New Payouts King Ransomware Threat Linked to Black
Payouts King, a relatively unknown ransomware group, has emerged as a serious cybersecurity threat, succeeding the now-defunct BlackBasta operation. Since its appearance in April 2025, the group has...
Payouts King, a relatively unknown ransomware group, has emerged as a serious cybersecurity threat, succeeding the now-defunct BlackBasta operation.
Since its appearance in April 2025, the group has quietly carried out targeted attacks while remaining largely under the radar, combining aggressive data theft with selective file encryption.
BlackBasta was one of the most active ransomware groups since it launched in February 2022 as a successor to the notorious Conti ransomware gang.
The group operated for nearly three years before it collapsed in February 2025 when its internal chat logs were publicly leaked, exposing its members and inner workings.
Following BlackBasta’s shutdown, its former affiliates did not simply disappear. Instead, they regrouped and continued their criminal activities under different ransomware families, including Cactus, and more recently, Payouts King.
Zscaler ThreatLabz analysts identified ransomware activity consistent with prior BlackBasta initial access brokers starting in early 2026, and have attributed several of those attacks to the Payouts King ransomware group with high confidence.
The researchers noted that many of these attacks closely mirror the same techniques, tactics, and procedures used by BlackBasta affiliates, particularly the combination of spam bombing, Microsoft Teams-based social engineering, and the abuse of the legitimate Windows tool Quick Assist.
Victims are typically flooded with spam emails, then contacted by a threat actor impersonating an IT staff member, and tricked into granting remote access through a Microsoft Teams call.
Once a foothold is established on the victim’s network, Payouts King deploys its ransomware payload, steals large volumes of sensitive data, and then selectively encrypts files.
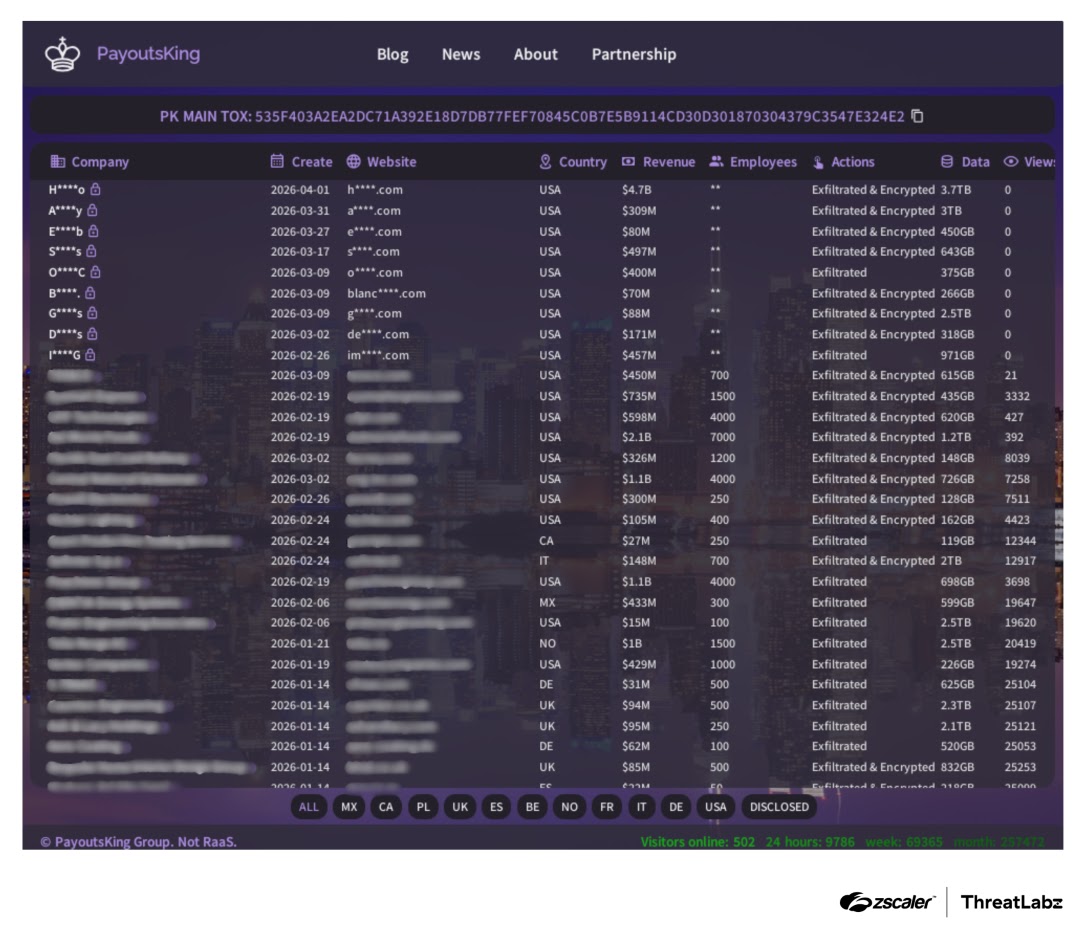
The group operates a data leak site accessible via the Tor network, which is used to pressure victims into paying by threatening to release their stolen information.
