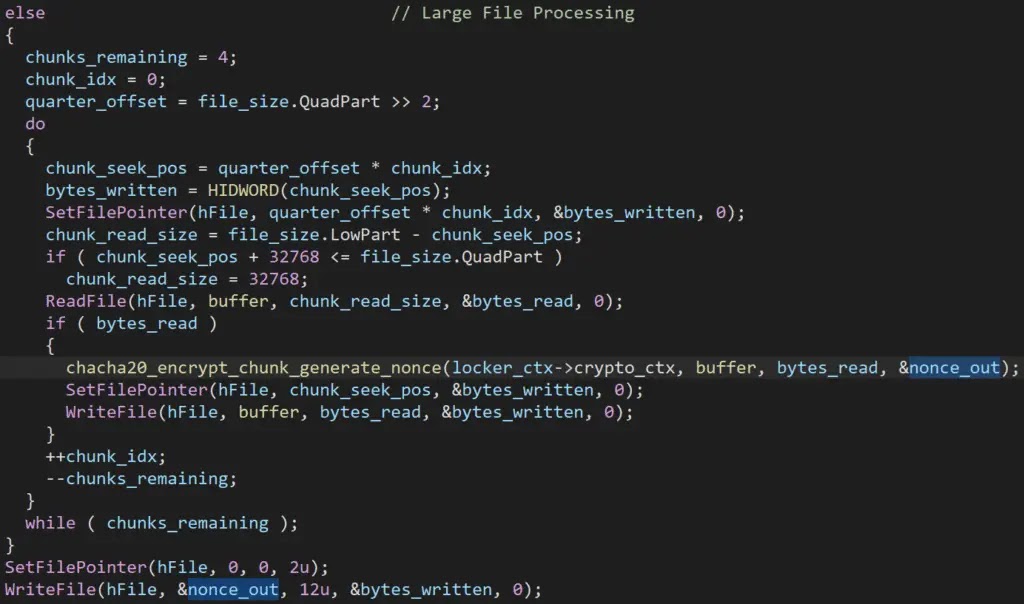
Since ChaCha20-IETF decryption requires both the encryption key and the exact matching nonce to reverse each chunk, the first three quarters of every large file are unrecoverable by anyone.
The discarded nonces are never saved on disk, stored in the registry, or sent to the attacker’s server in any of the three variants. Even if a victim pays the ransom in full, the operator cannot provide a working decryptor because the nonces required for decryption were permanently lost the moment the buffer was overwritten.
At just 128 KB, this threshold captures virtually every meaningful file type, from VM disk images and databases to backups, spreadsheets, and email archives.
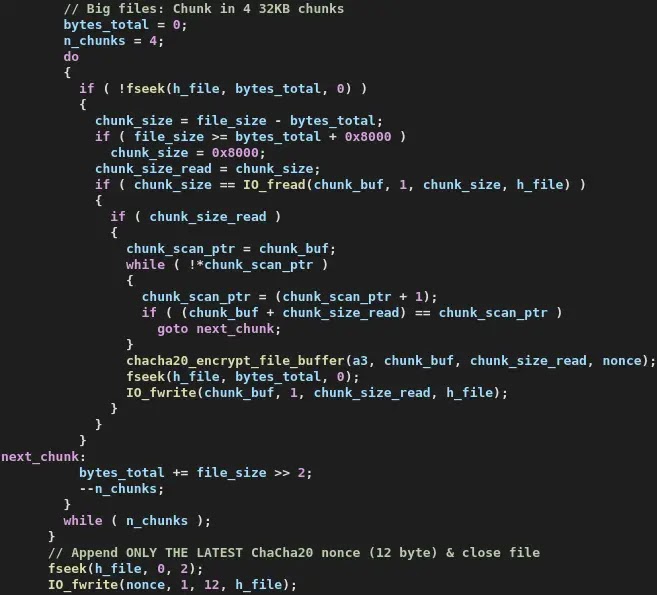
Check Point Research confirmed this flaw is present in all three platform variants and predates the 2.0 release, having existed in earlier deployments without ever being fixed.
Organizations should keep offline, air-gapped backups that cannot be reached through network shares or lateral movement.
Monitoring for bulk process terminations, sudden shadow copy deletions, and mass file renaming to the .vect extension can provide early warning of an active infection.
Given VECT’s partnership with TeamPCP, validating the integrity of third-party software dependencies is also a critical step.
Security teams should watch for PowerShell-based disabling of Windows Defender, event log clearing activity, and unusual safe-mode boot configuration changes, all of which are key behavioral indicators of this ransomware.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.