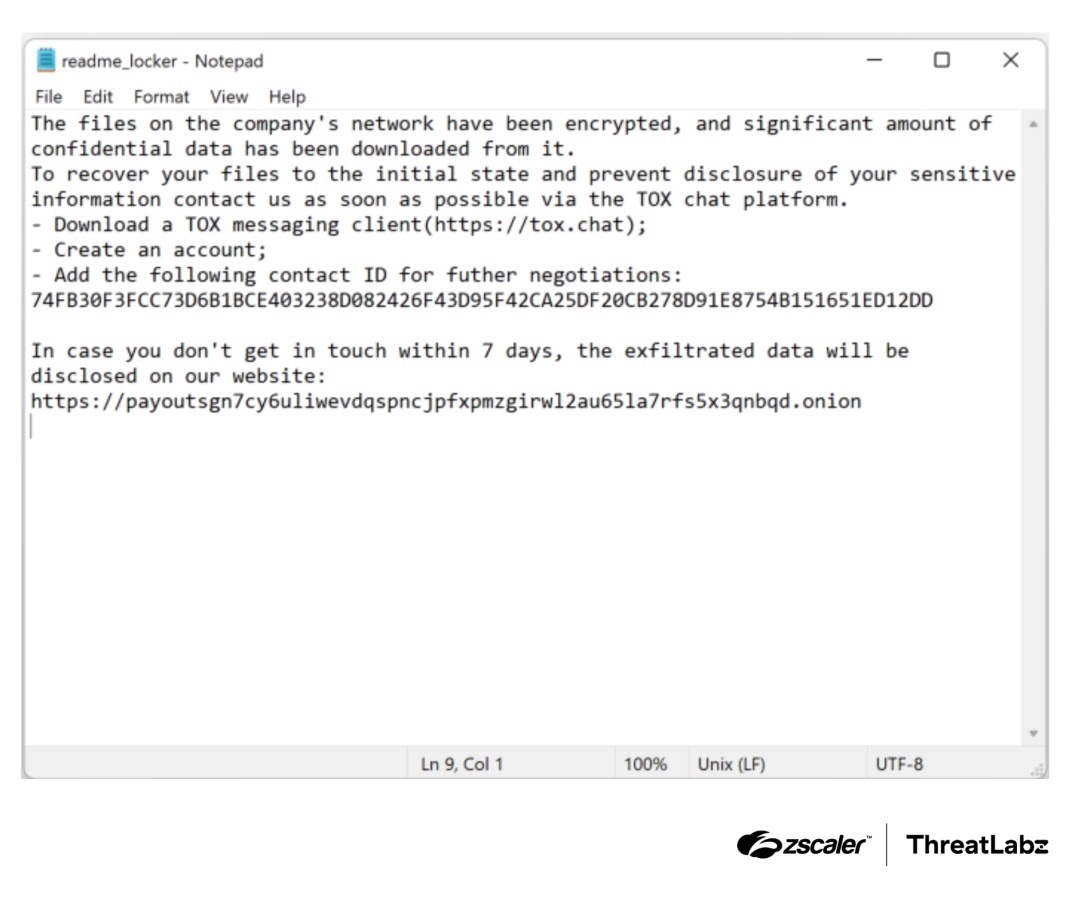
The ransom note, named “readme_locker.txt,” is dropped on the victim’s desktop and provides contact instructions through the TOX messaging platform.
The ransomware itself is technically sophisticated, using 4,096-bit RSA and 256-bit AES encryption in counter mode to lock victim files.
Each file is encrypted using a pseudorandomly generated key and initialization vector, and the encryption parameters are stored in a structured 487-byte format that begins with the magic bytes “CRPT”.
For large files exceeding 10MB, Payouts King divides the file into 13 blocks and only partially encrypts each block, a common performance optimization seen in modern ransomware to speed up the attack.
How Payouts King Avoids Detection
Payouts King is designed from the ground up to evade security tools. It employs several obfuscation methods including stack-based string encryption, Windows API function resolution through hashing, and a custom CRC checksum algorithm with a polynomial value of 0xBDC65592.
These methods defeat precomputed hash tables commonly used by security analysts to reverse-engineer malware quickly, making static analysis considerably more difficult.
The ransomware also uses a unique anti-sandbox mechanism. By default, it refuses to begin file encryption unless a specific identity parameter is passed on the command line, and the CRC checksum of that value must match an expected result.
This effectively prevents the malware from running in automated sandbox environments used by antivirus vendors.
To further frustrate endpoint security tools, Payouts King uses low-level direct system calls instead of standard Windows API calls when terminating running security processes.
It builds a runtime table of system call numbers by walking the ntdll module’s export table, targeting processes belonging to a hardcoded list of 131 antivirus and EDR applications.
After file encryption is complete, the ransomware deletes Windows shadow copies, clears the recycle bin, and wipes Windows event logs to hinder forensic investigation.
To defend against Payouts King and similar threats, organizations should train employees to recognize social engineering tactics like spam bombing and fake IT support calls.
Enforcing multi-factor authentication, restricting the use of remote access tools like Quick Assist to verified IT personnel only, and deploying behavior-based endpoint detection are also strongly recommended.
Proactive threat hunting combined with continuous updates to security controls remains essential in keeping pace with ransomware groups that continuously adapt their methods.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.